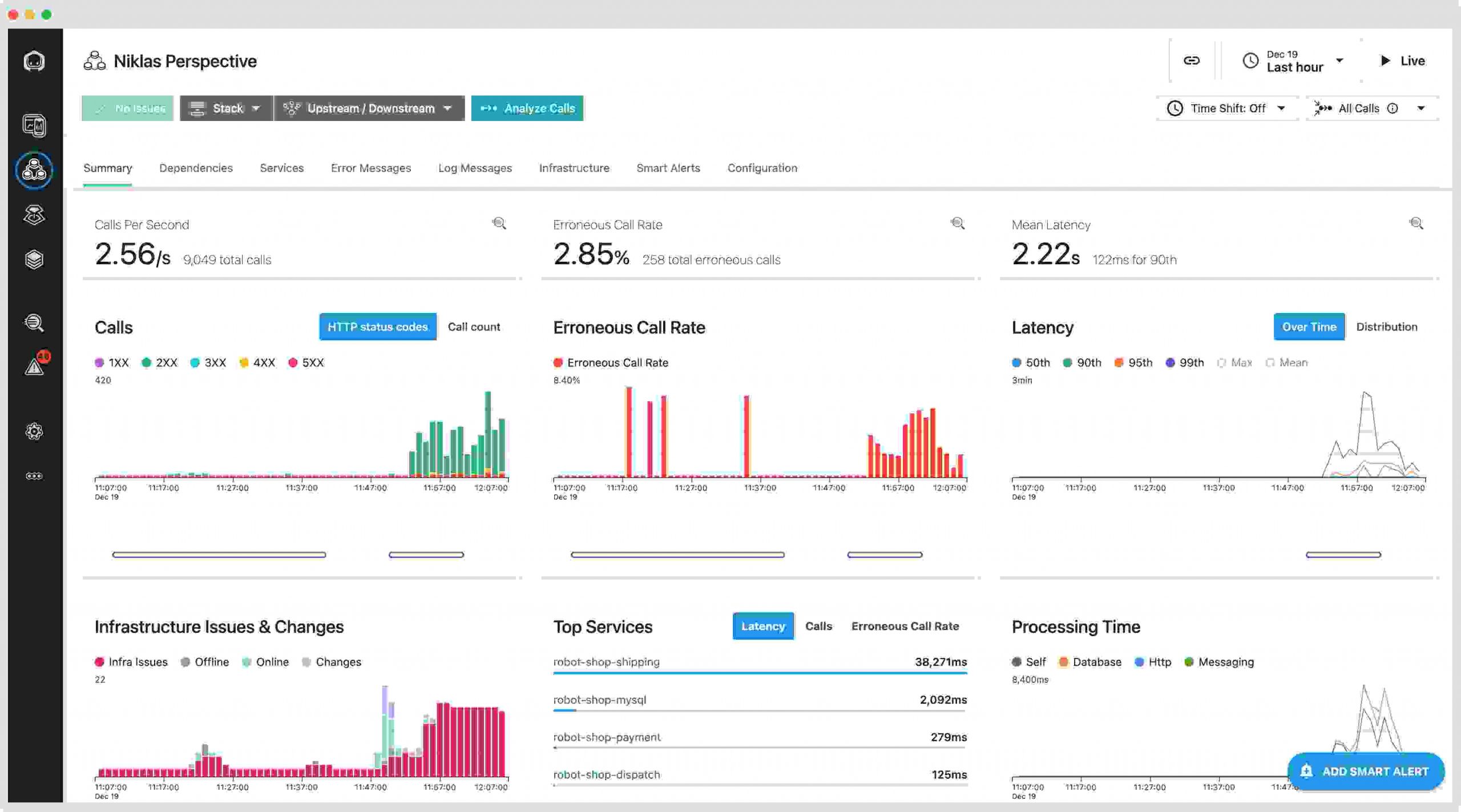
Continuous Monitoring Tools for Cloud Environments
Hey there! If you run apps or infrastructure in the cloud, you already know how…
Cybersecurity Career Guide 2026
The world runs on technology, and with every click, swipe, and online transaction, cyber threats…
Digital Trust Frameworks: Building Customer Confidence in 2026
Picture this: It's a busy Tuesday in 2026. You're shopping online for a new laptop,…
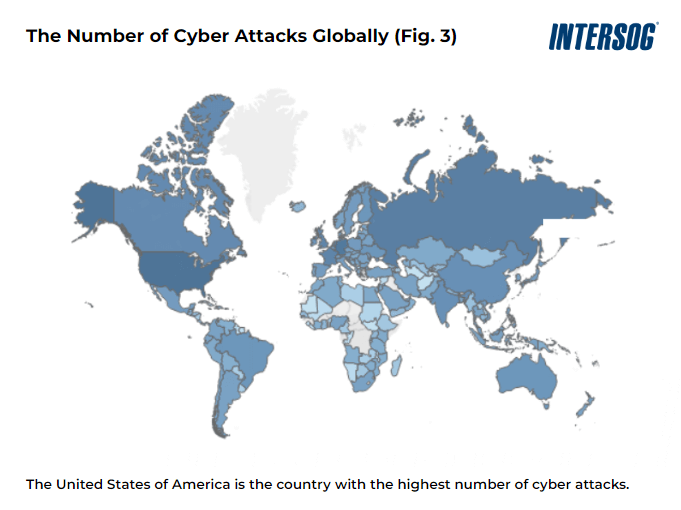
Nation-State Cyber Threats: Protection Strategies for 2026
In our hyper-connected world, nation-state cyber threats have become a daily reality that affects everyone—from…
Identity and Access Management for AI Agents
In today's fast-moving world, AI agents are changing how businesses work. These smart systems handle…
