How Regulatory Volatility Is Shaping Cyber Strategies in 2026
Regulatory Volatility Is Shaping Cyber Strategies more than ever before. Rules aren’t just getting stricter. They’re changing fast, overlapping across countries, and hitting every industry from small e-commerce shops in Jamshedpur to global banks. If you’re still treating compliance as a once-a-year checkbox, you’re already behind.
Imagine running a business in 2026. One month your team is focused on rolling out new AI tools. The next, a fresh set of rules from Brussels or Washington forces you to rethink everything from data storage to vendor contracts. This is regulatory volatility in action — and it’s quietly reshaping how smart companies protect themselves online.
What Exactly Is Regulatory Volatility?
Think of it like the weather in the mountains. One day it’s sunny and calm. The next, a storm rolls in without much warning. In cybersecurity, “regulatory volatility” means laws and rules keep shifting — sometimes every few months.
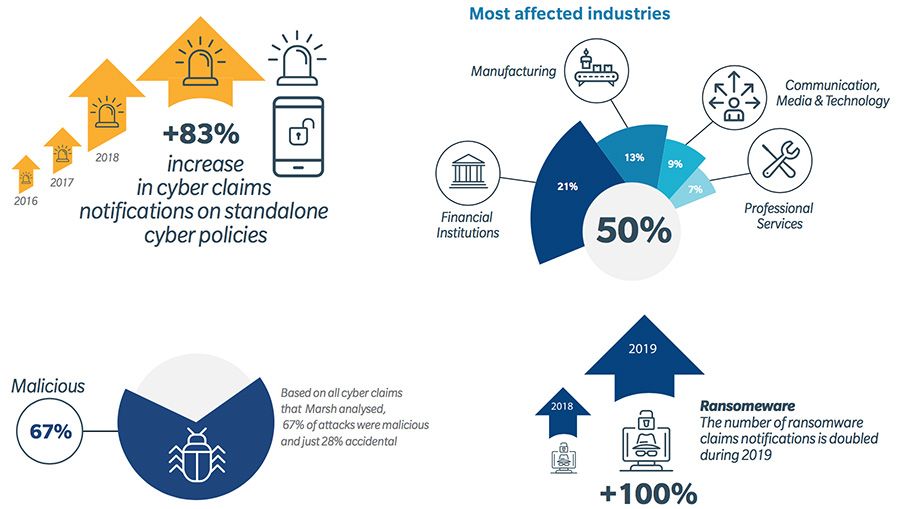
Why does this happen? Cyber threats evolve faster than lawmakers can keep up. Ransomware gangs get smarter. AI makes attacks easier and cheaper. Supply chains stretch across continents. Governments respond by updating old rules or creating new ones.
In 2026, this volatility feels especially intense because so many big changes hit at once:
- The European Union rolled out updates to its NIS2 rules in January.
- New U.S. state privacy laws kicked in across Indiana, Kentucky, and Rhode Island.
- Full enforcement of the EU AI Act arrived in August.
- Reporting deadlines under the Cyber Resilience Act started in September.
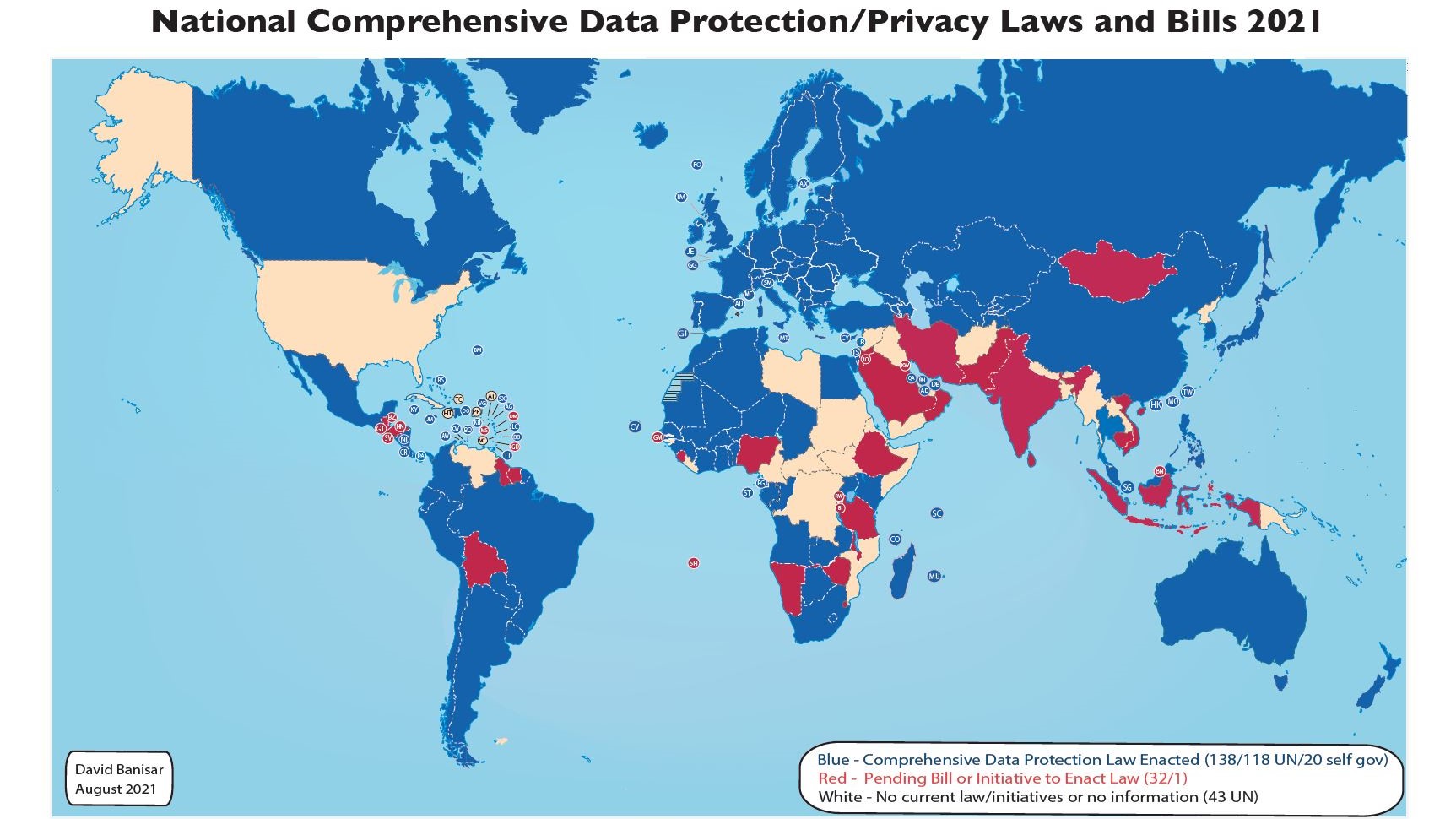
Businesses that operate across borders feel it the most. A single company might need to follow GDPR in Europe, CCPA updates in California, and DPDP rules in India — all slightly different.
