Threat Hunting with AI
In today’s world, cyber threats don’t wait for you to notice them. Attackers hide in networks for weeks or months, using stolen credentials, living-off-the-land techniques, or brand-new malware that traditional tools miss. That’s why more security teams are moving from reactive defense to proactive Threat Hunting with AI.
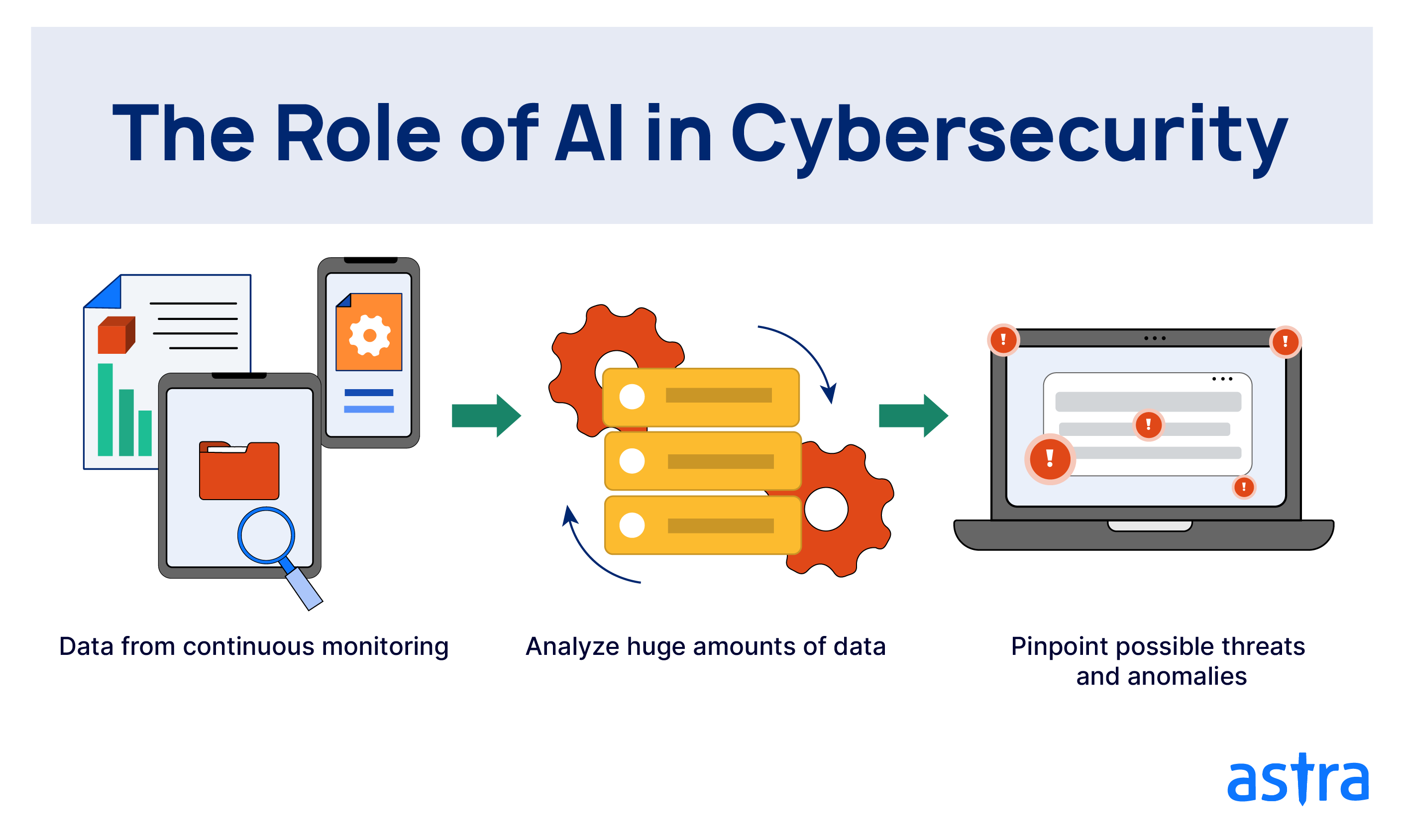
Threat Hunting with AI means using artificial intelligence to actively search for signs of compromise before damage happens. AI handles massive data volumes, spots subtle patterns, and learns continuously—making hunts faster and more accurate than ever.
This guide walks through everything you need to know about Threat Hunting with AI, from the basics to real benefits, how it actually works, challenges, best practices, examples, and what’s coming next. Let’s explore how this approach is changing cybersecurity.

