Network Security
Application Security
Cloud Security
AES encryption, BitLocker, cybersecurity, data encryption, data privacy, data protection, digital privacy, encryption, end-to-end encryption, file encryption, FileVault, internet safety, online security, password security, PGP, VPN
Rahul Chandak
0 Comments
What Is Data Encryption and How to Start Using It Today
In today’s digital world, protecting your information is more crucial than ever. Data encryption is a key method to keep your personal and professional data safe from unauthorized access. Whether you’re sending an email, storing files on your computer, or making online purchases, data encryption plays a vital role in securing that information. This blog post will explain what data encryption is, why it matters, and how you can begin using it right away. We’ll break it down into simple & easy terms so anyone can understand and apply it.
Data encryption is essentially the process of converting readable data into a coded format that can only be accessed by those who have the right key to decode it. Think of it like locking a treasure chest – only the person with the matching key can open it and see what’s inside. Without the key, the contents remain a mystery. This technique has been around for centuries but has evolved dramatically with technology.
As we discuss deeper, you’ll learn about different types of data encryption, how it functions behind the scenes, its history, benefits, common applications, and practical steps to implement it in your daily life. By the end, you’ll feel confident in using data encryption to safeguard your data.

Image credit: What Is Encryption? Explanation and Types – Cisco
Why Is Data Encryption Important?
Data encryption is important because it protects sensitive information from falling into the wrong hands. In an era where cyber threats are rampant, such as hacking, phishing, and data breaches, encryption acts as a shield. For instance, if a hacker intercepts your data during transmission, without encryption, they could easily read it. But with data encryption, it appears as gibberish, making it useless to them.
Consider the massive data breaches that have made headlines in recent years. Companies like Equifax and Yahoo have suffered attacks where millions of users’ personal details were exposed. If stronger data encryption had been in place, the impact could have been minimized. Governments and businesses mandate data encryption for compliance with laws like GDPR in Europe or HIPAA in the US, which require protecting personal data.
On a personal level, data encryption prevents identity theft. When you bank online or share medical records, encryption ensures that your details stay private. It’s not just for big corporations; everyday users benefit too. For example, using encrypted messaging apps like Signal keeps your conversations confidential.
Moreover, data encryption builds trust. When customers know their data is encrypted, they’re more likely to engage with services. In e-commerce, sites using HTTPS (which involves encryption) see higher conversion rates because users feel secure entering credit card information.
Without data encryption, risks include financial loss, reputational damage, and legal consequences. Cybercriminals can exploit unencrypted data for fraud or ransomware. By understanding its importance, you can take proactive steps to protect yourself.
Data encryption also supports privacy rights. In a surveillance-heavy world, it empowers individuals to control their information. Activists, journalists, and whistleblowers rely on it to communicate safely.
In summary, data encryption is essential for security, compliance, trust, and privacy. Ignoring it is like leaving your front door unlocked in a busy city.
Types of Data Encryption
There are several types of data encryption, each suited for different purposes. The two main categories are symmetric and asymmetric encryption.
Symmetric encryption uses a single key for both encrypting and decrypting data. It’s fast and efficient for large amounts of data. Common algorithms include AES (Advanced Encryption Standard), which is widely used in file encryption and Wi-Fi security. Imagine symmetric encryption as a shared secret key between friends – both use the same key to lock and unlock messages.
Asymmetric encryption, also known as public-key encryption, uses two keys: a public key for encryption and a private key for decryption. This is ideal for secure communications over the internet, like in SSL/TLS for websites. RSA is a popular asymmetric algorithm. Think of it as a mailbox: anyone can drop a letter in (using the public key), but only the owner can open it (with the private key).
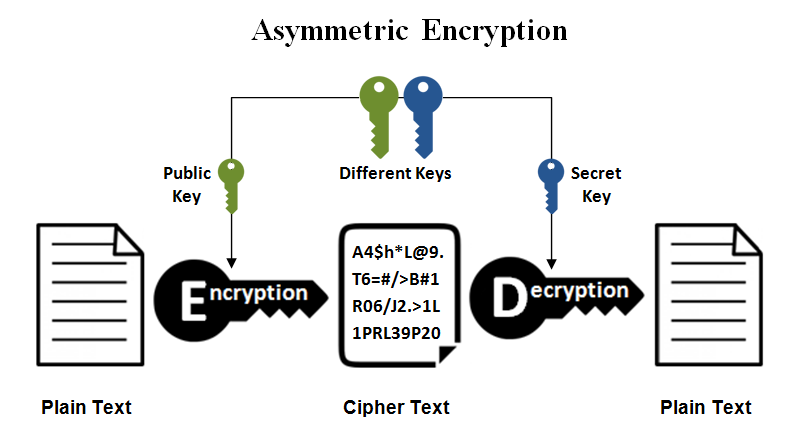