The result? Cyber strategies can no longer be “set it and forget it.” They must be flexible, forward-looking, and baked into everyday operations.

Image credit: HIPAA Journal – Average cost of data breaches 2018-2025 (showing the steady climb that makes compliance critical in 2026)
Why 2026 Feels Like a Tipping Point
Last year’s breach reports showed average costs hovering around $4.44 million globally (IBM Cost of a Data Breach Report 2025). That’s not pocket change for most companies. Non-compliance fines can easily add millions more — plus the reputational hit when customers lose trust.
Governments noticed. They decided 2026 would be the year of accountability. Instead of vague “best practices,” rules now demand proof: documented risk assessments, board-level oversight, rapid incident reporting, and tight controls over third-party vendors.
Here’s the good news: companies that get ahead of these changes are seeing real benefits. Better security posture. Lower insurance premiums. Stronger customer confidence. Even easier access to financing, because banks now ask about your cyber maturity.
Major Regulations Driving Change in 2026
Let’s break down the biggest players without drowning you in legal text.
1. NIS2 Directive (EU) – Now with 2026 Amendments The updated NIS2 rules cover more companies than ever — from energy and transport to digital infrastructure and even certain manufacturing firms. Key demands:
- Risk management that covers the entire supply chain
- Incident reporting within 24 hours for serious events
- Management accountability (yes, executives can face personal liability)
- Regular testing and audits
The January 2026 amendments simplified some paperwork and clarified which companies fall under “essential” versus “important” categories. But the core message stayed loud: you must prove you’re resilient, not just say it.
Internal link: If you handle critical infrastructure, read our deep dive on supply chain security basics.
