Privacy Enhancing Technologies (PETs)
In our connected world, every click, purchase, and health check generates personal data. Companies and governments collect this information to improve services, but it often feels like your privacy is the price you pay. Privacy Enhancing Technologies (PETs) change that equation completely.
These smart tools let organizations analyze and use data without exposing sensitive details about you. Whether it’s your shopping history or medical records, PETs keep things private while still delivering real value.
If you’ve ever felt uneasy about how your data is handled online, you’re not alone. Millions of people worry about breaches, tracking, and misuse. Privacy Enhancing Technologies offer practical solutions that put control back in your hands – or at least make sure no single party can see everything.
This guide explains everything about Privacy Enhancing Technologies in simple terms. You’ll discover what they are, how they work, real examples from daily life, and why they’re becoming essential in 2026. By the end, you’ll understand how PETs protect everyday people like you and why businesses are rushing to adopt them.
What Are Privacy Enhancing Technologies (PETs)?
Privacy Enhancing Technologies, often called PETs, are a family of tools, methods, and systems designed to protect personal information. They minimize how much data gets collected, maximize security, and give individuals more control.
Think of PETs as invisible shields around your data. Traditional systems might copy your full information to a central server for analysis. Privacy Enhancing Technologies let useful insights emerge without ever revealing the raw details.
For instance, a hospital might want to study disease patterns across thousands of patients. Without PETs, they’d need to share everyone’s full medical history – risking leaks. With Privacy Enhancing Technologies, the hospital gets accurate trends while patient identities stay hidden.
The core idea is simple: use data without abusing it. PETs achieve this through clever math, cryptography, and clever design tricks. They follow key privacy principles like data minimization (collect only what you need) and purpose limitation (use data only for agreed reasons).

Image Credit: bulletproof.co.uk
According to experts at organizations like the OECD and ENISA, Privacy Enhancing Technologies fall into “hard” and “soft” categories. Hard PETs ensure no one – not even the system operator – can access raw data. Soft PETs rely more on policies and access controls but still add strong protections.
Why do they matter so much right now? Data breaches hit records every year. Regulations like GDPR in Europe and similar laws worldwide demand better protection. At the same time, AI and big data need massive amounts of information to work well. Privacy Enhancing Technologies solve this tension perfectly.
They aren’t just for tech giants. Small businesses, researchers, governments, and even individuals use versions of PETs today. Your smartphone’s privacy settings often include basic PET features, like limiting app tracking.
In short, Privacy Enhancing Technologies let the digital world function smoothly while respecting your right to privacy. They turn “collect everything” into “analyze safely.”
A Quick History of Privacy Enhancing Technologies
Privacy Enhancing Technologies didn’t appear overnight. The ideas started in the 1970s and 1980s with early cryptography research. People realized that as computers spread, so would privacy risks.
The 1990s brought big steps forward. Researchers developed concepts like anonymous communication networks (think early versions of Tor). The OECD published reports highlighting the need for tools that protect data while allowing its use.
By the early 2000s, terms like “Privacy Enhancing Technologies” became common. The European Union and Canada’s privacy commissioners studied them seriously. A 2017 report from Canada’s Office of the Privacy Commissioner called PETs essential for modern data protection.
The 2010s saw real-world adoption. Apple introduced differential privacy in iOS in 2016 to improve Siri and emoji suggestions without tracking individuals. Google started using federated learning for its keyboard app around the same time.
Fast forward to 2025-2026. Privacy Enhancing Technologies exploded in popularity. New regulations, AI boom, and high-profile breaches pushed companies to invest heavily. Market reports show the PET sector growing rapidly toward tens of billions of dollars by 2030.
Today, governments like the EU integrate PETs into health data spaces. Banks use them for fraud detection across borders. Even advertising platforms experiment with Privacy Enhancing Technologies to target ads without creepy tracking.
This evolution shows Privacy Enhancing Technologies moving from research labs to everyday tools. The future looks even brighter as they become standard in software and apps.