(Infographic showing AI’s central role in modern cybersecurity capabilities – Credit: XenonStack)
Understanding Basic Threat Hunting First
Threat hunting is proactive searching for threats inside your environment. Instead of waiting for alerts from firewalls or endpoint detection tools, hunters go looking for evidence of attackers already inside.
Traditional hunting relies on human expertise: analysts form a hypothesis (like “attackers might be using PowerShell for lateral movement”), then query logs, endpoints, and network data to prove or disprove it.
This works against advanced persistent threats (APTs) that avoid triggering signatures. But as data grows and skilled hunters stay hard to find, manual hunting can’t keep up alone.
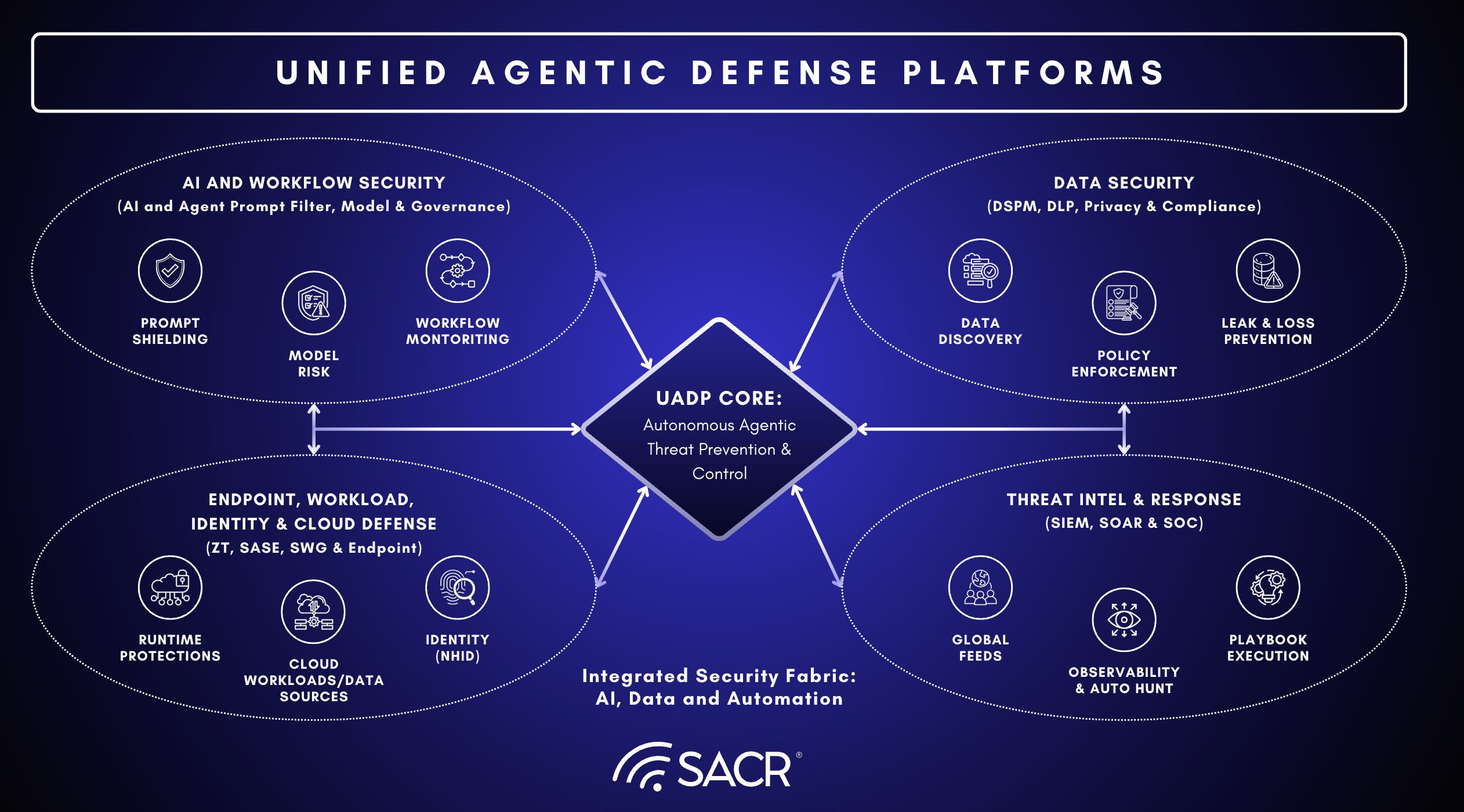
That’s where Threat Hunting with AI makes the difference. AI automates pattern recognition, anomaly spotting, and correlation across sources, letting human hunters focus on high-value decisions.