2. DORA – Digital Operational Resilience Act (Financial Sector) Fully in force since early 2025, DORA hit its stride in 2026 with the first full cycle of Register of Information submissions. Banks, insurers, and investment firms must show they can withstand ICT disruptions.
Big focus areas:
- Third-party risk (your cloud provider just became your compliance headache)
- Regular resilience testing (think simulated attacks)
- Clear incident classification and reporting
Even non-EU firms that serve European clients feel the ripple effect.
Image credit: ZPE Systems – Visual summary of DORA’s key pillars
3. Cyber Resilience Act (CRA) – Products with Digital Elements Starting September 2026, manufacturers of smart devices, software, and connected hardware must meet cybersecurity standards before selling in the EU. Vulnerabilities must be reported quickly. Security updates become mandatory for the expected lifetime of the product.
This one hits hardware makers, app developers, and even IoT companies hard.
4. U.S. Developments
- SEC rules require material cyber incidents reported on Form 8-K within four business days.
- New state laws in Indiana, Kentucky, and Rhode Island joined the privacy club on January 1.
- California’s updated CCPA now requires cybersecurity audits for big data handlers.
5. Other Global Moves India’s DPDP Act moved into Phase 2 consent management. Australia strengthened automated decision-making rules. China tightened cross-border data rules effective January 2026.
The pattern? More countries want control over data and demand proof of protection.
How Regulatory Volatility Is Shaping Cyber Strategies Right Now
Regulatory Volatility Is Shaping Cyber Strategies in five practical ways you can see in boardrooms today.
1. Compliance Moves from Legal Team to Everyone It’s no longer “check with compliance.” IT, operations, procurement, and even marketing now own pieces of the puzzle. Smart companies create cross-functional “cyber compliance councils” that meet monthly.
2. Supply Chain Becomes the New Front Line Because rules like NIS2 and DORA put heavy emphasis on vendors, companies now run rigorous security questionnaires and contract clauses. Many now require SOC 2 reports or ISO 27001 certification before signing deals.
3. Board and Executive Accountability Skyrockets Directors want dashboards they can understand. They ask questions like: “What would happen if our main cloud provider went down for 48 hours?” or “How fast can we notify regulators if we spot a breach?”
4. Technology Investment Shifts Toward Automation and Visibility Manual processes can’t keep up with volatility. That’s why tools for continuous monitoring, automated incident response, and AI-driven risk scoring are booming. Organizations using security AI saved an average of $2.22 million per breach according to recent IBM data.
5. Zero Trust Moves from Buzzword to Baseline “Never trust, always verify” is now the default architecture. Micro-segmentation, just-in-time access, and continuous authentication help meet multiple regulations at once.
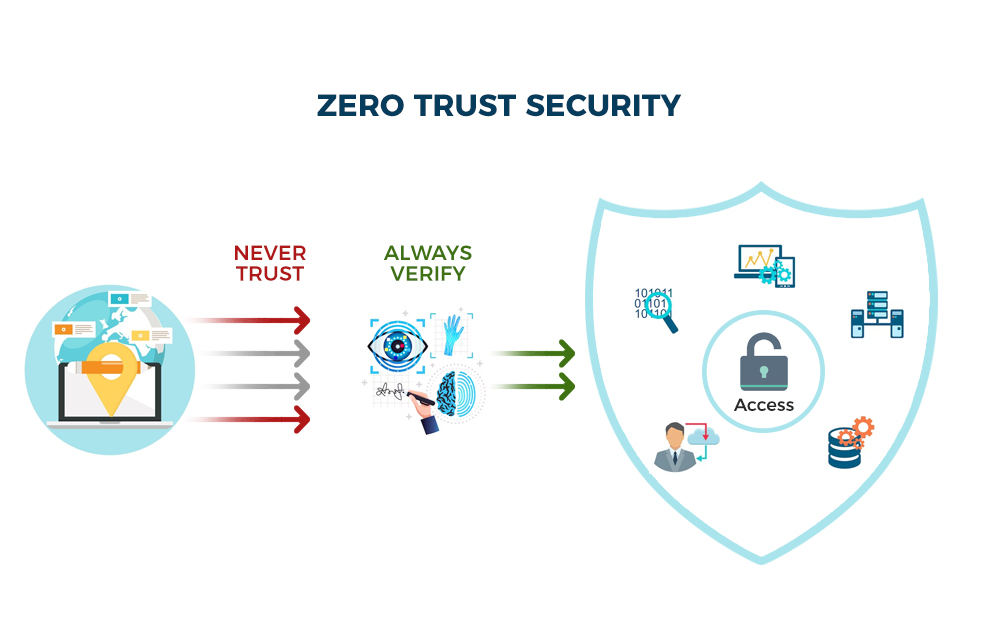
Image credit: Brickwork India – Simple visual of Zero Trust principles
Real Stories from Companies Adapting in 2026
A mid-sized fintech firm in Singapore expanded into Europe last year. When NIS2 deadlines loomed, they didn’t panic. Instead, they mapped every vendor against the new requirements, automated their incident reporting workflow, and trained their entire leadership team. Result? They passed their first audit with flying colors and actually won new clients who valued their “regulation-ready” status.
