How to Build Cyber Resilience Against AI-Powered Attacks
Businesses everywhere are scrambling to protect themselves. That’s where cyber resilience against AI-powered attacks comes…
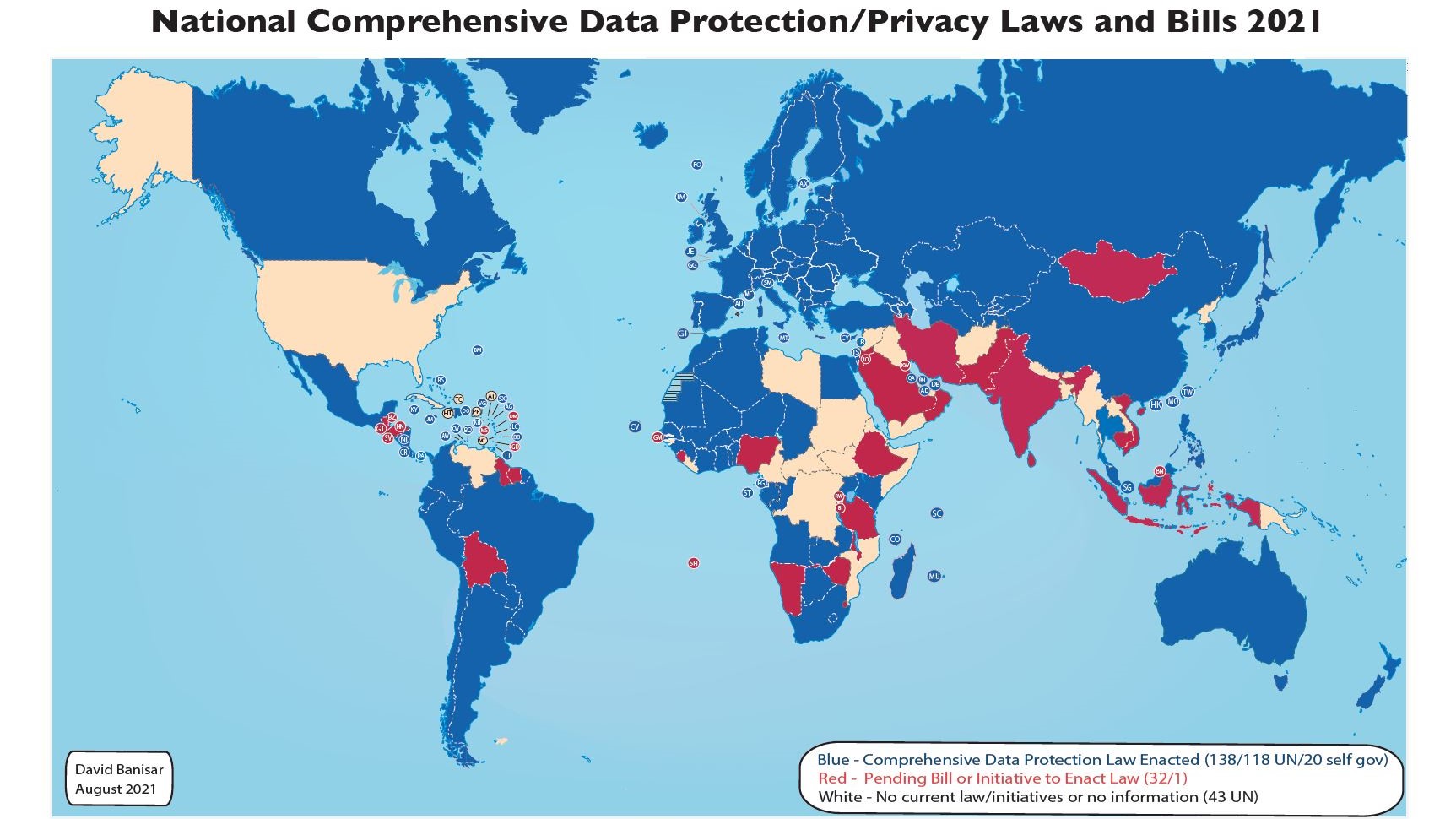
How Regulatory Volatility Is Shaping Cyber Strategies in 2026
Regulatory Volatility Is Shaping Cyber Strategies more than ever before. Rules aren’t just getting stricter.…
Fighting AI-Generated Phishing: Advanced Detection Methods
