Cyber Capability Benchmarking
Businesses and organizations face constant risks from cyber attacks. Whether it's a small company or…
Ransomware Kill Chain Disruption
Ransomware attacks have become a nightmare for businesses and individuals alike. These sneaky cyber threats…
Non-Human Identity Federation
In the fast-paced world of technology, businesses rely more on machines, software, and devices to…
Prompt Engineering for Defense
Cybercriminals don't always need fancy hacking tools to break into systems. Often, they just trick…
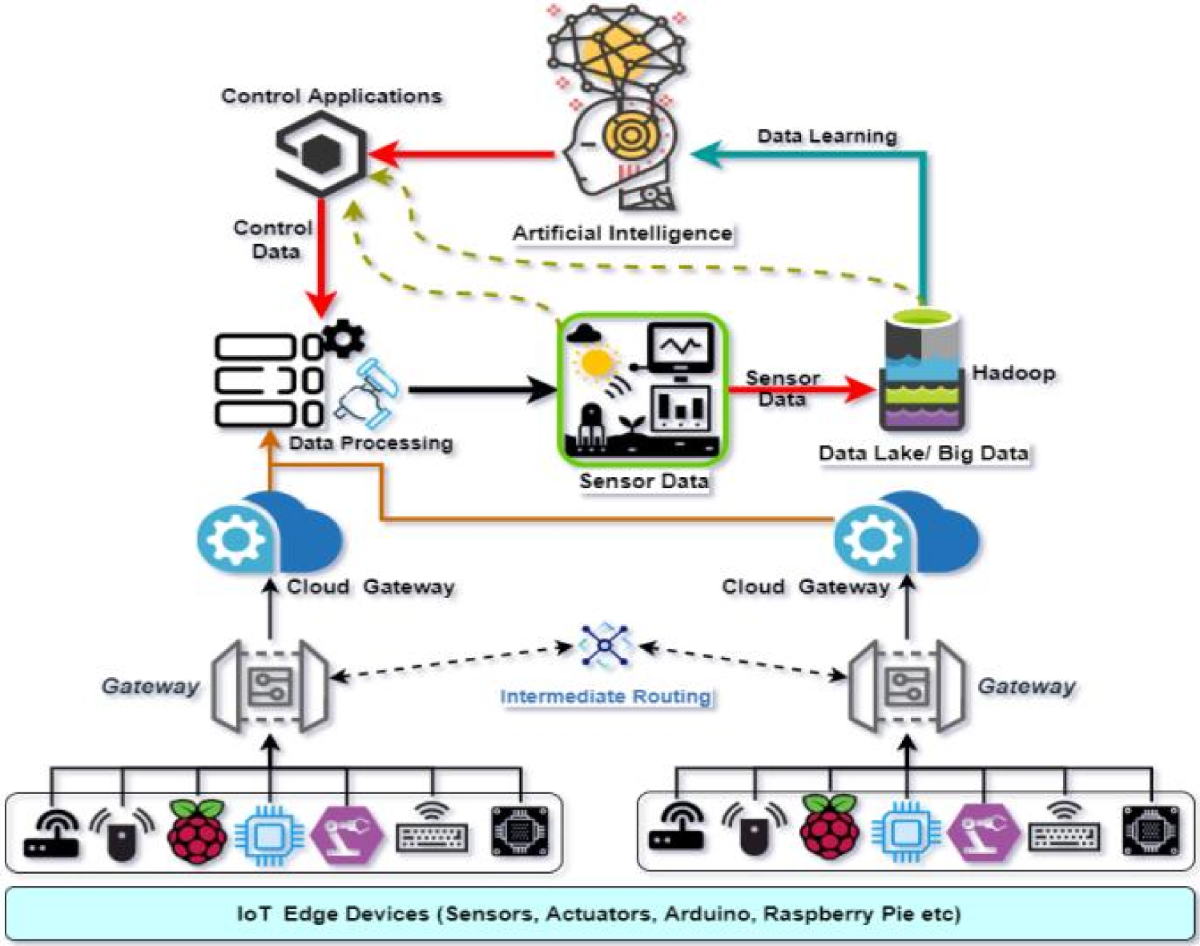
Cyber Physical Systems Convergence
Industries are blending digital tech with physical operations like never before. This blend, known as…