Image Credit: oecd.org
Main Types of Privacy Enhancing Technologies Explained Simply
Many different Privacy Enhancing Technologies exist, but a few stand out as game-changers. Let’s break down the most important ones in plain English.
Differential Privacy: Adding Just Enough Noise
Differential Privacy is one of the most popular PETs. It adds a small amount of random “noise” to data or query results. This makes it nearly impossible to identify any single person while keeping overall patterns accurate.
Imagine a clear group photo of a crowd. Differential privacy is like adding a gentle fog – you still see there are many people and general features, but you can’t pick out your friend’s exact face.
How does it work technically? When a database answers a question (like “How many users are over 30?”), it adds tiny random numbers. The noise is carefully calculated so individual records don’t affect the answer much, but group trends stay reliable.
Apple uses differential privacy to learn which emojis people use most without knowing which user typed what. Google applies it in many products too.
Pros: Strong mathematical guarantees, relatively easy to add to existing systems, works well for statistics.
Cons: Too much noise can make results less useful; needs careful tuning.
Real example: In 2026, public health agencies use differential privacy to share COVID-like trend data across regions without exposing patient details.
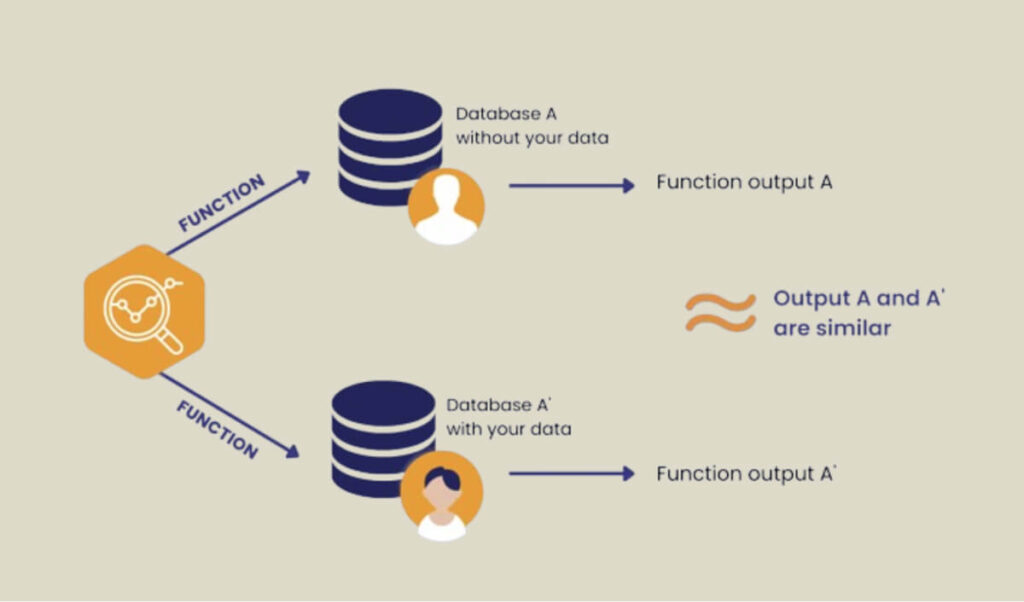
Image Credit: pvml.com
This technique proves incredibly powerful for census data, research, and any situation where you need accurate counts without individual exposure.
Homomorphic Encryption: Math on Locked Data
Homomorphic Encryption sounds complex, but the idea is beautiful. It lets you perform calculations on encrypted data without decrypting it first.
Picture sending your locked diary to a friend. They can add notes or calculate totals on the locked pages using special math, then send it back. Only you have the key to read the final result.
There are partial and fully homomorphic versions. Fully homomorphic encryption (FHE) allows any computation – addition, multiplication, even complex AI models – on encrypted data.
In practice, a bank could let an analytics company run fraud-detection algorithms on customer transaction data without ever seeing the actual numbers or account details.