Image credit: Symmetric vs. Asymmetric Encryption – What are differences? from https://www.ssl2buy.com/wiki/symmetric-vs-asymmetric-encryption-what-are-differences
Another type is hashing, which is a one-way encryption used for verifying data integrity, like in passwords. It turns data into a fixed-size string that can’t be reversed. SHA-256 is common here.
Data encryption can also be classified by what it protects: at-rest encryption for stored data (like on hard drives), in-transit for data moving over networks (like emails), and in-use for data being processed.
Full-disk encryption protects entire devices, while file-level encryption targets specific files. End-to-end encryption ensures data is secure from sender to receiver, as in WhatsApp.
Hybrid encryption combines symmetric and asymmetric methods for efficiency and security. For example, PGP (Pretty Good Privacy) uses this for email encryption.
Understanding these types helps you choose the right one. For personal use, start with symmetric for files and asymmetric for online transactions.
Each type has strengths: symmetric is speedy, asymmetric is secure for key exchange. Drawbacks include key management in symmetric and computational overhead in asymmetric.
In practice, most systems use a mix. When you visit a secure website, asymmetric handles the handshake, then symmetric takes over for data transfer.
How Data Encryption Works
Data encryption works by applying mathematical algorithms to transform plain text into cipher text. The process involves keys, which are strings of bits used by the algorithm.
First, the encryption algorithm takes the original data (plaintext) and the key, then scrambles it into unreadable form (ciphertext). Decryption reverses this using the key to get back the plaintext.
For symmetric encryption, the same key is used. An example: AES-256 uses a 256-bit key and multiple rounds of substitution and permutation to encrypt blocks of data.
In asymmetric, the public key encrypts, private decrypts. It relies on complex math like prime factorization in RSA.
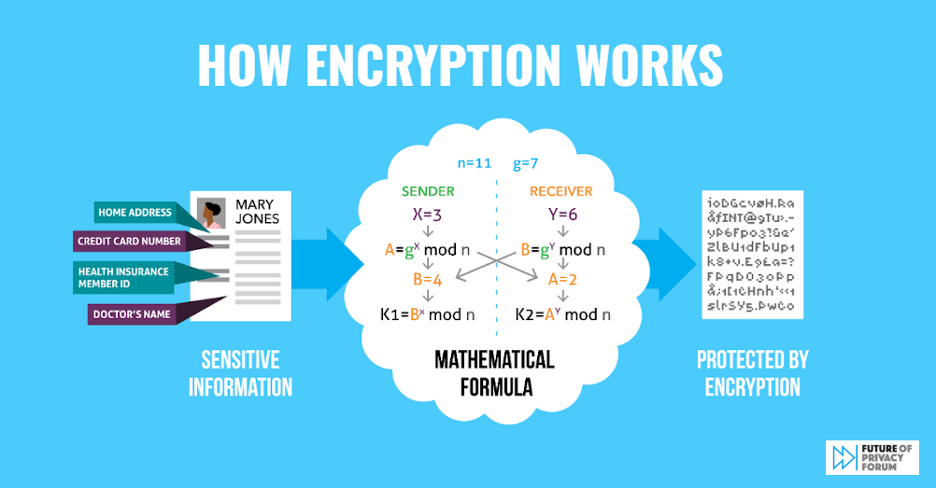
Image credit: Strong Data Encryption Protects Everyone: FPF Infographic Details … from https://fpf.org/blog/strong-data-encryption-protects-everyone-fpf-infographic-details-encryption-benefits-for-individuals-enterprises-and-government-officials/
Keys are generated securely, often using random number generators. Key length affects strength – longer keys are harder to crack.
Encryption can be stream or block cipher. Stream encrypts bit by bit, good for real-time data; block handles fixed-size chunks.
In practice, when you send an encrypted email, the software applies the algorithm, sends the ciphertext, and the recipient’s software decrypts it.
Security depends on the algorithm’s strength and key secrecy. Brute-force attacks try all keys, but with long keys, it’s impractical.
Modern encryption is quantum-resistant in some cases, but that’s advanced.
Overall, data encryption works like a puzzle: the algorithm jumbles pieces, key reassembles them.
The History of Data Encryption
Data encryption has a rich history dating back to ancient times. The Egyptians used hieroglyphs for secret messages around 1900 BC.
In ancient Rome, Julius Caesar employed the Caesar cipher, shifting letters by a fixed number.
During the Renaissance, the Vigenère cipher improved on this with a keyword.
In the 20th century, the Enigma machine used by Germany in WWII was a mechanical encryption device. Alan Turing’s work in breaking it advanced computing.
The 1970s saw the Data Encryption Standard (DES) developed by IBM and adopted by the US government.
In 1976, Diffie and Hellman introduced public-key cryptography, revolutionizing the field.
RSA algorithm in 1977 enabled asymmetric encryption.
The 1990s brought PGP for email, and AES replaced DES in 2001.
With the internet boom, SSL/TLS became standard for web security.
Today, quantum cryptography is emerging.
This history shows data encryption evolving from simple shifts to complex algorithms, driven by needs for secrecy in war, business, and daily life.
Benefits of Data Encryption
- The benefits of data encryption are numerous. Primarily, it enhances security by protecting against unauthorized access.
- It ensures confidentiality, integrity, and authenticity of data.
- Compliance with regulations is easier, avoiding fines.
- It prevents data loss impacts in breaches.
- Builds customer trust, leading to better business.
- Reduces risks of identity theft and fraud.
- Supports secure remote work and cloud storage.
- In healthcare, it protects patient records; in finance, transactions.
- Overall, data encryption provides peace of mind.
Common Uses of Data Encryption
- Data encryption is used in many areas. In online banking, it secures transactions.
- Email services like Gmail use it for protection.
- VPNs encrypt internet traffic to hide activity.

