Quantum Computing Threats to Encryption
Imagine logging into your online banking app one morning only to find that every transaction from the past decade has been decrypted overnight. Or waking up to news that sensitive government secrets, medical records, and even your family photos stored in the cloud are suddenly public. Sounds like a nightmare scenario from a sci-fi movie? Unfortunately, this is the real-world risk posed by quantum computing threats to encryption — and it’s closer than most people realize.
As we sit here in February 2026, quantum computers aren’t breaking encryption left and right yet. But the warning signs are everywhere. Nation-states are already scooping up encrypted data today, banking on the fact that tomorrow’s quantum machines will crack it open. Google just issued a major alert about “store now, decrypt later” attacks. Bitcoin developers are rushing new protections into the protocol. And governments worldwide are pouring billions into post-quantum upgrades.
In this comprehensive guide, we’ll break down exactly what quantum computing threats to encryption mean for you, your business, and the future of the internet. We’ll use simple language, real examples from 2026, and practical steps you can take right now. Whether you’re a complete beginner or a tech professional, by the end you’ll understand why this matters and how to stay safe.

Image credit: Google’s quantum computer setup (Source: The New York Times)
What Exactly Are Quantum Computing Threats to Encryption?
Let’s start with the basics. Regular computers — the ones in your phone or laptop — use bits that are either 0 or 1. Encryption today works because certain math problems (like factoring huge numbers) are incredibly hard for these classical computers to solve. It would take billions of years to crack a good RSA key with today’s supercomputers.
Quantum computers flip that script completely. They use qubits that can be 0, 1, or both at the same time thanks to something called superposition. They can also link qubits together through entanglement, so changing one instantly affects another, no matter the distance.