Companies like Microsoft and IBM research practical FHE tools. In 2026, it’s becoming feasible for more use cases as computing power improves.
Pros: Extremely strong protection – data stays encrypted the whole time.
Cons: Currently slow and computationally expensive, though getting better fast.

Image Credit: chain.link
Privacy Enhancing Technologies like this are perfect for cloud computing where you don’t fully trust the provider.
Secure Multi-Party Computation (SMPC): Teamwork Without Sharing Secrets
Secure Multi-Party Computation lets multiple parties calculate something together while keeping their individual inputs private.
It’s like several people wanting to find the average salary in a group without anyone revealing their own pay. They each add secret numbers and share partial results in a way that only the final average emerges.
SMPC uses clever cryptographic protocols so no party sees others’ data.
Use cases include secure auctions (bidders don’t reveal bids until winner is decided), private voting, or companies comparing customer lists for overlaps without exposing full databases.
In finance, banks use SMPC to detect money laundering patterns across institutions without sharing customer data.
Pros: Enables collaboration that was impossible before.
Cons: Can be complex to set up and slower than normal computation.
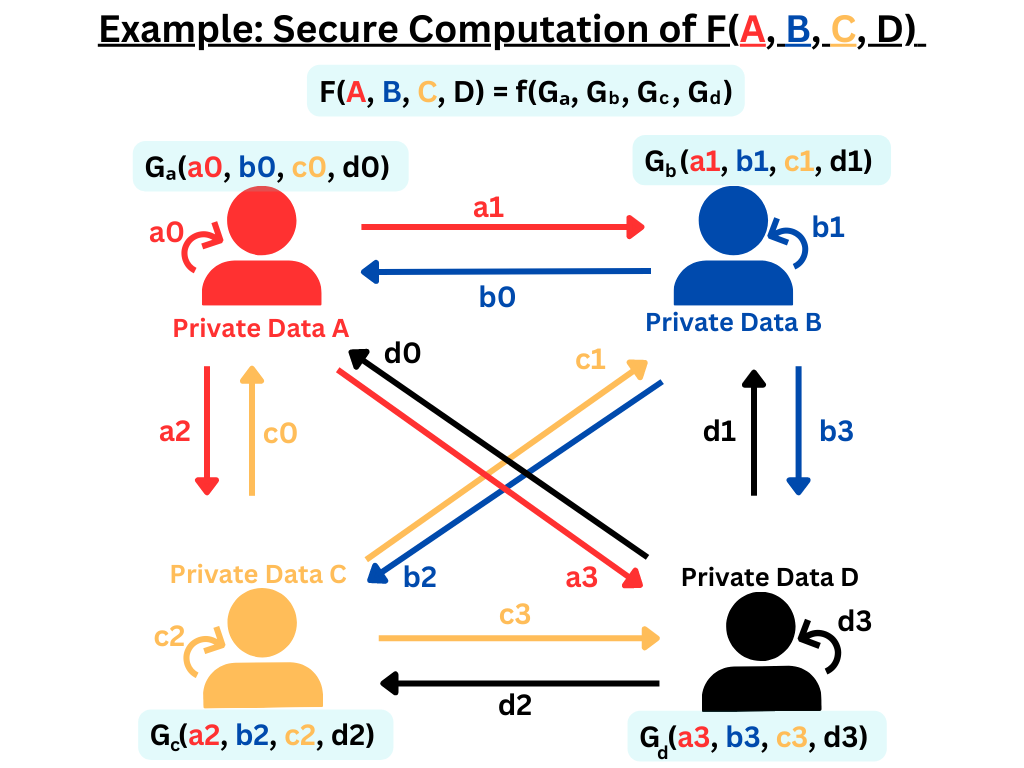
Image Credit: iudx.org.in
This PET shines when trust between organizations is low but cooperation is needed.