Top 10 AI Governance Best Practices for Businesses 2026
In 2026, artificial intelligence sits at the heart of how companies operate — from customer…
Quantum Computing Threats to Encryption
Imagine logging into your online banking app one morning only to find that every transaction…
Data Privacy Regulations 2026: Compliance Checklist
Hey there, business owner, marketer, or tech professional — if you're handling any kind of…
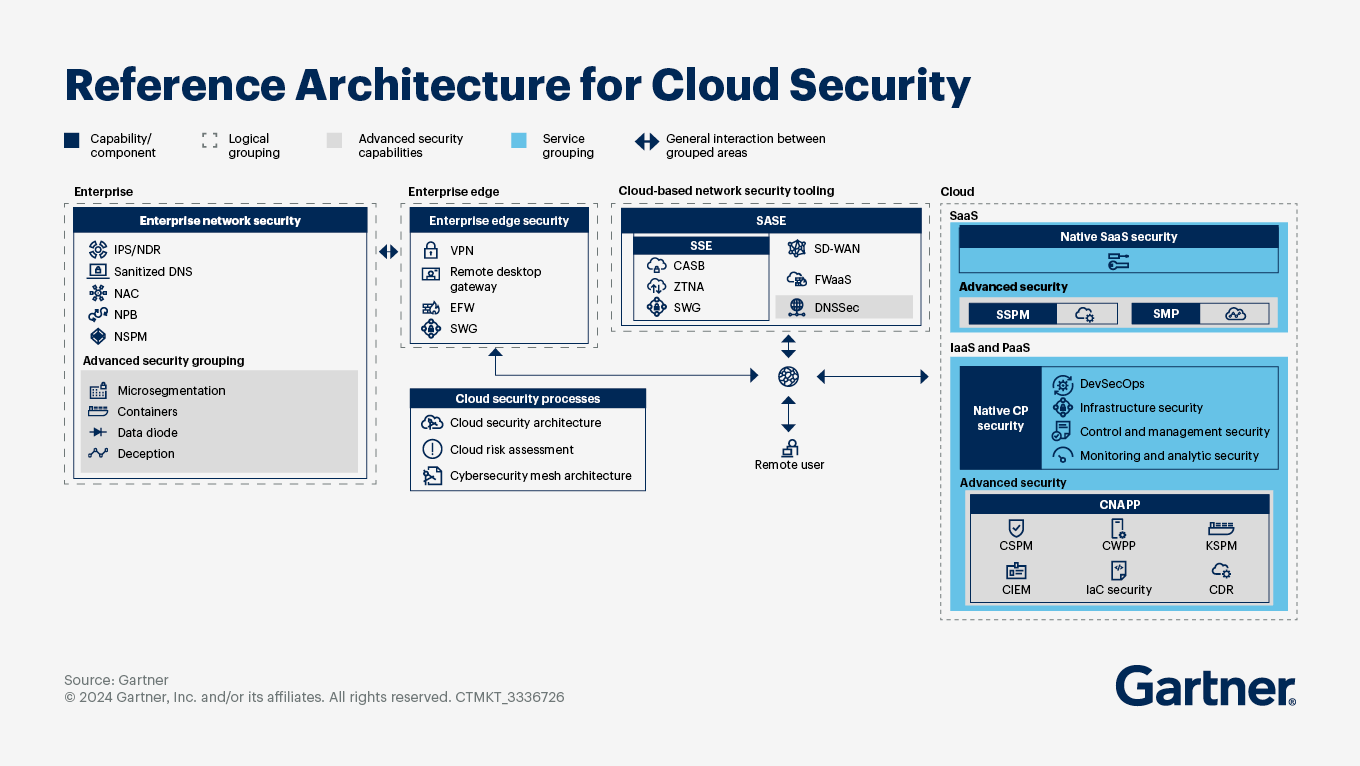
Cloud-Native Security Architectures
Cloud computing has changed how businesses build and run applications. But with great power comes…
Secure Your APIs Against Emerging Threats in 2026
If you want to secure your APIs against emerging threats, you need practical steps that…