This isn’t just faster computing — it’s a completely different way of processing information. And one specific quantum trick, called Shor’s algorithm, can factor those huge numbers in hours instead of centuries. That’s the core of the quantum computing threats to encryption.
But don’t worry — we’ll unpack all of this step by step.
How Quantum Computers Actually Work (Without the Jargon)
Think of a regular bit like a light switch: on or off. A qubit is more like a spinning coin in the air — it’s both heads and tails until you look at it. That’s superposition.
Now imagine two coins spinning together. Measure one, and the other instantly shows the matching result, even if it’s across the room. That’s entanglement.
These properties let quantum computers explore millions of possibilities simultaneously. For encryption-breaking, it means they can try every possible factor of a big number at once instead of one by one.
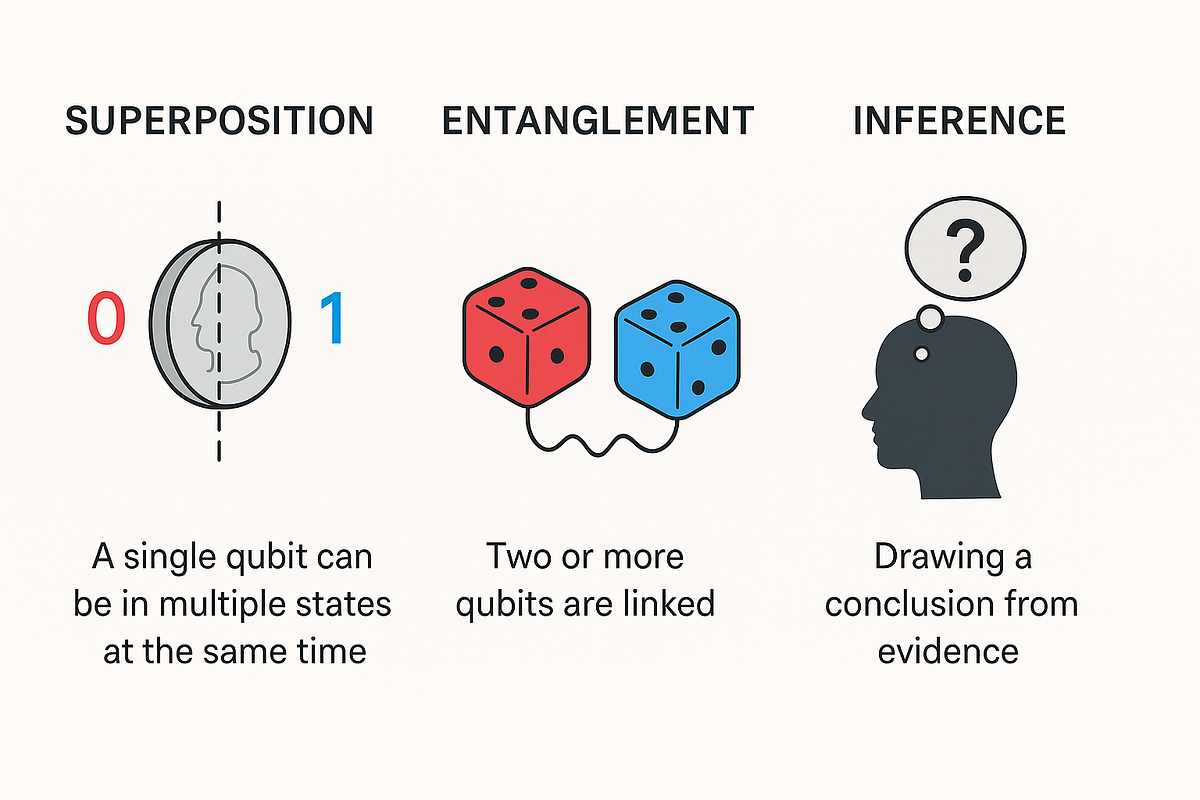
Image credit: Simple explanation of superposition and entanglement (Source: Medium article on quantum concepts)
Here’s a fun analogy I like: Cracking classical encryption is like trying every key on a massive keyring one by one in a dark room. A quantum computer turns on the lights and can test every key at the exact same time.
Of course, real quantum machines today are noisy and error-prone. They lose their “quantumness” quickly because of heat, vibration, or even cosmic rays. That’s why we don’t have full-scale quantum computers breaking banks yet — but the progress in 2025-2026 has been staggering.
The Two Big Quantum Algorithms That Threaten Encryption
There are two main quantum algorithms everyone in cybersecurity talks about:
- Shor’s Algorithm (the big one for public-key encryption)
- Grover’s Algorithm (the one that affects symmetric encryption too)
Shor’s algorithm is the star of the show for quantum computing threats to encryption. Developed back in 1994 by Peter Shor, it can factor large numbers exponentially faster than any classical method. RSA and ECC — the encryption protecting 99% of the internet, HTTPS, VPNs, digital signatures, and cryptocurrencies — all rely on the difficulty of factoring or solving discrete logarithms.