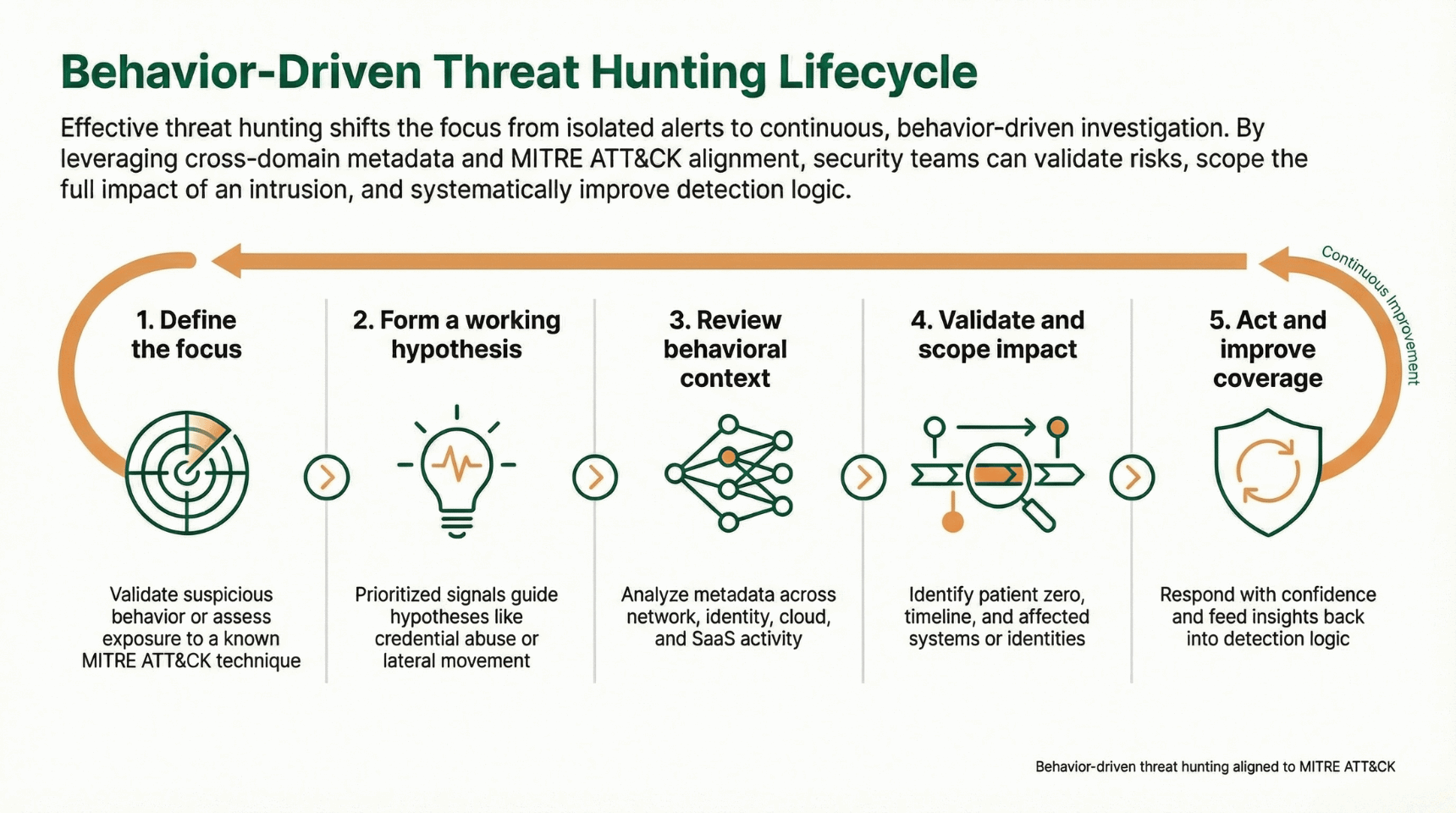
(Behavior-Driven Threat Hunting Lifecycle diagram aligned with MITRE ATT&CK – Credit: Vectra AI)
Why AI Is a Game-Changer for Threat Hunting
Modern networks generate terabytes of logs daily—from endpoints, cloud services, identity systems, email, and more. Humans can’t review it all.
