Secure Your APIs Against Emerging Threats in 2026
If you want to secure your APIs against emerging threats, you need practical steps that work right now. This complete guide walks you through everything in plain English: the new dangers, simple fixes, tools that actually help, and what top companies are doing to stay safe.
APIs power almost every app and service we use today. From ordering food to checking bank balances, they quietly connect everything behind the scenes. But in 2026, these same APIs have become the favorite target for attackers. Hackers no longer need complex tricks — they simply abuse the doors you left open.
By the end, you’ll know exactly how to protect your APIs without slowing down your team or breaking your budget.
Table of Contents
- Understanding APIs and Why They Need Protection
- The Biggest API Threats in 2026
- How to Secure Your APIs Step by Step
- Must-Have Tools for API Protection
- Real Stories from 2025 Breaches
- What’s Coming Next and How to Prepare
- Quick Checklist You Can Use Today
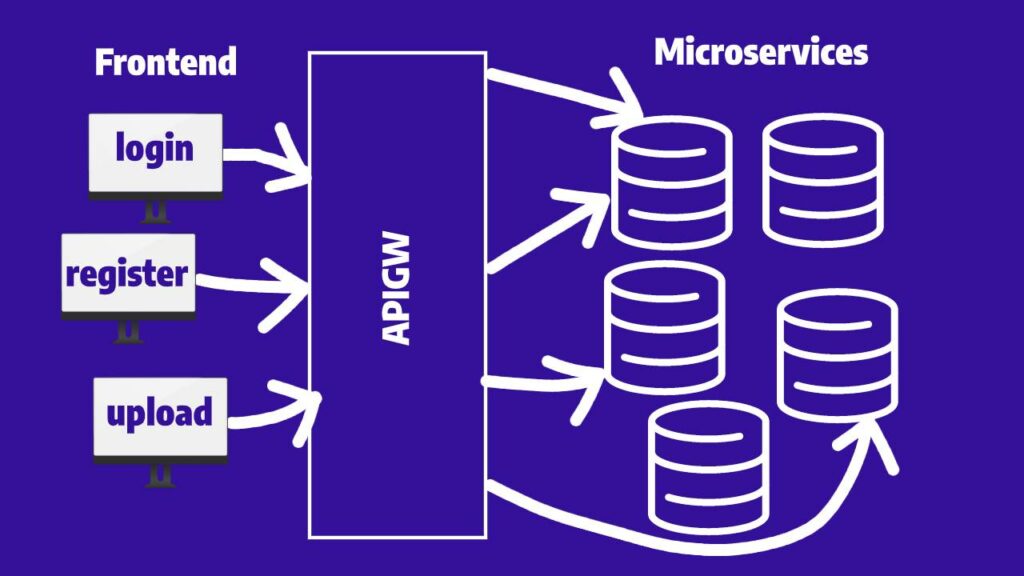
Image Credit: Dashbird – AWS API Gateway Architecture Illustration
Understanding APIs and Why They Need Protection {#understanding-apis}
Think of an API as a waiter in a restaurant. You (the customer) tell the waiter what you want. The waiter goes to the kitchen (your server) and brings back the food (data).
APIs do the same thing for software. Your mobile banking app talks to the bank’s servers through APIs. Your weather app pulls data from government servers the same way.
In 2026, businesses run on thousands of these connections. Companies have internal APIs for their own teams, partner APIs for suppliers, and public APIs for customers. Every single one is a potential entry point.
Why does this matter so much now?
Because APIs handle sensitive information — credit card numbers, personal health data, company secrets. A single weak API can expose millions of records in minutes. Reports from 2025 show that 17% of all published vulnerabilities were API-related, and 43% of the vulnerabilities actually exploited in the real world came through APIs.
Attackers love APIs because they are fast, automated, and often poorly protected. One wrong setting and your entire system can be wide open.
The good news? You don’t need to be a security expert to fix this. Simple, consistent habits make a huge difference.
The Biggest API Threats You Must Watch in 2026 {#emerging-threats}
Here are the threats that security teams worry about most this year. Each one comes with real examples and why it hurts.