Zero-Knowledge Proofs (ZKPs): Prove It Without Showing It
Zero-Knowledge Proofs let you prove a statement is true without revealing any extra information.
Classic example: Prove you are over 18 without showing your birthdate or ID. Or in crypto, prove you have enough money for a transaction without revealing your balance.
The prover convinces the verifier through a series of mathematical challenges. The verifier learns only that the claim is true (or false).
Zcash cryptocurrency popularized ZKPs for private transactions. Blockchains now use them widely for scalability and privacy.
In 2026, governments explore ZKPs for digital IDs – verify citizenship without exposing full passport details.
Pros: Incredible privacy with verifiable truth.
Cons: Computationally intensive for complex proofs, though libraries are improving.

Image Credit: horizen.io
Privacy Enhancing Technologies using ZKPs feel almost magical – perfect security through math.
Federated Learning: Train AI Without Moving Data
Federated Learning trains machine learning models across many devices or servers without centralizing the raw data.
Each phone or hospital trains a local model on its own data. Only the model updates (not the data) get sent to a central server, which combines them into a better global model.
Your phone improves Google’s keyboard predictions based on your typing, but Google never sees what you actually typed.
Hospitals can build better cancer detection AI by learning from each other’s patient scans without sharing sensitive images.
Pros: Keeps data local, reduces breach risks, great for mobile and edge devices.
Cons: Communication overhead, potential for biased models if some participants drop out.
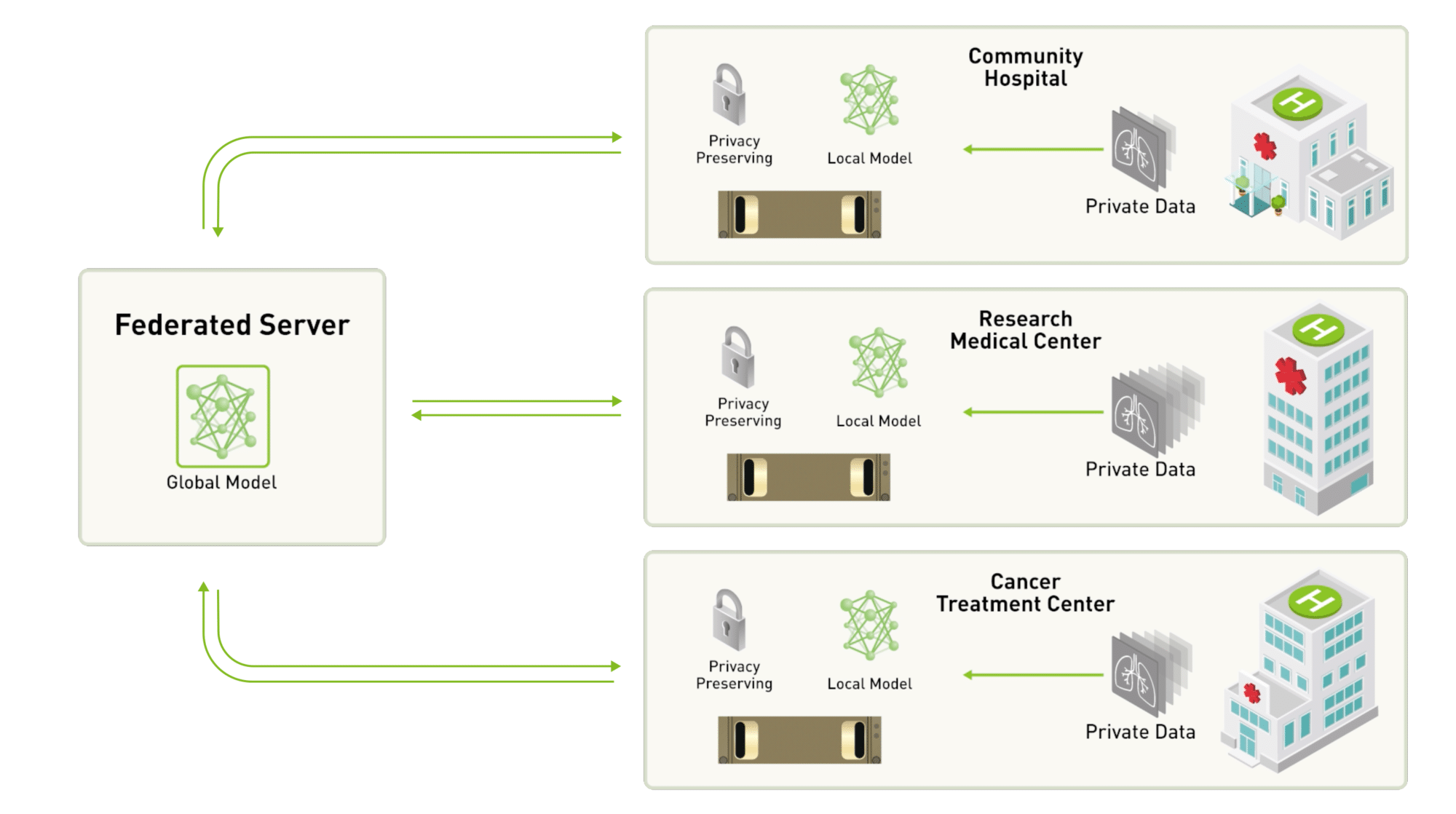
Image Credit: blogs.nvidia.com
This PET powers much of modern privacy-friendly AI development.