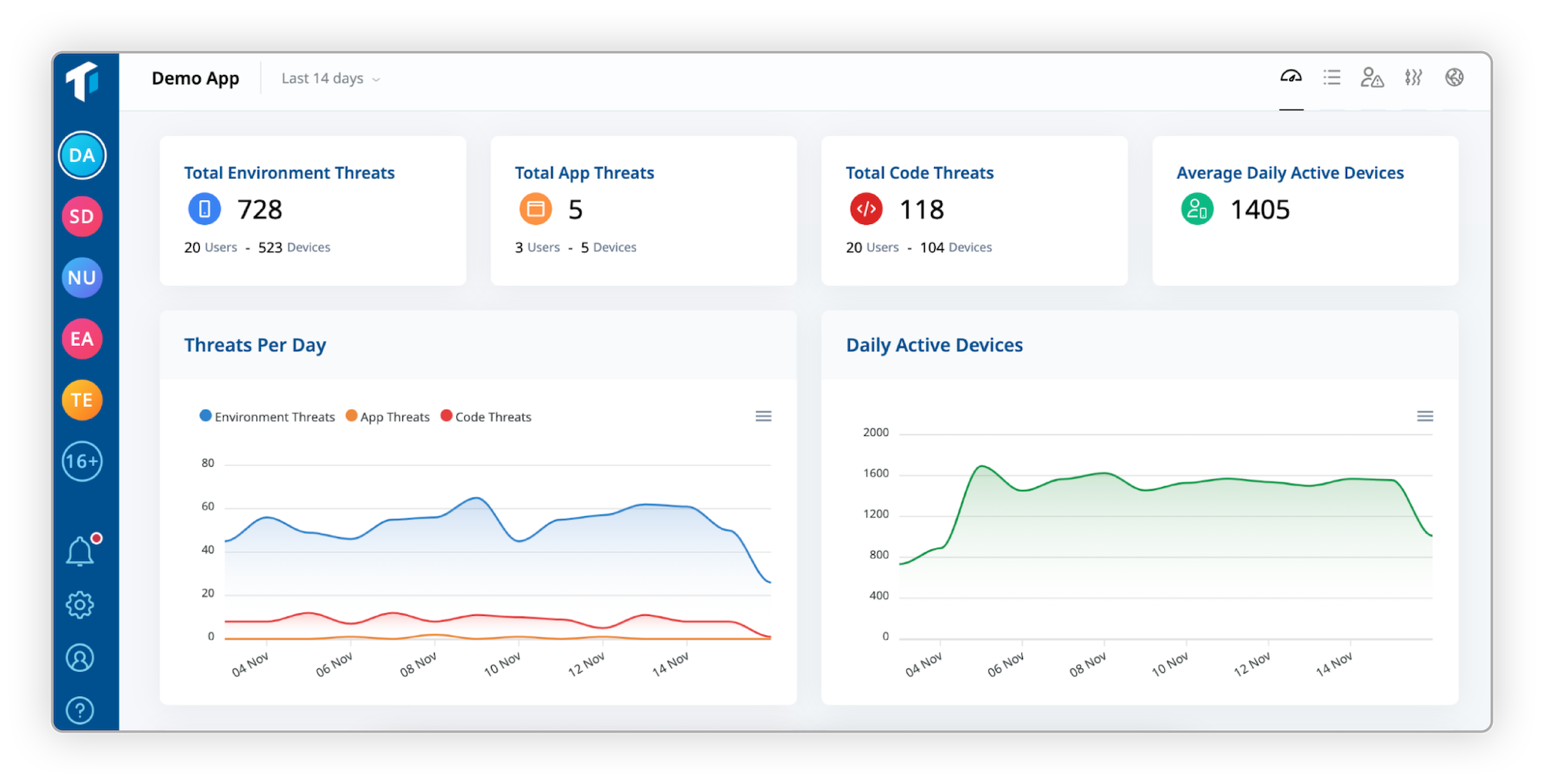
Continuous Threat Exposure Management (CTEM)
Cyber threats are everywhere. Businesses face constant risks from hackers looking to exploit weaknesses in…
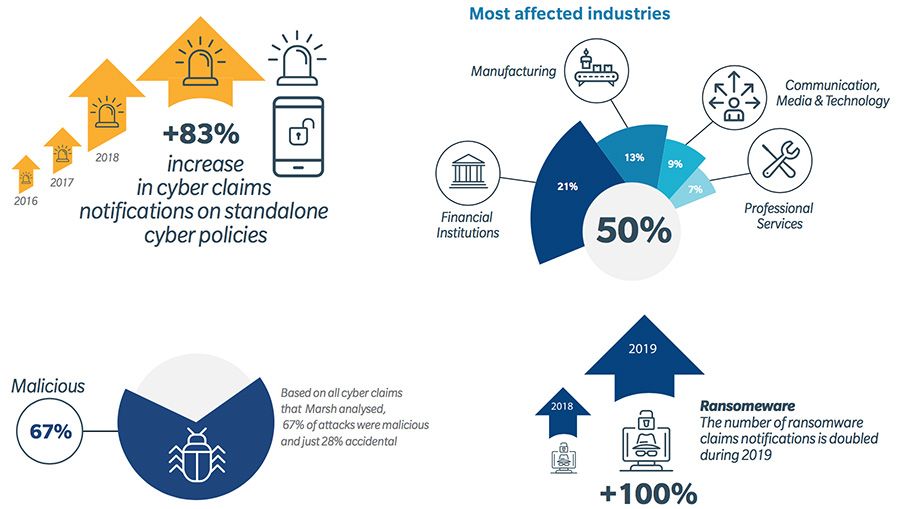
Financialized Cyber Risk
Businesses face threats that can hit their bottom line hard. One big issue is cyber…
Geopolitical Cyber Fragmentation
The world we live in today is more connected than ever, but that connection is…
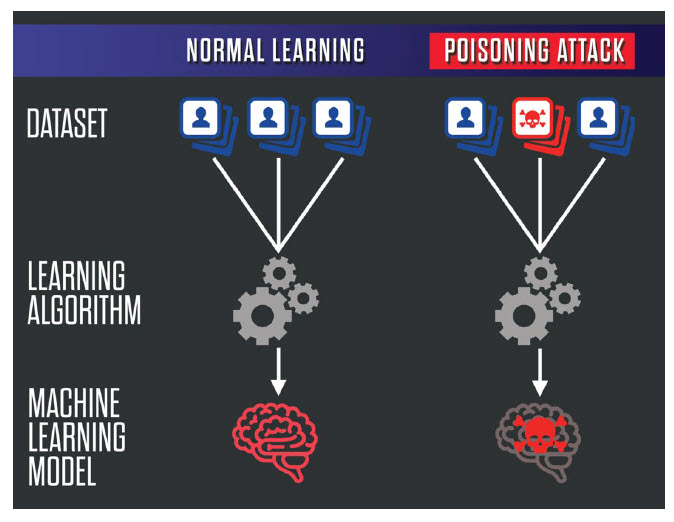
Adversarial Machine Learning Attacks
Machine learning powers everything from spam filters in your email to self-driving cars on the…
Machine Identity Explosion
Businesses are moving faster than ever, relying on clouds, automation, and smart tech to get…