A powerful enough quantum computer running Shor’s could derive your private key from a public one in minutes.
Grover’s algorithm is less dramatic but still important. It speeds up brute-force searches by “square root” time. So a 256-bit AES key, which is safe against classical computers, would effectively offer only 128-bit security against a quantum one. That’s still pretty strong, but it means we might need to double key lengths in the future.
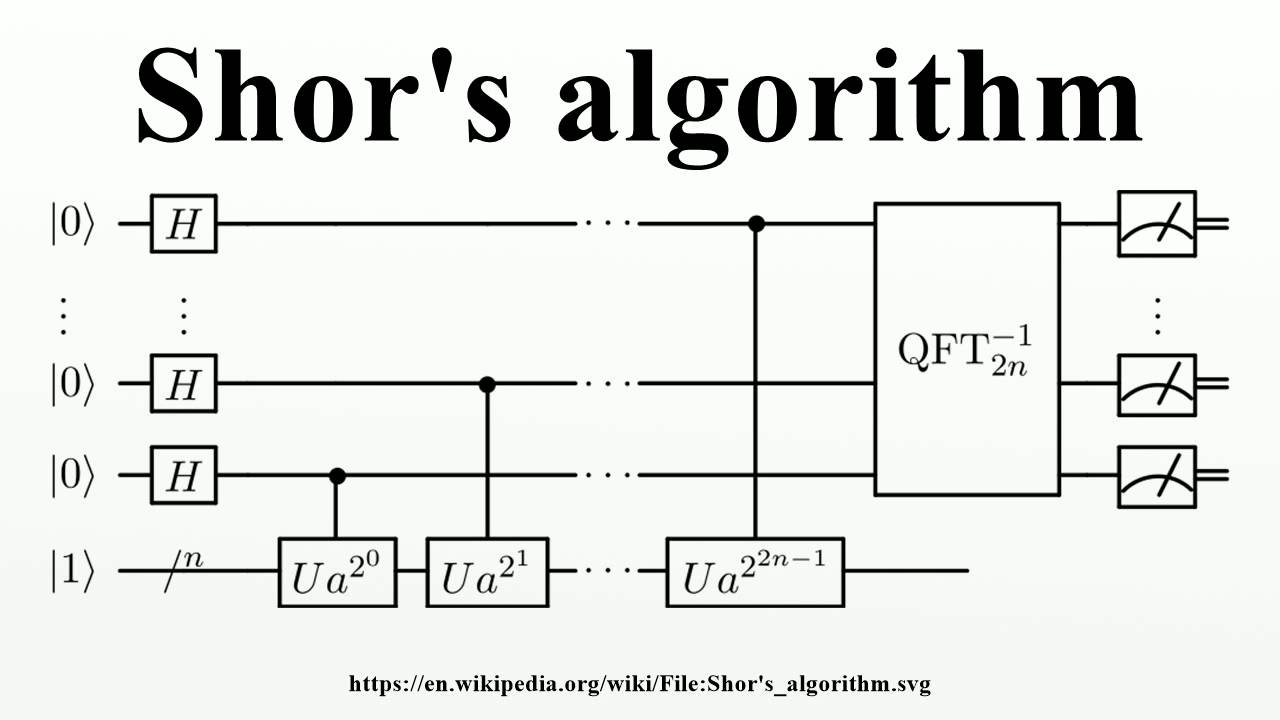
Image credit: Shor’s algorithm circuit diagram (Source: Wikipedia / educational resources)
Current State of Quantum Computing in 2026 — Are We There Yet?
Good news first: No one has a cryptographically relevant quantum computer (CRQC) capable of running Shor’s on real 2048-bit RSA keys today.
But the hardware is improving fast. IBM has clear roadmaps toward fault-tolerant systems by 2029. Google demonstrated “below threshold” error correction in late 2025 with their Willow chip — meaning adding more qubits actually reduced errors instead of making them worse. That’s a huge milestone.
Recent estimates from researchers suggest breaking RSA-2048 might need somewhere between 100,000 to a few million physical qubits with good error correction, depending on the architecture. We’re talking years, not decades, for the first demonstrations on smaller keys.
Major players like IBM, Google, Microsoft (with their Majorana qubits breakthrough in early 2026), and even startups are racing ahead. China is investing heavily too.
The real threat right now isn’t a sudden “quantum apocalypse” tomorrow. It’s the harvest now, decrypt later (HNDL) strategy.
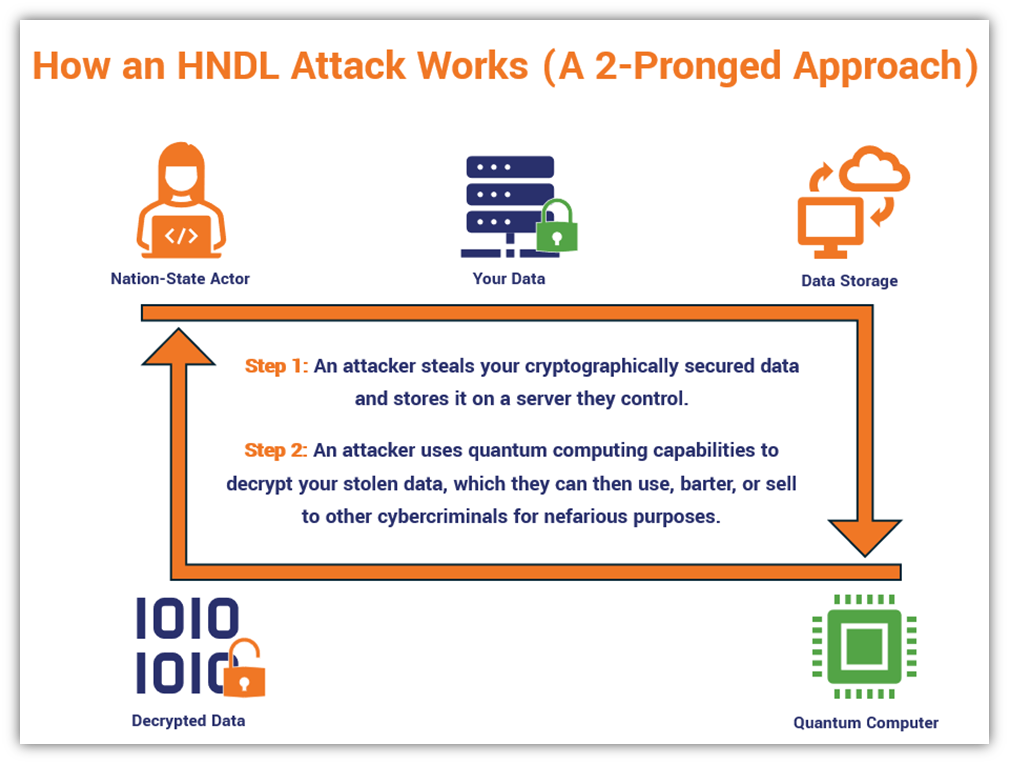
Image credit: HNDL attack explanation (Source: The SSL Store / cybersecurity blogs)
Nation-states and well-funded actors are vacuuming up encrypted traffic today — emails, financial records, health data, intellectual property — and storing it. They know that in 5-15 years, quantum computers will unlock it all. Google explicitly warned about this in their February 2026 blog post, calling on governments and industry to act immediately.