Other notable Privacy Enhancing Technologies include synthetic data (fake but realistic datasets), trusted execution environments (secure chips), and advanced anonymization techniques.
Real-World Applications of Privacy Enhancing Technologies
Privacy Enhancing Technologies aren’t just theory – they’re solving problems across industries every day.
Healthcare: Saving Lives While Protecting Patients
Healthcare generates incredibly sensitive data. PETs let researchers collaborate safely.
The European Health Data Space (launched around 2025) uses federated learning, homomorphic encryption, and pseudonymization so doctors across countries can train AI for early disease detection without moving patient records.
Hospitals share insights on treatment effectiveness while keeping identities hidden. Pharmaceutical companies analyze trial data across sites without exposing participant details.
One real case: Researchers used Privacy Enhancing Technologies to study rare diseases by pooling data from multiple hospitals securely. They found patterns faster without privacy violations.
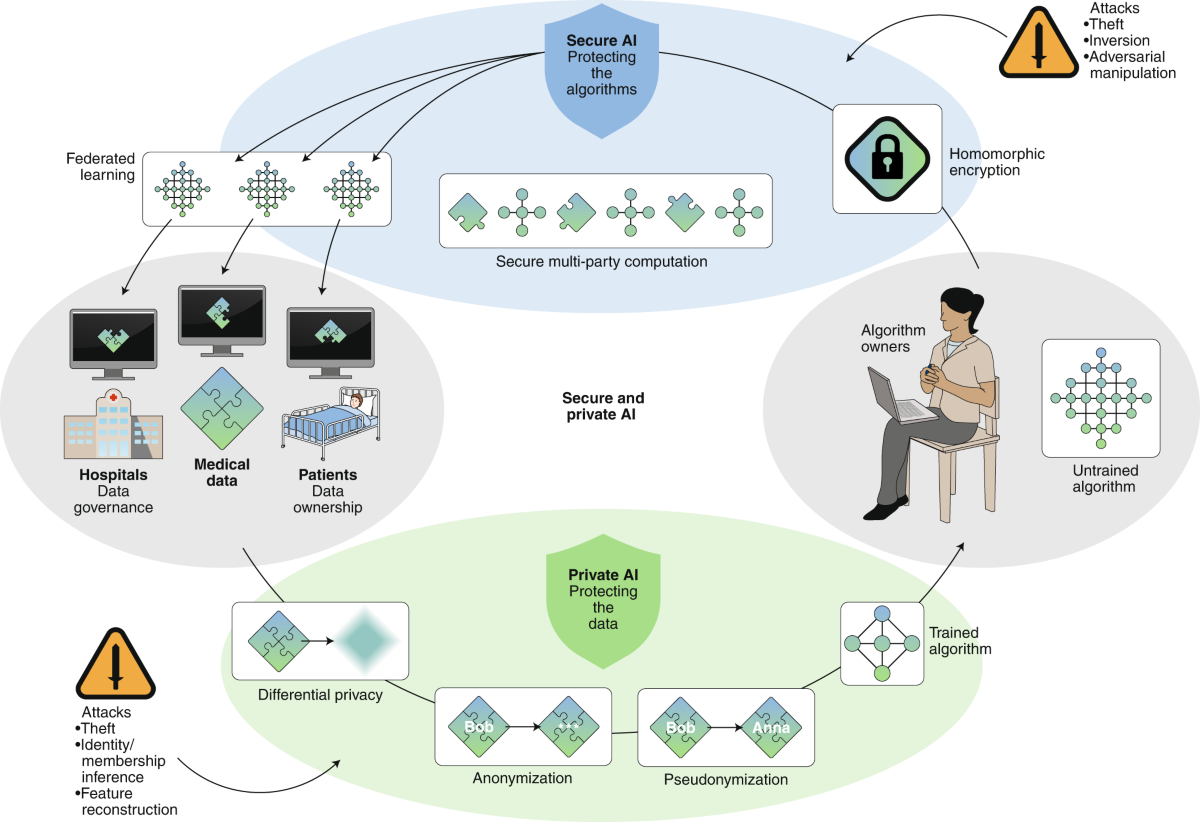
Image Credit: nature.com
In 2026, telemedicine apps use differential privacy to improve symptom checkers based on anonymous user reports.
Finance: Smarter Fraud Detection Without Sharing Secrets
Banks face strict rules about sharing customer data. Secure Multi-Party Computation lets them jointly detect fraud rings across institutions.
Mastercard ran proofs-of-concept using federated learning and homomorphic encryption to share financial crime intelligence internationally while complying with cross-border laws.
Credit bureaus explore PETs to calculate risk scores without exposing full credit histories.
Personal finance apps use zero-knowledge proofs so users prove income for loans without uploading bank statements.
Advertising and Marketing: Targeted Without Tracking
