Ransomware Kill Chain Disruption
Ransomware attacks have become a nightmare for businesses and individuals alike. These sneaky cyber threats lock up your files and demand payment to give you access back. But what if we could stop them before they even get a foothold? That’s where ransomware kill chain disruption comes in. By breaking the sequence of steps attackers use, we can prevent major damage. In this post, we’ll explore how AI helps spot warning signs early and how automated rollback gets things back to normal fast. If you’re worried about ransomware, stick around – this could save you a lot of headaches.
Ransomware kill chain disruption is all about interrupting the attack process at key points. Attackers follow a predictable path, known as the kill chain, to infiltrate systems, spread, and encrypt data. With AI-powered tools, we can detect unusual activity before a breach happens. And if something slips through, automated rollback restores files without paying a dime to criminals. This approach is gaining traction because traditional defenses like antivirus software often react too late.

Image credit: ProServeIT – Anatomy of a Ransomware Attack
Understanding Ransomware and the Kill Chain
First off, let’s break down what ransomware really is. Ransomware is malware that encrypts your files or locks your device, making it unusable until you pay a ransom, usually in cryptocurrency. It’s like a digital kidnapper holding your data hostage. Over the years, these attacks have evolved from simple viruses to sophisticated operations run by organized crime groups.
I remember reading about the WannaCry attack back in 2017, which hit hundreds of thousands of computers worldwide. It spread like wildfire through a Windows vulnerability. Today, things are even more advanced. Attackers use tools like Ransomware-as-a-Service (RaaS), where anyone can rent ready-made attack kits. This has lowered the barrier for entry, meaning more threats out there.
Now, the cyber kill chain is a model that describes the stages of a cyber attack. It was originally developed by Lockheed Martin to help defend against advanced persistent threats. For ransomware, it maps out how attackers plan and execute their hits.
The kill chain typically has seven stages:
- Reconnaissance: Attackers gather info about the target, like employee emails or weak points in the network.
- Weaponization: They create or modify malware to exploit those weaknesses.
- Delivery: The payload is sent via phishing emails, malicious websites, or infected downloads.
- Exploitation: The malware takes advantage of vulnerabilities to gain access.
- Installation: It installs itself and persists on the system.
- Command and Control: Attackers communicate with the malware to control it remotely.
- Actions on Objectives: Finally, they encrypt files, steal data, or cause disruption.
By understanding these steps, we can focus on ransomware kill chain disruption – stopping the process early.

Image credit: MakInsights – Ransomware and the Cyber Kill Chain
If you’d like more basics on ransomware, check out our beginner’s guide to cybersecurity threats.
For a deeper dive into the kill chain framework, visit the Lockheed Martin Cyber Kill Chain page – it’s a great resource.
The Importance of Ransomware Kill Chain Disruption
Why bother disrupting the kill chain? Because prevention beats cure every time. Once ransomware encrypts your files, recovery can be costly and time-consuming, even if you have backups. Disruptions at early stages like reconnaissance or delivery can stop attacks cold.
Traditional security relies on signatures – known patterns of malware. But new variants pop up daily, making this approach outdated. Ransomware kill chain disruption shifts the focus to behavior and patterns, catching threats that don’t match known signatures.
In 2025, reports show ransomware attacks are up, with AI helping both sides. Attackers use AI to automate phishing and evasion, but defenders use it for better detection. Disrupting the chain means using proactive tools to spot and block these moves.
Businesses lose millions to downtime and ransoms. A single attack can halt operations for days. By focusing on disruption, you reduce risk and build resilience.
AI-Powered Pre-Breach Indicators
AI is a game-changer in spotting threats before they breach your systems. Pre-breach indicators are subtle signs that an attack is brewing, like unusual network traffic or login attempts.
AI analyzes vast amounts of data in real-time, looking for anomalies. For example, machine learning models can baseline normal behavior and flag deviations. If someone tries to access sensitive files at odd hours, AI raises an alert.
How does this tie into ransomware kill chain disruption? AI targets early stages. In reconnaissance, it detects port scans or data harvesting attempts. During delivery, it scans emails for phishing lures crafted by AI tools.
Common pre-breach indicators include:
- Unusual Login Patterns: Multiple failed logins or access from new locations.
- Spike in Network Traffic: Sudden outbound connections to unknown servers.
- File Access Anomalies: Rapid reading of many files, a sign of data exfiltration prep.
- Privilege Escalation Attempts: Users trying to gain higher access without reason.
AI tools like those from CrowdStrike or SentinelOne use behavioral analysis to catch these. They learn from past attacks, improving over time.
Implementing AI isn’t hard. Start with endpoint detection and response (EDR) systems that incorporate AI. These monitor devices and networks, providing alerts and even automated responses.