Fighting AI-Generated Phishing has become one of the biggest challenges for individuals and businesses in…
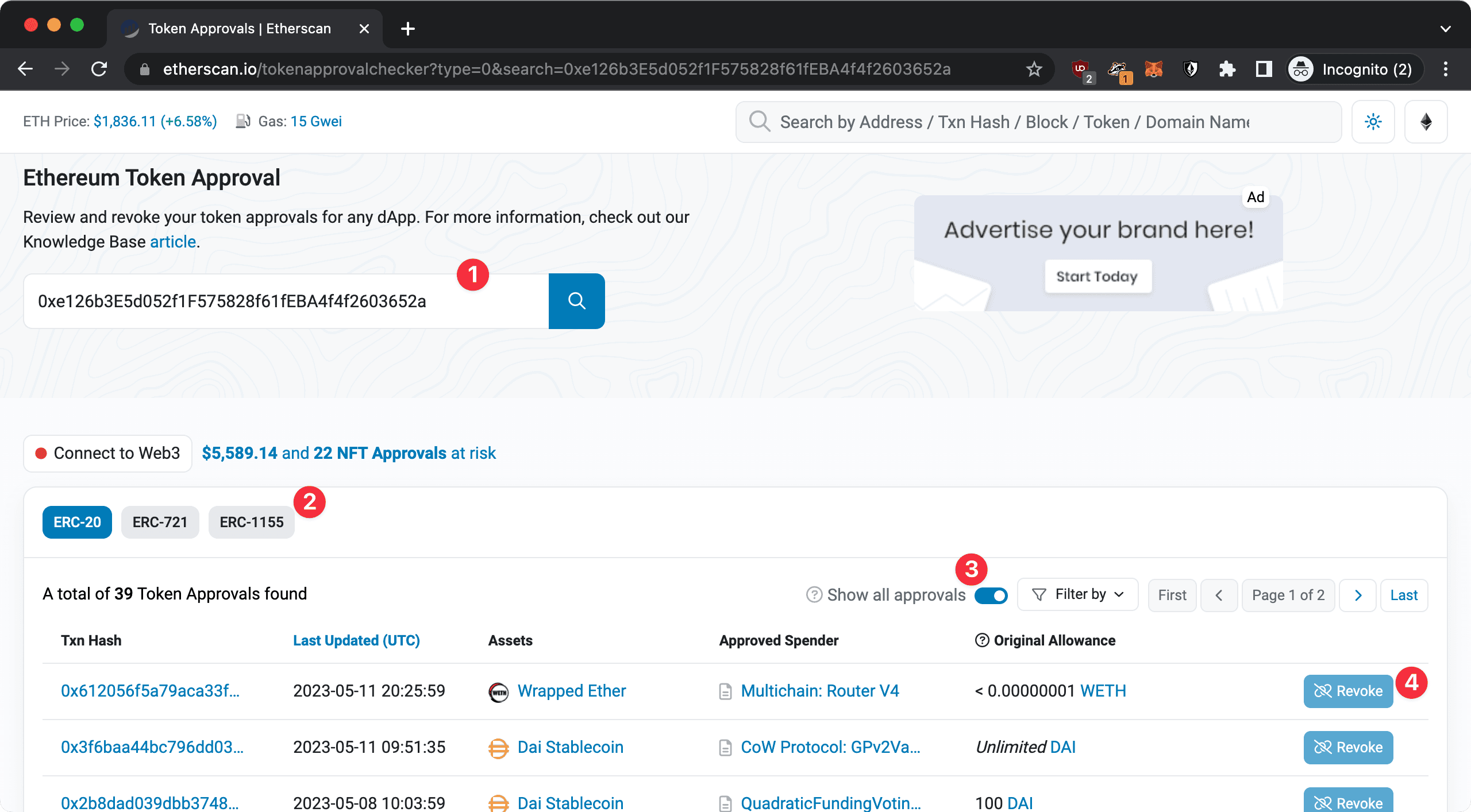
Protect Your Crypto Wallet from Drainer Attacks
If you own any crypto at all, learning to protect your crypto wallet is not…
Emerging Cyber Threats in 2026: AI, Deepfakes, and More
In today's world, where everything from our morning coffee maker to our work emails is…
