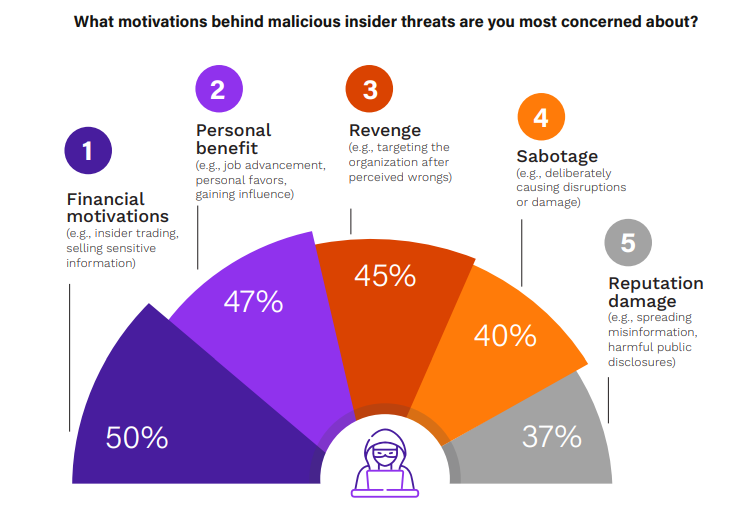
Threat Detection Using Behavioral AI
Insider threats cost organizations millions every year. In 2024 alone, 83% of companies faced at…
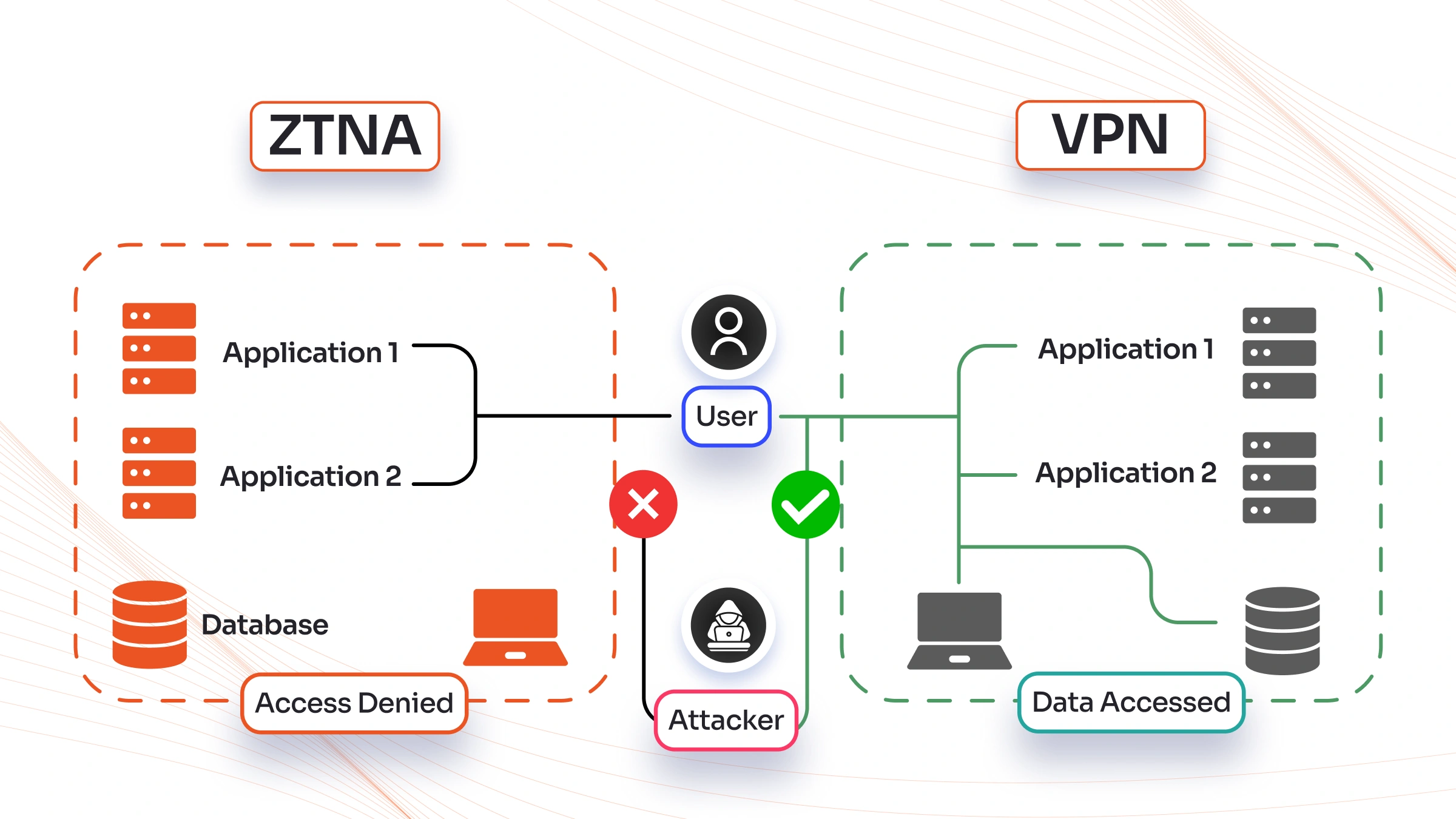
VPN vs ZTNA in 2026: Which One Should Your Business Use for Secure Remote Access?