AI excels here because:
- It processes huge datasets instantly
- It finds deviations from normal behavior without needing predefined rules
- It learns from your environment over time
- It connects distant events that look unrelated at first glance
Recent industry reports show organizations using AI-assisted hunting detect threats weeks earlier than those relying on alerts alone. In many cases, AI reduces dwell time from months to days.

(2025 Threat Hunting Report highlights showing AI-powered adversary trends – Credit: CrowdStrike)
How Threat Hunting with AI Actually Works Step by Step
The process usually follows these stages, with AI powering each one:
- Data Ingestion and Baseline Creation AI pulls in logs from everywhere and builds a model of “normal” activity for users, devices, and applications.
- Anomaly and Behavior Detection Machine learning watches for outliers—like unusual login times, rare process executions, or unexpected data transfers.
- Hypothesis Testing at Scale You start with a question (“Are we seeing credential dumping?”). AI quickly searches across months of data to find matches or related activity.
- Event Correlation and Enrichment When something suspicious appears, AI links it to other signals—maybe tying a weird login to cloud API calls minutes later.
- Prioritization and Investigation Support AI scores findings by risk, suggests next queries, and even summarizes context for analysts.
- Feedback Loop and Model Improvement Confirmed threats or false positives feed back into the system, making future detections smarter.