The 3-2-1 Backup Rule: Protect Your Data from Ransomware
In this post we will explain The 3-2-1 Backup Rule. In today's digital world, losing…
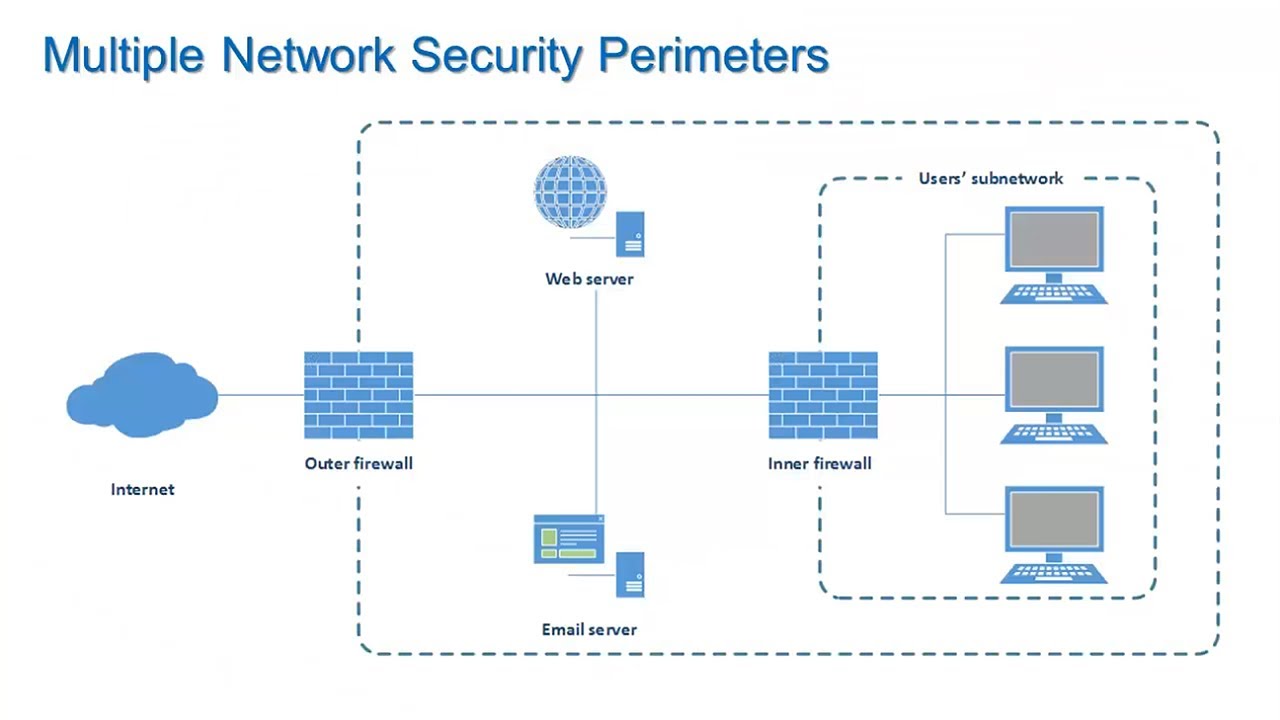
Ransomware Protection Strategies for Small Businesses
In this post, we're explain ransomware protection strategies that can help you safeguard your business…
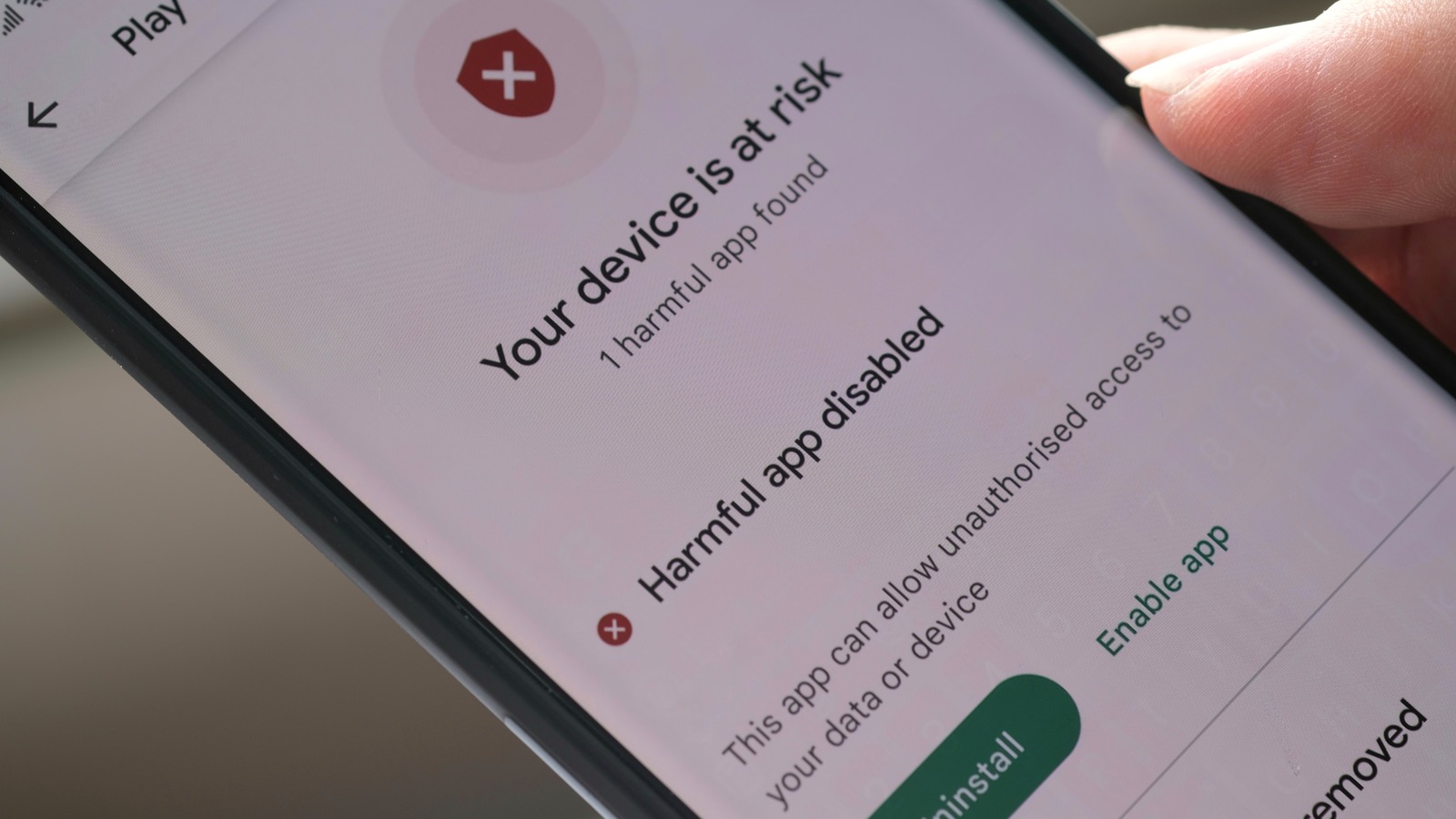
How to Spot and Remove Malware from Your Device
The good news? Most malware infections are preventable, and even when they happen, you can…
Phishing Emails – How to Spot and Avoid Them Effectively
In today’s world, phishing emails remain one of the most common and dangerous cyber threats.…
What Is Data Encryption and How to Start Using It Today
In today's digital world, protecting your information is more crucial than ever. Data encryption is…