1. AI-Powered Attacks and Machine-Speed Abuse
Attackers now use AI to test thousands of API calls per second. They don’t guess passwords anymore — they study your API patterns and strike at the exact weak spots.
In 2025, automated attacks grew dramatically. One report found that cross-site issues jumped to the top spot for API abuse. AI agents can keep trying new combinations until they find a way in.

Image Credit: Dreamstime / Yana Lysenko – AI-powered cybersecurity visualization
Even worse, AI agents themselves create new risks. When your own AI tools call external APIs, one mistake can let attackers control the entire workflow.
2. Broken Object Level Authorization (BOLA)
This is still the number one API risk. It happens when the API checks “who is logged in” but forgets to check “does this person own this record?”
Example: User A logs in and changes the user ID in the URL to User B’s ID. Suddenly User A sees User B’s private data. This flaw appears in almost every API that deals with user profiles, orders, or documents.
Security researchers say BOLA and similar authorization problems caused most of the big breaches last year.
3. Missing or Weak Authentication
Some APIs still trust anyone who knocks on the door. Others use simple API keys that never expire or get shared by mistake.
In 2025, 59% of API vulnerabilities needed no authentication at all. That means anyone on the internet could reach sensitive functions if they guessed the right URL.
4. Model Context Protocol (MCP) Vulnerabilities
This new threat exploded in 2025. MCP is the control system that lets AI agents talk to each other and to tools. Over 315 serious MCP problems appeared last year — a 270% jump in just a few months.
If an attacker takes over an MCP connection, they can control entire chains of AI actions. One bad setting and your AI assistant starts doing whatever the hacker wants.
5. Shadow APIs and Forgotten Endpoints
Developers create test APIs during projects. Sometimes those APIs stay live forever with no security.
These “shadow” APIs don’t appear in your official list, so nobody monitors them. Hackers find them easily with automated scanners and use them as secret backdoors.
6. Injection Attacks and Bad Input Handling
Attackers send tricky data — SQL commands, malicious code, or huge files — hoping your API will pass it straight to the database or server.
Broken input validation ranked among the top flaws again in 2026 reports. One small mistake here can let attackers steal or delete everything.
7. Insecure Resource Consumption (DoS via APIs)
Instead of flooding your website with traffic, attackers now hit specific API endpoints that use a lot of server power. A few clever calls can crash your whole service and cost you thousands in cloud bills.
This attack type moved up to fourth place in abuse rankings last year.
8. Supply Chain Attacks Through Third-Party APIs
You use Stripe for payments, Google Maps for location, or Twilio for messages. If any of those partners gets compromised, the attackers can reach you through their API keys.
Supply chain problems keep growing because companies share more and more APIs with partners.
These eight threats cover most real incidents in 2025-2026. The pattern is clear: attackers exploit simple mistakes at massive scale.

Image Credit: Valency Networks – Common web and API attack vectors diagram
How to Secure Your APIs Against Emerging Threats – Practical Steps {#best-practices}
You don’t need fancy tools to start. Follow these proven methods in order.
Step 1: Make a Complete API Inventory
List every single API — public, internal, partner, test, and old versions. Include shadow APIs too.
Use automated discovery tools that scan your cloud accounts and code repositories. Update this list every month. Without knowing what exists, you cannot protect it.
Step 2: Use Strong Authentication Everywhere
Never rely on “the client will handle security.” Always verify on the server side.
Best options in 2026:
- OAuth 2.0 with short-lived tokens
- JSON Web Tokens (JWT) with proper signing
- Mutual TLS for machine-to-machine connections
- API keys that rotate automatically every 30-90 days
For AI agents, use workload identities instead of long-term secrets.
Step 3: Enforce Proper Authorization at Every Level
Check permissions for every single request:
- Does this user own this object? (Object Level)
- Is this user allowed to call this function? (Function Level)
Do these checks in the backend code, not just in the frontend. Add context — IP address, time of day, device type — for extra safety.