(Detailed AI-driven threat hunting workflow from data sources to action – Credit: XenonStack)

(End-to-end AI threat detection pipeline visualization – Credit: XenonStack)
Real Benefits Teams Experience with Threat Hunting with AI
Organizations adopting this approach report clear wins:
- Much Earlier Detection — Many threats get caught during reconnaissance or initial access instead of after data theft
- Handling Unknown Attacks — Behavior-based AI catches zero-days and fileless attacks that evade signatures
- Scaling Security Operations — One team can cover environments with thousands of endpoints and cloud accounts
- Lower Alert Fatigue — AI filters noise, so analysts see fewer but higher-quality leads
- Stronger Incident Response — Hunts provide rich context, speeding up containment
- Cost Efficiency — Preventing breaches saves far more than the investment in AI tools

(Key benefits of AI automation in cybersecurity – Credit: Fortinet)

(Top practical uses of AI for threat prevention – Credit: Keepnet)
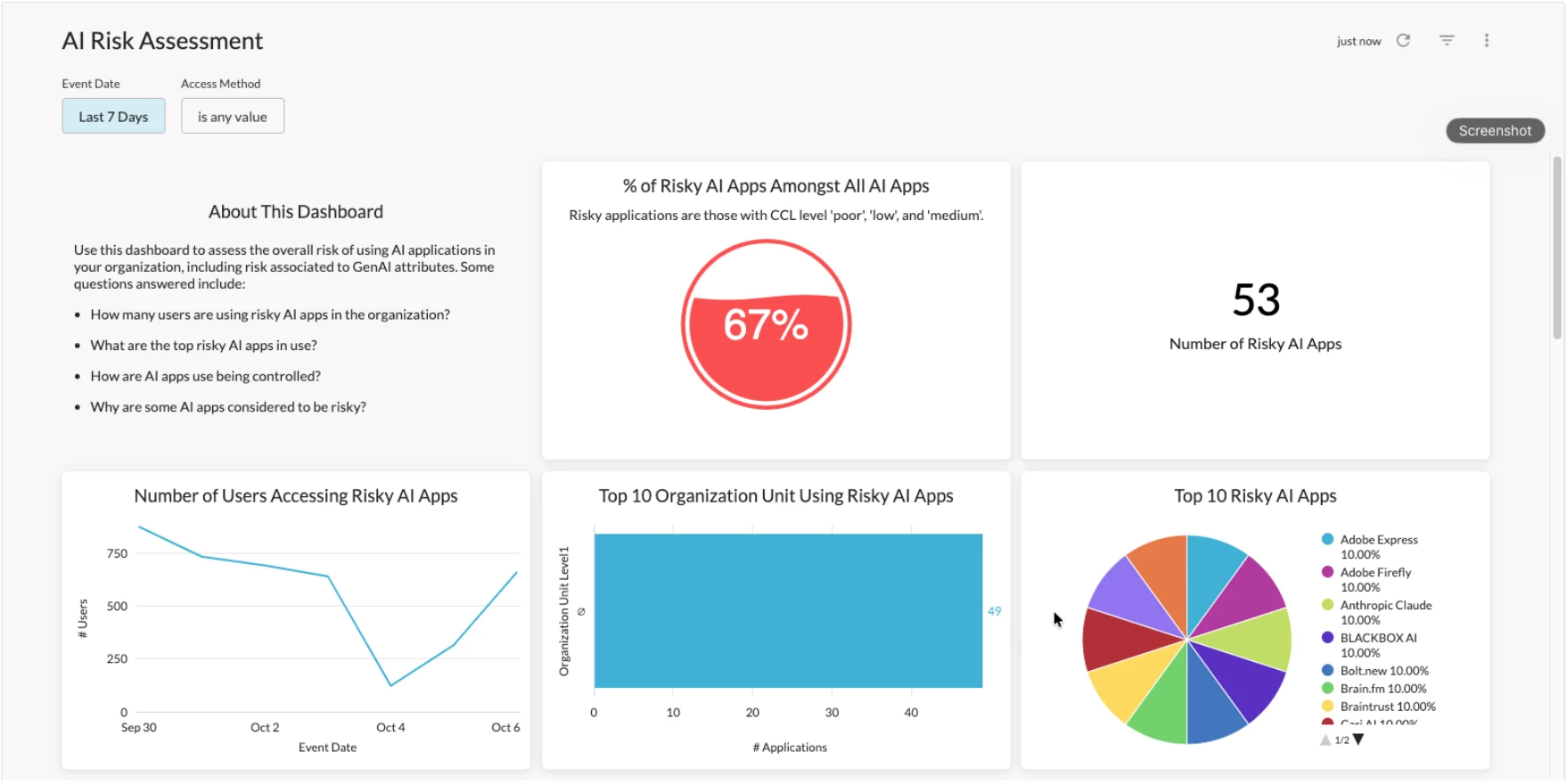
Common Challenges You Should Prepare For
No approach is perfect. Here are the main hurdles:
- False Positives Still Happen — New software, seasonal business changes, or legitimate admin activity can trigger alerts
- Data Quality Matters — Incomplete logging or blind spots limit what AI can see
- Attackers Also Use AI — Adversaries generate better phishing, evade detection, or automate attacks
- Skill Requirements — Teams need people who understand both security and AI concepts
- Privacy Concerns — Behavioral monitoring raises questions about employee monitoring