Image credit: Koorsen Fire & Security – AI Intrusion Detection
For more on AI in security, read this Fortinet article on AI in cybersecurity.
Also, link to our post on AI tools for small businesses for practical tips.
Automated Rollback: Recovering from Attacks
Even with the best prevention, some attacks slip through. That’s where automated rollback shines. It’s a recovery method that restores files to a pre-attack state without manual effort.
What is automated rollback? It uses snapshots or shadow copies of files to revert changes made by ransomware. Tools like SentinelOne’s Rollback feature detect encryption in progress, stop it, and restore affected files automatically.
The process works like this:
- Continuous monitoring tracks file changes.
- When ransomware starts encrypting, AI detects the pattern.
- The system quarantines the threat and rolls back modifications.
- Files return to their original state, minimizing downtime.
Benefits are huge: No ransom payments, quick recovery, and less data loss. Sophos Endpoint, for instance, uses CryptoGuard to block encryption and revert files.
To implement, integrate it into your backup strategy. Use tools that support immutable backups – ones that can’t be altered by attackers.
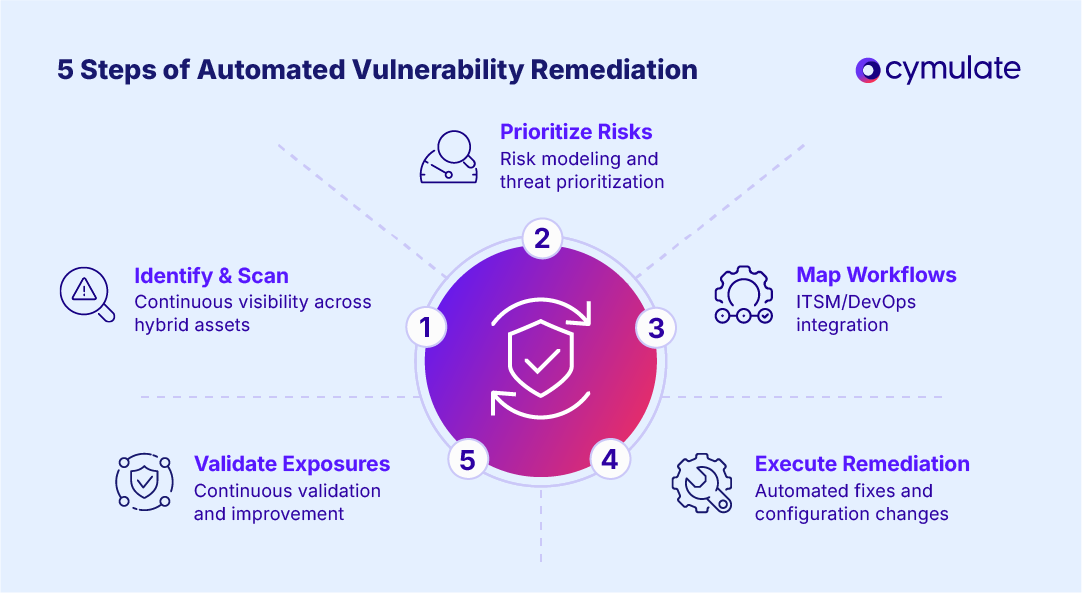
Image credit: Cymulate – Automated Vulnerability Remediation
Check out Halcyon’s ransomware defense strategy for more ideas.
See our backup best practices guide for internal advice.
Case Studies of Successful Disruptions
The Case Studies of Successful Disruptions section in the original post was a good start, but let’s expand it with more depth, real examples, and lessons learned. These stories show ransomware kill chain disruption in action — how AI spots threats early and automated rollback saves the day. I’ve pulled from documented incidents (mostly recent ones from 2024-2026) to make this practical and believable.
These aren’t just hypotheticals; they’re from companies that shared their experiences publicly to help others. They highlight why focusing on early detection and fast recovery beats paying ransoms or dealing with weeks of downtime.
Case Study 1: Guardz and the INC Ransomware Attack (2025-2026 Incident)
One of the clearest examples of autonomous AI stopping ransomware comes from a recent incident involving a new variant of INC Ransomware. The attack targeted a managed service provider’s (MSP) client environment, where the threat actor first hit one endpoint, then tried to pivot to an unmanaged staging client to spread across 36 workstations.
Here’s what happened step by step:
- The attacker got initial access (likely through phishing or a vulnerability — common entry points in the delivery stage).
- They deployed the ransomware payload, which began making modifications — over 430 file changes were detected as it tried to encrypt drives.
- SentinelOne’s endpoint agents (powered by behavioral AI) kicked in autonomously. No human in the loop needed. The system detected the malicious patterns in real time.
- In just 59 milliseconds, it terminated the process on the initial endpoint.
- When the attacker pivoted to push the ransomware wider, every agent on the 36 endpoints blocked the activity, quarantined threats, remediated, and used the built-in Rollback feature.
- Rollback relied on protected Volume Shadow Copies to restore every encrypted or modified file to its original state.
Result? Zero data loss, no encryption completed across the network, and the attack was neutralized before it could demand a ransom. The MSP avoided downtime, and the client kept operating normally.
This is a textbook ransomware kill chain disruption: AI caught behavioral anomalies during exploitation and installation stages, then rollback handled any partial damage in the actions-on-objectives phase. It shows how agentic AI (AI that acts on its own) can outpace human response times.
For more technical breakdown, check the original report on Guardz’s blog about autonomous AI vs INC Ransomware.
Case Study 2: N-able’s AI Threat Detection in MSP Environments (Ongoing 2025-2026 Deployments)
Managed service providers handle hundreds of client networks, making them prime targets for ransomware that spreads laterally. N-able’s Adlumin MDR/XDR platform uses proprietary AI to analyze billions of security events monthly.
In real deployments:
- The AI focuses on behavioral detection — spotting data exfiltration or unusual file access before encryption starts (pre-breach indicators).
- When ransomware activity is flagged (like mass file modifications), automated containment isolates endpoints instantly.
- Ransomware rollback restores Windows devices to clean states in seconds, using AI-driven analysis.