If you run a business in 2026, chances are your team works from different places…
Privacy Enhancing Technologies (PETs)
In our connected world, every click, purchase, and health check generates personal data. Companies and…
How to Respond to a Cyber Incident in Under 60 Minutes
Cyber threats hit fast. One minute your systems run smooth, the next an alert pops…
Top 10 Open-Source Cybersecurity Tools
In today's world, keeping your data safe is more important than ever. Hackers are getting…
Securing Cryptocurrency Wallets Against AI Drainers
Imagine waking up to find your entire crypto portfolio wiped out overnight. No hack on…
Cybersecurity Awareness Training That Actually Works
In today's connected world, one wrong click can open the door to serious trouble. Hackers…
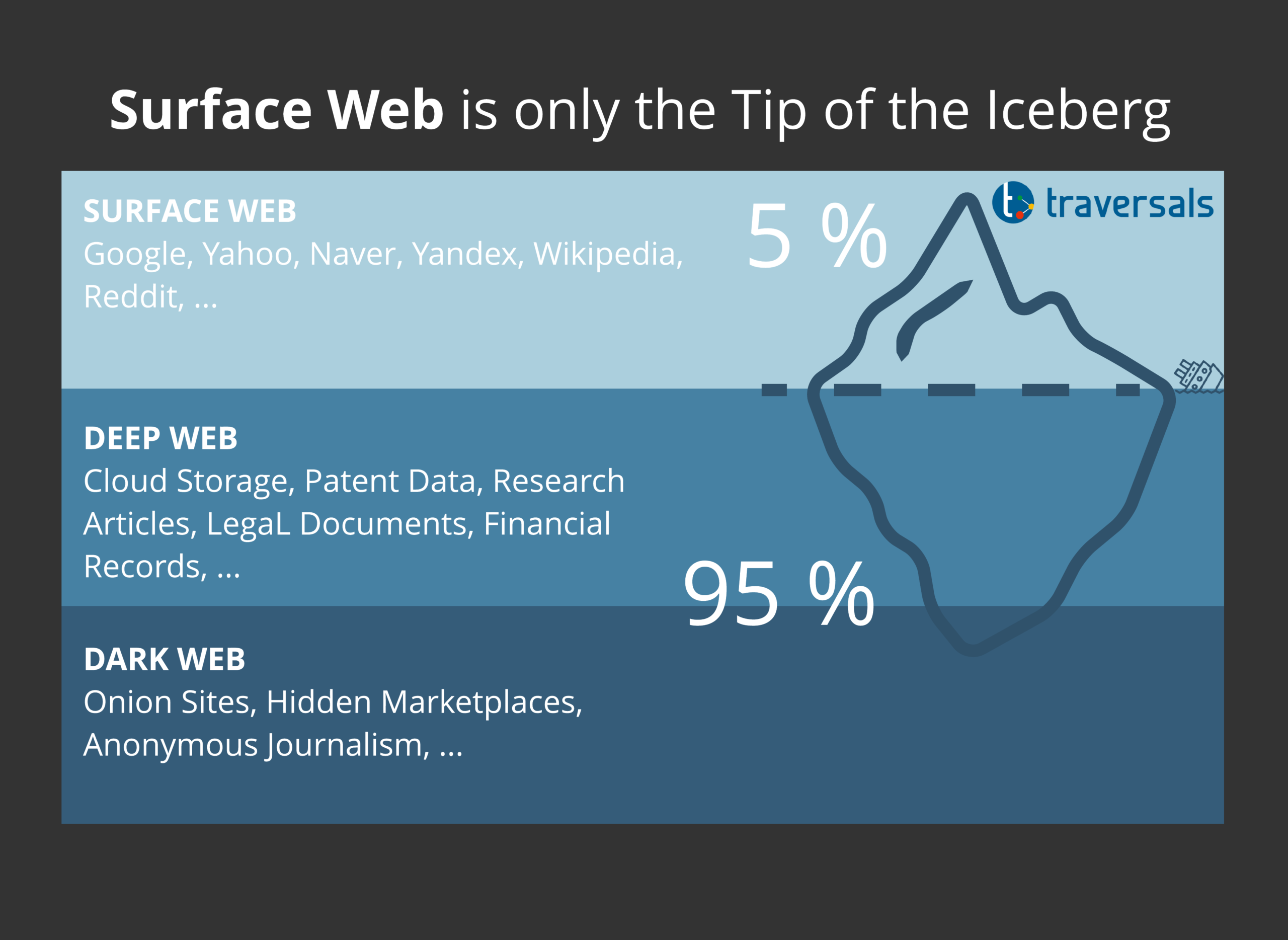
Dark Web Monitoring Services
Hey folks, in today's connected world, your personal information is everywhere. From your email and…
Secure Coding Practices to Block AI Generated Vulnerabilities
AI tools are everywhere in coding these days. Developers use them to write functions in…
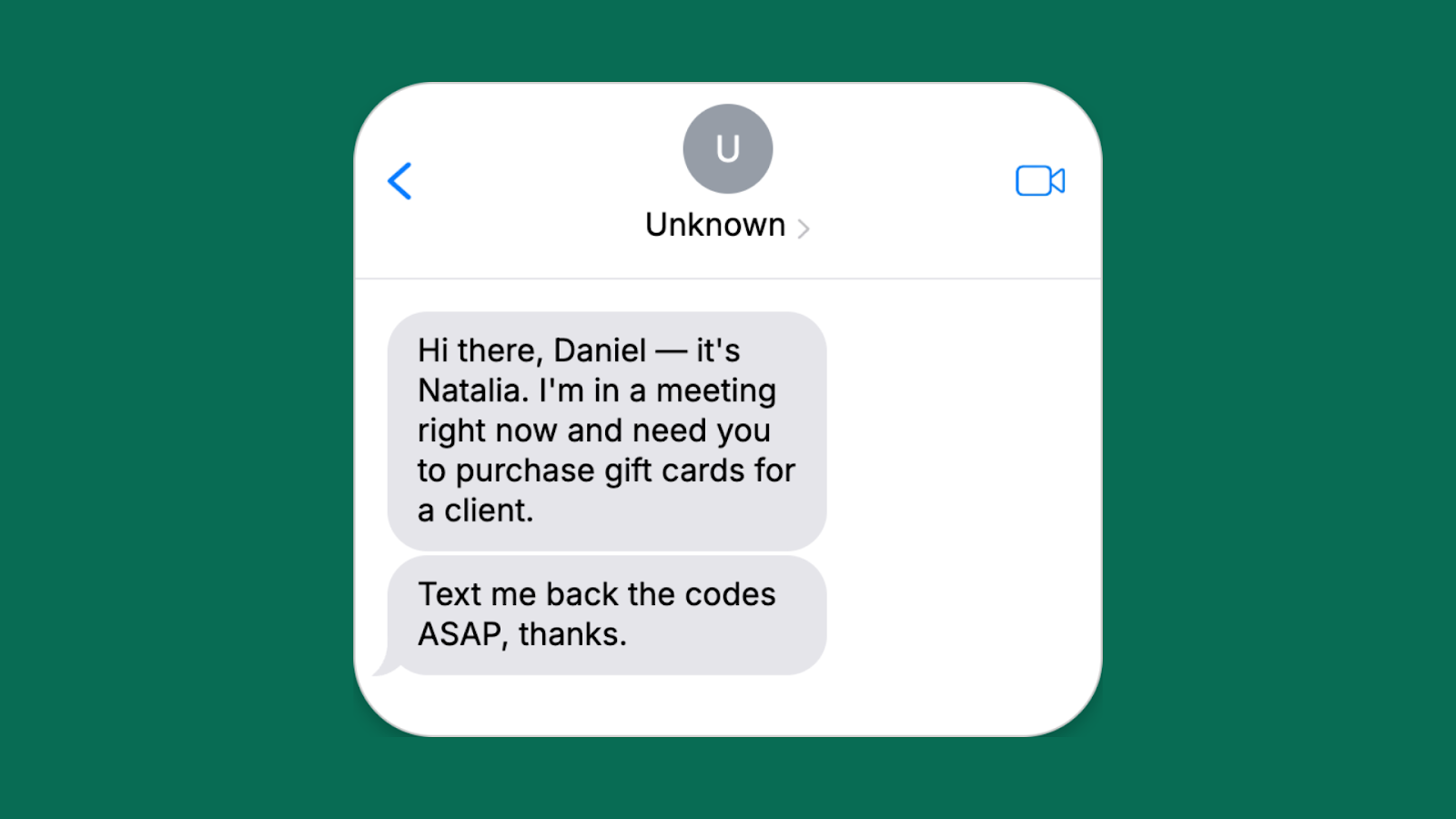
Smishing & Vishing Attacks
You’re sitting at home, phone in hand, when a text arrives: “Your Amazon package is…