- Over-Reliance Risk — AI is powerful, but human context remains essential for critical decisions
The best programs balance AI automation with human oversight.
.png?width=1110&height=624&name=New%20AI-Driven%20Cybersecurity%20Threats%20(8).png)
(New AI-driven cybersecurity threats to watch – Credit: ProServeIT)
Best Practices to Get Started and Succeed
- Build Solid Data Foundations — Ensure comprehensive logging from endpoints, network, cloud, and identity
- Start with High-Impact Hunts — Focus on common attack paths like credential abuse or ransomware precursors
- Use Established Frameworks — Align hunts with MITRE ATT&CK for better structure
- Combine AI + Human Expertise — Let AI find and correlate, let people decide significance
- Tune Continuously — Review detections, reduce noise, and improve models
- Integrate Threat Intelligence — Feed current IOCs and TTPs into your AI platform
- Test Regularly — Run purple team exercises to validate coverage
- Document Everything — Track hunts, findings, and lessons for maturity
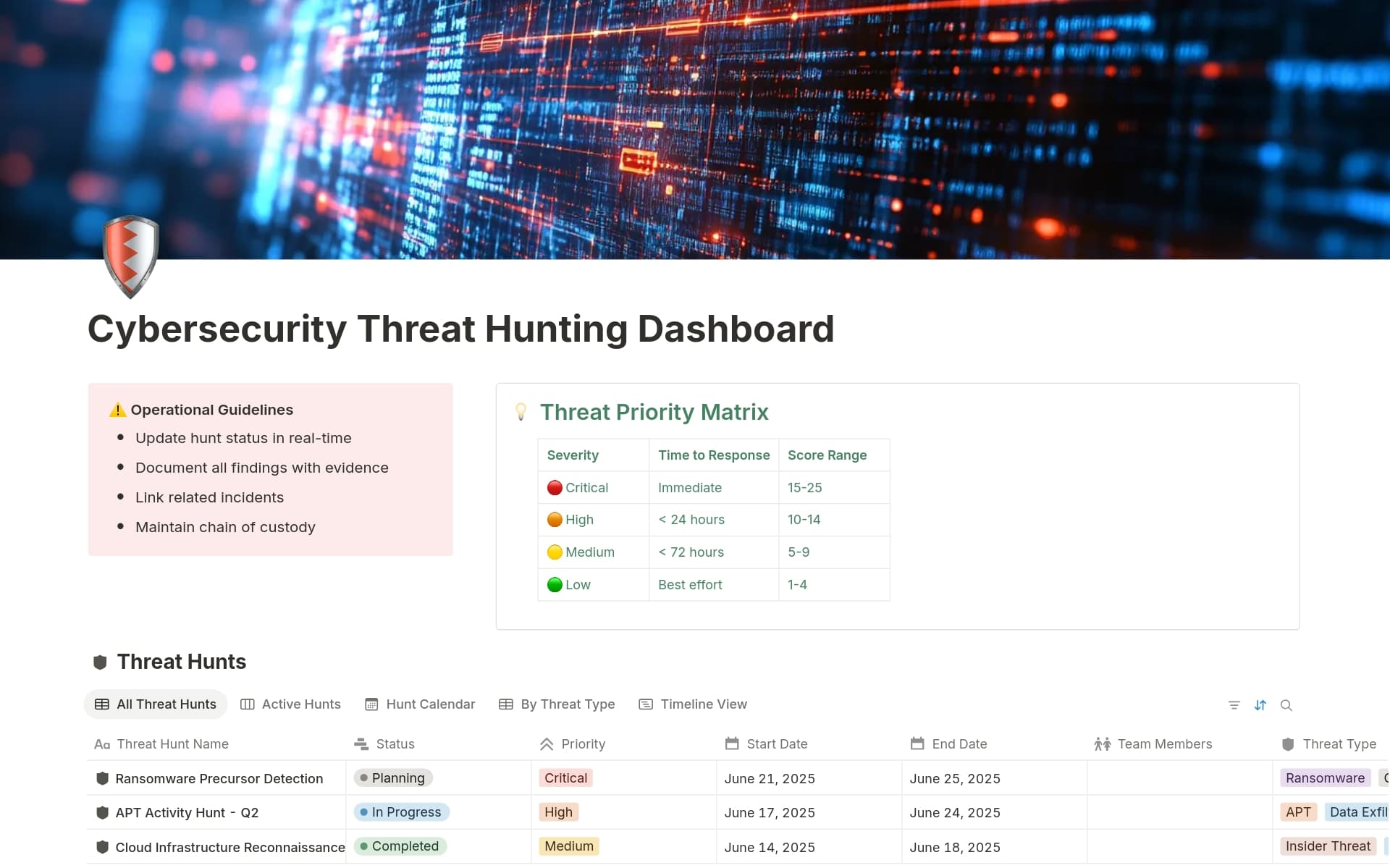
notion.com
Cybersecurity Threat Hunting Dashboard Template by micahtml | Notion Marketplace
(Example threat hunting dashboard for tracking hunts and priorities)
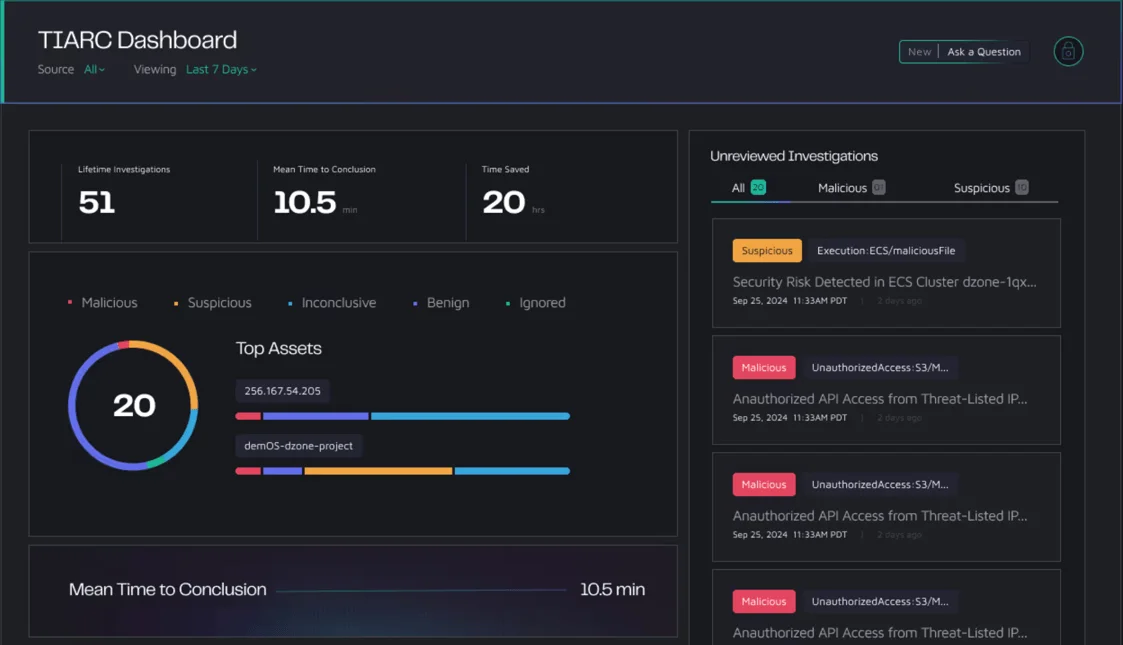
socradar.io
Top 10 AI-Powered Cybersecurity Platforms
(Modern AI-powered threat investigation dashboard example)
Examples of Threat Hunting with AI in Action
Security teams have shared success stories:
- One financial organization used behavioral AI to detect unusual SaaS logins tied to data exfiltration attempts, stopping a potential breach early.