Step 4: Validate and Sanitize All Input
Never trust data coming from outside. Check:
- Data type and size
- Required fields
- Allowed values only
Use libraries that automatically block common injection patterns. Set strict limits on file uploads and request sizes.
Step 5: Always Use HTTPS and Encrypt Sensitive Data
HTTPS must be mandatory — no exceptions. Encrypt data at rest too, especially in databases and logs.
Never log API keys, passwords, or personal information.
Step 6: Add Rate Limiting and Quotas
Limit how many requests each user or IP can make per minute. Different limits for different endpoints (login gets stricter limits than public search).
This stops both brute-force attacks and resource exhaustion.
Step 7: Monitor Everything in Real Time
Set up logging for every API call. Watch for:
- Sudden spikes in traffic
- Unusual patterns (one user accessing thousands of records)
- Failed authorization attempts
- Requests from unexpected locations
Tools that show live dashboards help you spot problems before they become breaches.
Step 8: Use an API Gateway as Your First Line of Defense
Place a gateway in front of all your APIs. It handles authentication, rate limiting, logging, and basic threat blocking in one place.
Popular choices include AWS API Gateway, Kong, or open-source options. The gateway acts like a security bouncer for all your services.
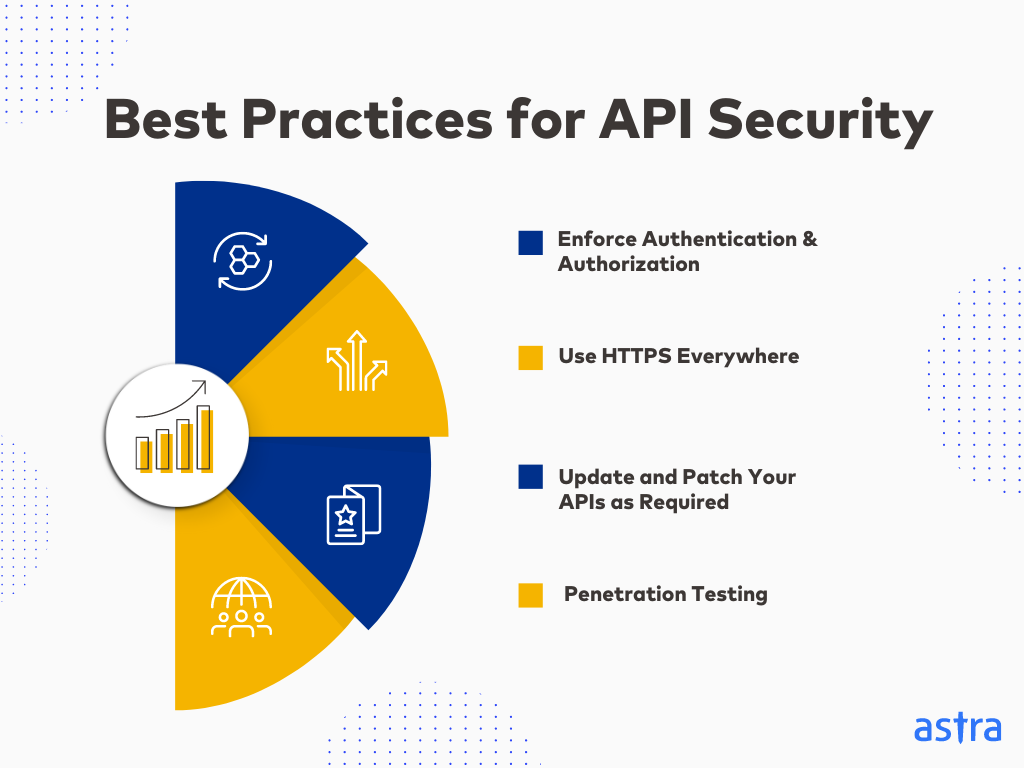
Image Credit: Astra Security – Best Practices for API Security infographic
Step 9: Test Regularly and Fix Fast
Run automated security scans every week. Do manual penetration tests every quarter. Fix critical issues within days, not months.