The end of third-party cookies forced the ad industry to adopt Privacy Enhancing Technologies.
Platforms now use federated analytics and trusted execution environments for audience matching. Google’s confidential matching lets advertisers upload lists that get processed securely – no one, not even Google, sees the raw data.
Differential privacy helps measure campaign effectiveness without individual tracking.
Marketers get better results while respecting user privacy – a win-win.
AI and Machine Learning: Responsible Innovation
AI needs data, but privacy laws limit collection. Federated learning and synthetic data solve this.
Companies train large language models on decentralized data. Privacy Enhancing Technologies prevent memorization of personal information.
Governments use PETs for public AI projects, like traffic optimization from anonymous phone location patterns.
Government and Census: Accurate Stats, Real Privacy
The US Census Bureau has long used differential privacy techniques. Other countries follow suit for population statistics.
Voting systems explore secure multi-party computation and zero-knowledge proofs for verifiable yet secret ballots.
Tax authorities could analyze compliance trends across regions without seeing individual returns.
Key Benefits of Using Privacy Enhancing Technologies
Adopting Privacy Enhancing Technologies brings clear advantages:
- Stronger Privacy Protection: Reduce breach impact since less raw data moves around.
- Regulatory Compliance: Easier to meet GDPR, CCPA, and future laws by design.
- Better Customer Trust: People prefer services that protect data – leading to higher engagement.
- New Business Opportunities: Collaborate with partners you couldn’t before.
- Innovation Enablement: Use sensitive data for AI and analytics safely.
- Cost Savings Long-Term: Fewer fines, less breach cleanup.