One highlighted capability: In MITRE Engenuity ATT&CK Evaluations (ongoing through 2024-2025), N-able EDR achieved 100% detection at major attack steps with zero delays and far less noise than competitors. This translates to real-world wins where threats are stopped autonomously, remediating over 70% of incidents without human intervention.
For MSPs or businesses with distributed teams, this means shifting from reactive firefighting to proactive disruption. Recovery costs average around $1.85 million per incident (per Sophos reports), but early AI intervention cuts that dramatically.
Learn more from N-able’s AI threat detection overview.
Case Study 3: Global Manufacturer — AI Isolates Endpoint During Exfiltration Attempt (Recent Anonymous Report)
A global manufacturing company faced a stealthy attack where attackers were exfiltrating data — a common precursor to ransomware double-extortion (steal first, encrypt later).
- Unusual outbound traffic spiked from one endpoint. It didn’t match any normal business process.
- The AI system (behavioral analytics-based) flagged it as anomalous.
- Automatically: Isolated the endpoint, severed the connection to command-and-control servers, and alerted the SOC team.
This stopped the kill chain at the command-and-control and actions-on-objectives stages. No encryption happened because the AI acted faster than the attackers could escalate. The company avoided a full breach, data leak, or ransom demand.
Shared on LinkedIn by a security professional, this shows how AI pre-breach indicators catch subtle moves that traditional tools miss. It’s especially useful in industrial settings where downtime costs thousands per minute.
Case Study 4: Sophos CryptoGuard in Healthcare Provider Phishing Block (Multiple Reported Wins)
Sophos often shares how their CryptoGuard technology stops ransomware mid-encryption. In one healthcare example (anonymized but representative):
- Phishing email delivered a malicious attachment (delivery stage).
- User opened it, triggering exploitation.
- As encryption began, CryptoGuard detected the unauthorized file changes.
- It blocked the process and rolled back affected files automatically.
The provider avoided paying ransom and restored operations quickly. Sophos reports similar blocks across industries, emphasizing prevention-first with AI adapting to new variants.
This ties directly to automated rollback — catching threats during the actions phase and reversing damage without backups alone.
For broader insights, see Sophos resources on ransomware protection.
Key Lessons from These Cases
Looking across these stories, a few patterns stand out for effective ransomware kill chain disruption:
- Speed matters: AI decisions in milliseconds beat human response times (often hours).
- Autonomy reduces risk: No need for constant monitoring; systems act first, then alert.
- Rollback is the safety net: Even if something slips past detection, restoring files prevents payout pressure.
- Behavioral focus wins: Signatures fail against new variants, but AI spots intent (e.g., mass encryption patterns).
- Layered defense: Combining pre-breach AI alerts with rollback covers the full kill chain.
These examples prove that investing in AI-powered tools isn’t futuristic — it’s working now, saving organizations from major losses.
If you’re evaluating solutions, start small: Test EDR with rollback features on a pilot group. Simulate attacks (ethically) to see disruption in action.
For more inspiration, read about SentinelOne’s platform capabilities or check our related post on AI tools for small business cybersecurity.
Best Practices for Implementation
To get started:
- Assess your current setup. Identify weak points in your kill chain defenses.
- Deploy AI tools for monitoring. Choose ones with pre-breach detection.
- Set up automated responses, including rollback.
- Train staff on phishing awareness.
- Regularly test with simulations.
- Keep software updated to close vulnerabilities.
Combine with multi-factor authentication and segmentation.
For advanced tips, visit Vectra AI’s kill chain guide.
Link to our simulation testing post.

Image credit: Fortinet – Malware Indicators
Future Trends in Ransomware Defense
Looking ahead, AI will evolve. Attackers are using AI for faster attacks, but defenders are stepping up with autonomous agents. Expect more integration of AI with zero-trust models.
Quantum computing might break encryptions, but AI could predict those risks too.
Stay informed with SANS Institute resources.
Conclusion
Ransomware kill chain disruption is key to staying safe in a dangerous digital world. With AI-powered pre-breach indicators, we catch threats early, and automated rollback ensures quick recovery. Implement these strategies, and you’ll be better protected.
Remember, cybershieldguide is ongoing. Keep learning and updating your defenses.
If you found this helpful, share it or check our other cybershieldguide posts.
Share this content:













Post Comment