- Energy sector hunters found lateral movement using legitimate tools by spotting deviations from baseline admin behavior.
- Cloud-focused teams caught adversaries abusing AI/ML services themselves for reconnaissance and persistence.
These examples show Threat Hunting with AI turning defense from waiting to actively disrupting attackers.

AI SOC Analyst Platform: Autonomous Threat Hunting | Dropzone AI
(AI analyst interface for fast threat hunting sessions)
Looking Ahead: The Future of Threat Hunting with AI
Looking ahead to 2026–2027 and beyond, the landscape of Threat Hunting with AI is set to evolve dramatically as technology pushes boundaries further. One of the most exciting shifts will be the rise of more autonomous AI agents that can run complete hunt cycles on their own. These agents won’t just flag anomalies—they’ll independently form hypotheses based on incoming data, query massive datasets across your environment, correlate findings, investigate leads step by step, and even recommend or initiate low-risk response actions, all while keeping detailed logs for human review. This level of autonomy will free up security teams from routine monitoring, letting them focus on strategic oversight and the most complex cases.


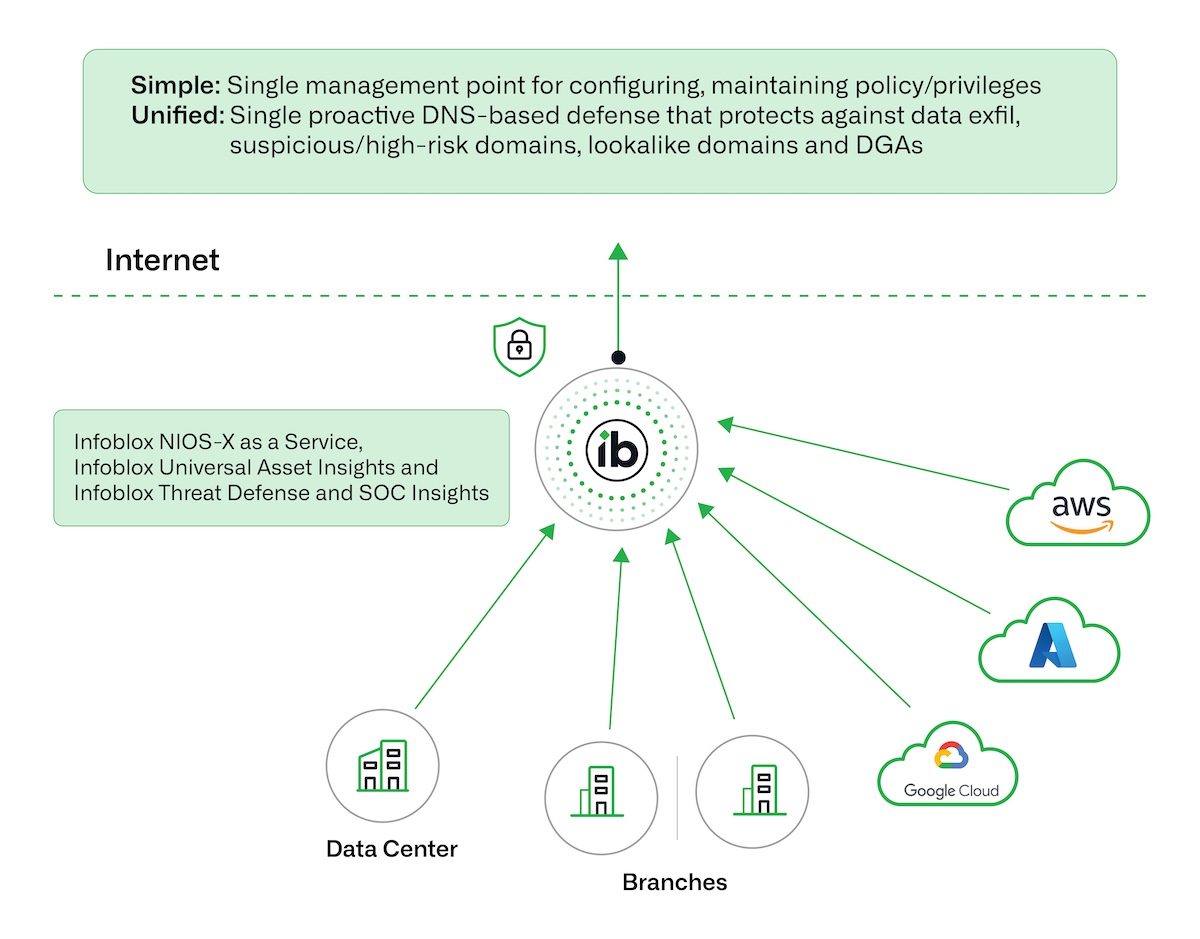
At the same time, we’ll see deeper integration of threat hunting capabilities across hybrid and multi-cloud environments. As organizations continue to spread workloads between on-premises data centers, AWS, Azure, Google Cloud, and various SaaS platforms, AI-driven hunting tools will need to provide seamless visibility and unified analysis without silos. Future systems will automatically pull in telemetry from diverse sources, normalize it, and apply consistent behavioral models and detection rules everywhere, making it much easier to spot threats that move laterally across these boundaries or exploit cloud-specific misconfigurations.
Another major advancement will come from predictive capabilities that go beyond reacting to current signals and start forecasting potential attack paths. By analyzing historical patterns, current adversary tactics from threat intelligence feeds, and your organization’s unique baseline, AI will map out likely next steps an attacker might take—such as which assets they could target after initial access or how they might escalate privileges. This forward-looking approach will allow teams to harden defenses proactively, close gaps before exploitation, and even simulate attack scenarios to test resilience.