Also test after every major code change — security should be part of your normal development process.
Step 10: Plan for AI-Specific Risks
If you use AI agents or LLMs:
- Give them the smallest possible permissions
- Log every action they take
- Review their API calls regularly
- Use sandboxing where possible
Treat AI agents like powerful but untrusted employees — verify everything they do.
Follow these ten steps and you will block 95% of common attacks. The remaining 5% need advanced tools and constant vigilance, but you will already be far ahead of most companies.
Must-Have Tools to Secure Your APIs in 2026 {#tools}
You don’t need to buy everything at once. Start with free or low-cost options and add as you grow.
API Gateways
- AWS API Gateway or Azure API Management (great if you already use those clouds)
- Kong or Tyk (open-source and very flexible)
Security and Monitoring
- Wallarm or 42Crunch for automated API threat detection
- OWASP ZAP or Postman for testing
- Datadog or New Relic for full observability
Web Application Firewall (WAF) with API Support
- Cloudflare, Fastly, or Akamai — they now have excellent API protection features
Authentication Services
- Auth0, Okta, or Keycloak for easy OAuth setup
Secret Management
- HashiCorp Vault or AWS Secrets Manager to stop hard-coded keys
Many of these tools offer free tiers perfect for small teams. Larger companies combine a gateway with a dedicated API security platform for the best results.
Real Stories from Recent Breaches and What We Learned {#case-studies}
Last year, several well-known companies learned hard lessons:
One logistics company left a test API endpoint live with full database access. Attackers found it in minutes and stole customer addresses. The fix? Proper inventory and automatic cleanup of test endpoints.
A fintech startup used the same API key across development and production. When a developer account got compromised, attackers drained test wallets that had real money. Lesson: separate environments completely and rotate keys often.
An e-commerce platform suffered BOLA attacks for weeks before noticing. Customers could view each other’s order history. The company fixed it with strict object ownership checks and added monitoring alerts.
These stories repeat every month. The companies that recover fastest are the ones that already had good logging and quick response plans.
What’s Coming Next and How to Prepare {#future}
2026 will bring even more AI agents and machine-to-machine communication. Expect:
- More regulations around API security (especially in Europe and finance)
- Quantum-resistant encryption becoming standard for high-security APIs
- Automatic security testing built into every code commit
Start preparing now by:
- Training your developers on secure API design
- Building a security checklist for every new API
- Creating an incident response plan just for API attacks
The companies that treat API security as a normal business process — not an extra task — will win.
Your API Security Checklist You Can Use Today {#checklist}
Print this or save it:
- Do I have a full list of all APIs?
- Does every API require strong authentication?
- Do I check authorization for every object and function?
- Am I validating all input on the server?
- Is HTTPS enforced everywhere?
- Do I have rate limits in place?
- Am I monitoring logs for strange behavior?
- Have I tested my APIs for common attacks recently?
- Are all secrets rotated and never hard-coded?
- Do my AI tools have minimal permissions?
Go through this list once per quarter. Mark items as done and celebrate small wins.
Final Thoughts
Secure your APIs against emerging threats is not a one-time project — it’s an ongoing habit. Start small today. Pick one section from this guide and improve it this week.
Your users trust you with their data. Strong API security shows you take that trust seriously. It also saves money by avoiding expensive breaches and downtime.
The threats in 2026 are real, but so are the solutions. Teams that follow these practical steps sleep better at night knowing their systems are protected.
Ready to begin? Open your API inventory right now and start with the first item on the checklist. You’ve got this.
Frequently Asked Questions
How often should I test my APIs for security? At least once per month for automated scans and every three months for deeper manual testing.
Do small businesses need API security too? Yes. Size doesn’t matter — attackers target easy targets first.
Can open-source tools provide good protection? Absolutely. Kong, OWASP ZAP, and Keycloak are used by huge companies.
What is the biggest mistake most teams make? Assuming “our frontend checks everything” or “nobody will find this endpoint.”
Stay safe out there. Protect your APIs, protect your business.
Share this content:














Post Comment