This is why quantum computing threats to encryption are an urgent issue in 2026, even if the actual breaking happens later.
Who Is Most at Risk from These Quantum Threats?
Pretty much everyone using modern technology:
- Governments and military: Classified communications could be retroactively decrypted.
- Banks and financial institutions: Billions in transactions rely on RSA/ECC.
- Healthcare: Patient records must stay private for decades.
- Cryptocurrency users: Bitcoin and others have exposed public keys that could be vulnerable (recent estimates put millions of BTC at risk, including potentially Satoshi’s coins).
- Regular people: Your emails, cloud storage, VPN connections, smart home devices — all could be exposed years later.
In the Bitcoin world, developers just formalized BIP 360 in early 2026 to move toward quantum-resistant addresses. About 7 million BTC (worth hundreds of billions) sit in vulnerable formats right now.

Image credit: RSA public key encryption flow (Source: Medium cryptography guides)
Post-Quantum Cryptography: Our Best Defense
The good news? We already have the solutions. Post-quantum cryptography (PQC) uses math problems that even quantum computers struggle with — things like lattice problems, hash-based signatures, and code-based systems.
NIST has been leading the charge since 2016. By 2024 they standardized three main algorithms:
- ML-KEM (formerly Kyber) for key encapsulation
- ML-DSA (formerly Dilithium) for digital signatures
- SLH-DSA (formerly Sphincs+) as a backup signature scheme
In 2025 they added HQC as another KEM option for diversity. Draft standards incorporating HQC were expected early 2026.
These algorithms are designed to work on classical computers but resist quantum attacks. The transition is happening, but it’s not simple.

Image credit: Post-quantum cryptography levels in messaging apps (Source: LinkedIn cybersecurity discussions)
Step-by-Step Guide: How to Prepare for Quantum Computing Threats to Encryption
You don’t need to be a cryptographer to start protecting yourself. Here’s a practical roadmap:
- Inventory your cryptography — Find where RSA, ECC, or other vulnerable algorithms are used in your systems.
- Prioritize high-risk data — Anything that needs to stay secret for 10+ years (medical records, trade secrets, government data) should be upgraded first.
- Implement hybrid cryptography — Use both classical and post-quantum algorithms together during transition. This is what many vendors are doing now.
- Build crypto agility — Design systems so you can swap algorithms easily without rewriting everything.
- Test and pilot — Start small with NIST-approved PQC in non-critical environments.
- Update protocols — TLS 1.3 already supports some PQC experiments. Push vendors for native support.
- Stay informed — Follow NIST, CISA, and industry groups.
For businesses, the migration could take 5-15 years according to recent studies. Start now.