.png)

As attackers increasingly leverage AI themselves—creating more sophisticated phishing content, generating polymorphic malware, or automating reconnaissance—defenders will need robust counter-AI measures built right into hunting platforms. These defenses could include adversarial robustness training for detection models, real-time monitoring for signs of AI-generated artifacts in network traffic or logs, and specialized techniques to detect when adversaries are using generative tools to evade traditional signatures or behavioral baselines. Staying one step ahead in this AI-versus-AI arms race will become a core part of mature threat hunting programs.

Finally, generative AI will play a much bigger everyday role by helping security analysts write effective hunt queries and summarize complex findings quickly. Instead of spending hours crafting precise search strings in query languages, hunters will describe what they’re looking for in natural language—”show me any unusual PowerShell executions from non-admin accounts in the last 30 days that contacted external IPs”—and generative models will translate that into optimized queries for tools like Splunk, Elastic, or custom platforms. On the back end, these same models will automatically generate concise executive summaries, explain why a particular alert chain is suspicious, or highlight key evidence in incident reports, making investigations faster and more accessible even for junior team members.

Taken together, these developments point to a future where Threat Hunting with AI becomes far more proactive, integrated, intelligent, and collaborative—shifting the balance firmly toward defenders who embrace these capabilities early and thoughtfully. The arms race continues, but the tools available to security teams are advancing at an incredible pace.
Final Thoughts on Threat Hunting with AI
Threat Hunting with AI represents one of the biggest steps forward in cybersecurity. It shifts teams from reacting to alerts to proactively finding and stopping threats.
If you’re starting, focus on good visibility, pick AI-capable tools that fit your environment, and combine machine speed with human insight. Over time, you’ll detect threats earlier, respond faster, and build stronger defenses.
For more on related topics, check our guides on MITRE ATT&CK in practice and building effective SOC teams.
Stay proactive—your network’s security depends on it.
Share this content:














Post Comment