A manufacturing company in India faced DPDP and upcoming CRA pressures on their IoT sensors. They rebuilt their product development process to include security-by-design checklists. Early investment cost money upfront but cut expected breach exposure by over 60% according to their internal models.
These aren’t huge multinationals with unlimited budgets. They’re regular businesses that decided to treat regulatory volatility as a roadmap rather than a roadblock.
Common Challenges (and How to Overcome Them)
- Resource Strain: Smaller teams feel overwhelmed. Solution: Start with a gap analysis using free NIST or ISO self-assessment tools, then prioritize high-impact fixes.
- Conflicting Rules: One law wants data localized; another allows transfers with safeguards. Solution: Build a central compliance matrix and review it quarterly.
- Keeping Up with Changes: Rules evolve. Solution: Subscribe to trusted update services (we recommend ENISA alerts and IAPP newsletters) and assign one person to track them.
- Employee Buy-In: People hate extra steps. Solution: Make training short, relevant, and even fun with gamified modules.
External resource: For the latest global updates, bookmark the IAPP Legislative Tracker.
Step-by-Step Guide: Building a Resilient Cyber Strategy in 2026
Here’s exactly what to do this quarter:
- Map Your Regulatory Footprint List every country you operate in or sell to. Note which laws apply. Use a simple spreadsheet.
- Conduct a Fresh Risk Assessment Include supply chain, AI usage, and cloud dependencies. Involve department heads.
- Update Policies and Contracts Add cyber clauses to every vendor agreement. Review insurance coverage.
- Implement Core Controls
- Multi-factor authentication everywhere
- Regular backups tested monthly
- Incident response plan with regulatory timelines baked in
- Employee training at least twice a year
- Choose Flexible Technology Look for tools that support multiple frameworks (NIST, ISO, CIS) and offer automated reporting.
- Test and Document Everything Run tabletop exercises. Keep records — regulators love evidence.
- Monitor and Adapt Set Google Alerts for your key regulations. Review your strategy every 90 days.
Internal link: Need help choosing tools? See our comparison of top compliance automation platforms.
The Road Ahead: What to Expect After 2026
Expect more harmonization efforts — countries trying to reduce overlap. AI-specific rules will tighten further. Quantum-resistant encryption will move from nice-to-have to must-have in some sectors.
But the biggest shift? Cybersecurity will become a board-level strategic advantage, not just a cost center. Companies that embrace Regulatory Volatility Is Shaping Cyber Strategies positively will attract better talent, win more business, and sleep better at night.
Conclusion: Turn Volatility into Your Advantage
The rules aren’t going to slow down. But your ability to adapt can become your superpower.
Start small. Pick one area — maybe vendor risk or incident reporting — and make real progress this month. Build momentum. Involve your team. Measure results.
Regulatory Volatility Is Shaping Cyber Strategies in 2026, yes. But you get to decide whether it shapes yours for better or worse.
What’s one step you’re taking this week? Drop a comment below — I read every one and often reply with extra tips tailored to your industry.
FAQs
Q: Do small businesses really need to worry about NIS2 or DORA? A: If you serve EU clients or fall into covered sectors, yes. Many SMEs are now in scope. Start with a simple self-check.
Q: How much will this cost? A: Initial investments vary, but automation often pays for itself through avoided breach costs and lower insurance.
Q: Where can I find official guidance? A: EU sites for NIS2/DORA, SEC.gov for U.S. rules, and your local data protection authority.
Resources & Further Reading
- NIST Cybersecurity Framework (external, dofollow)
- ENISA NIS2 Page
- IBM Cost of a Data Breach Report 2025
- Our guide: Building a Zero Trust Roadmap
Share this content:











Post Comment