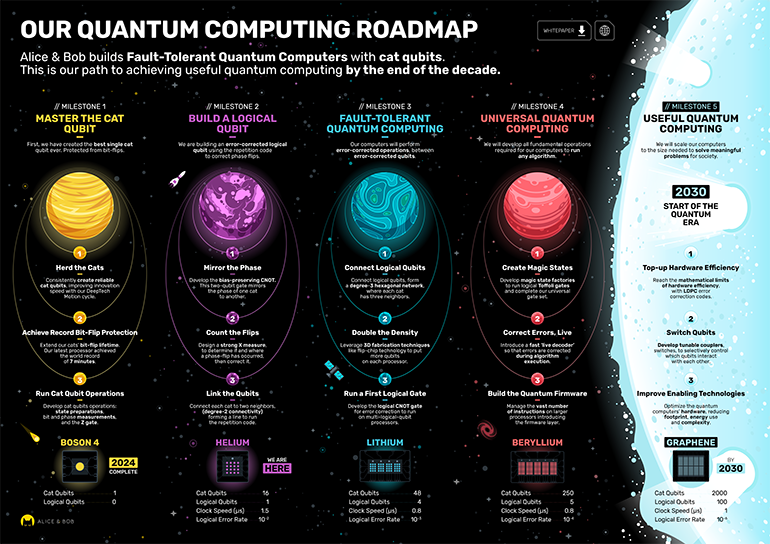
Image credit: Example quantum computing roadmap toward useful systems (Source: Alice & Bob company materials)
Challenges We’ll Face During the Transition
This isn’t just flipping a switch. Post-quantum algorithms often have larger keys and signatures, which means more bandwidth and storage. Performance can be slower on some devices.
Legacy systems in critical infrastructure (power grids, transportation) are especially tricky. Many run on hardware from the 1990s that’s hard to update.
Skills shortage is real too — not enough people understand both quantum and classical crypto.
Cost is another factor. Large organizations might spend millions on audits and upgrades.
But the alternative — getting caught flat-footed when quantum computers mature — is far worse.
Real-World Examples and What’s Happening Right Now (2026)
- Google’s warning: In February 2026, Google’s leadership called for immediate action on PQC migration.
- Bitcoin’s move: BIP 360 aims to protect against quantum attacks on exposed public keys.
- Government mandates: US federal systems target full PQC by 2035. Defense contractors must use it in new systems after 2027.
- Financial sector: Banks are running pilots with hybrid PQC for payments and messaging.
- Messaging apps: Signal and others are experimenting with PQC key exchanges to counter HNDL.
Beyond the Threats: The Positive Side of Quantum Computing
While we’re focused on risks here, quantum computers will also revolutionize security in other ways — better random number generation, quantum key distribution (QKD) for ultra-secure links, and faster threat detection using quantum machine learning.
The same technology creating threats can help solve them.
Conclusion: Act Now to Stay Secure Tomorrow
Quantum computing threats to encryption represent one of the most significant shifts in cybersecurity history. It’s not about panic — it’s about smart preparation.
The data we encrypt today might be decrypted in 2035. The systems we build now need to last decades. By understanding these threats, inventorying our crypto, and migrating to post-quantum standards, we can turn this challenge into an opportunity for stronger, future-proof security.
Don’t wait for the first headline about a quantum break. Start your journey today.
What are you doing to prepare? Share in the comments or check our related guides:
- Basics of Modern Encryption
- Understanding Quantum Computing for Beginners
- Complete Guide to Post-Quantum Migration
Stay safe out there — the quantum era is coming, and we can be ready for it.
Frequently Asked Questions About Quantum Computing Threats to Encryption
Q: Will quantum computers break all encryption? No. Symmetric encryption like AES-256 will still be strong (just use longer keys). The main targets are public-key systems like RSA and ECC.
Q: When will quantum computers actually break encryption? Expert estimates range from 2030-2040 for practical attacks on RSA-2048. But HNDL makes the threat immediate.
Q: Is my data safe if I use VPN or HTTPS? Currently yes, but upgrade to hybrid or PQC versions as they become available.
Q: What should small businesses do? Start with a crypto inventory using free tools. Prioritize cloud providers and vendors that offer PQC options. Follow NIST guidelines.
Q: Are there any quantum-safe alternatives available today? Yes — NIST standards are ready for testing and early deployment in many libraries (OpenSSL, BoringSSL, etc.).
Q: How does this affect cryptocurrencies? Bitcoin and Ethereum are actively working on quantum-resistant upgrades. Move funds to new quantum-safe addresses when available.
Share this content:














Post Comment