Image credit: How does a VPN work | Blog | Adroit Information Technology Academy … from https://www.adroitacademy.com/blog/How-does-a-VPN-work
- Cloud storage like Dropbox encrypts files.
- Smartphones use it for device protection.
- IoT devices encrypt communications.
- Governments use it for classified info.
- Businesses for intellectual property.
- Personal uses include encrypted messaging and file vaults.
How to Start Using Data Encryption Today
Starting with data encryption is straightforward. First, enable device encryption: On Windows, use BitLocker; on Mac, FileVault.
For files, use tools like VeraCrypt for cross-platform encryption.
For emails, use PGP with Thunderbird or ProtonMail.
Install a VPN like ExpressVPN for browsing.
Use password managers like LastPass, which encrypt credentials.
Enable HTTPS on your website if you have one.
For mobile, use encrypted apps.
Back up keys securely.
Start small: Encrypt your hard drive.

Practice with free tools.
Tools and Software for Data Encryption
- Popular tools include AES Crypt for files, AxCrypt.
- For full disk: BitLocker, FileVault, LUKS on Linux.
- VPNs: NordVPN, Surfshark.
- Messaging: Signal, Telegram (secret chats).
- Browsers: Use extensions like HTTPS Everywhere.
- Cloud: Encrypted options from Google Drive.
- Open-source: GnuPG.
- Choose based on needs.
Best Practices for Data Encryption
- Use strong keys and change them regularly.
- Implement multi-factor authentication.
- Keep software updated.
- Train on phishing avoidance.
- Use encryption everywhere possible.
- Monitor for breaches.
- Have a key management policy.
Challenges and Limitations of Data Encryption
- Challenges include performance overhead, key loss leading to data inaccessibility.
- Complexity in management.
- Not foolproof against all attacks, like side-channel.
- Regulatory issues in some countries.
- Quantum computing threats.
- But benefits outweigh.
The Future of Data Encryption
The future involves post-quantum cryptography to resist quantum attacks.
Homomorphic encryption for computing on encrypted data.
Blockchain integration for secure transactions.
AI to enhance key generation.
Wider adoption in IoT.

Image credit: Y2Q Will Be Here Sooner Than You Think from https://cybersecurityventures.com/quantropi-on-y2q/
Stay updated as tech evolves.
Conclusion
Data encryption is a powerful tool for protecting your information. From understanding basics to implementing it, you can start today. Embrace data encryption for a safer digital life.
Share this content:














Post Comment