Businesses report improved reputation and competitive edges when using Privacy Enhancing Technologies.
Challenges and Limitations of Privacy Enhancing Technologies
No technology is perfect. Privacy Enhancing Technologies face real hurdles:
- Performance Overhead: Many PETs slow down computations or require more computing power.
- Complexity: Implementing them needs specialized skills – not every team has experts.
- Utility Trade-offs: Adding noise or encryption can slightly reduce accuracy.
- Cost: Initial setup and ongoing resources can be expensive, though prices drop as tools mature.
- Interoperability: Different systems don’t always work together smoothly yet.
- Regulatory Uncertainty: Laws are still catching up with these new methods.
- Adoption Barriers: Organizations worry about changing established processes.
Despite these, progress is rapid. In 2026, open-source libraries and cloud services make PETs more accessible than ever.
Many experts recommend starting small – layer simple techniques like differential privacy first, then add advanced ones.

Image Credit: ipc.on.ca
The Future of Privacy Enhancing Technologies in 2026 and Beyond
Privacy Enhancing Technologies are just getting started. By late 2026, expect:
- Wider integration into standard software (your browser, apps, and cloud services will use them by default).
- Quantum-resistant versions to prepare for future computers.
- AI-powered PETs that automatically choose the best protection method.
- Standardized frameworks making implementation easier.
- Greater use in Web3 and decentralized applications.
- Global collaboration standards from bodies like OECD and NIST.
The market will keep expanding as more regulations require privacy-by-design. Everyday users will benefit without even noticing the technology working behind the scenes.
Imagine a world where personalized services feel magical but never invasive. Privacy Enhancing Technologies make that possible.
For more on upcoming trends, check external resources like the OECD Emerging Privacy-Enhancing Technologies report or Martin Fowler’s introduction to PETs.
Internally, read our guide on data privacy basics for foundational knowledge or GDPR compliance tips.
How Individuals and Businesses Can Start Using Privacy Enhancing Technologies Today
For individuals:
- Choose apps and services that advertise privacy features (look for differential privacy mentions).
- Use tools like privacy-focused browsers or VPNs with strong PET elements.
- Support companies investing in these technologies.
- Enable privacy settings that limit data sharing.
For businesses:
- Assess current data practices and identify high-risk areas.
- Start with easy wins like differential privacy in analytics.
- Partner with PET providers or use cloud services offering built-in tools.
- Train teams on privacy-by-design.
- Pilot projects in one department before full rollout.
- Consult resources like NIST privacy guidelines or ENISA PET reports.
Small steps today build strong privacy habits for tomorrow.
Case Studies: Privacy Enhancing Technologies in Action
Google’s use of federated learning in Gboard improved typing predictions for billions while keeping keystrokes private.
Apple’s differential privacy powers features across iOS and macOS, balancing utility with user trust.
Mastercard’s cross-border fraud detection pilots using multiple PETs showed faster threat response and easier compliance.
EU health projects demonstrated how PETs unlock medical research across borders safely.
These examples prove Privacy Enhancing Technologies deliver measurable benefits right now.
Conclusion: Embrace Privacy Enhancing Technologies for a Better Digital Future
Privacy Enhancing Technologies (PETs) represent one of the most hopeful developments in our data-driven world. They show it’s possible to have both powerful insights and real privacy.
Whether you’re an individual wanting safer apps or a business leader building trust, PETs offer practical paths forward. As we move deeper into 2026 and beyond, these technologies will become as normal as HTTPS or two-factor authentication.
The key is understanding and supporting them. By choosing privacy-respecting services and encouraging adoption, we all help create a digital ecosystem where data serves people – not the other way around.
What do you think about Privacy Enhancing Technologies? Have you encountered them in apps you use? Share in the comments below, and don’t forget to explore more on our blog, like how to protect your online identity.
Stay informed, stay private, and keep learning about tools that put you first.
Share this content:














Post Comment