Identity and Access Management for AI Agents
In today’s fast-moving world, AI agents are changing how businesses work. These smart systems handle tasks like analyzing data, talking to customers, booking appointments, or even managing supply chains—all without constant human input. But with great power comes great responsibility. One wrong move, and sensitive information could leak, systems could break, or compliance rules could get violated.
That’s where Identity and Access Management steps in. Identity and Access Management makes sure the right AI agents can reach the right resources at the right time—and nothing more. It handles who (or what) the agent is, what it can do, and keeps a close watch on every action.
If you’re building or using AI agents in your company, understanding Identity and Access Management isn’t optional anymore. It’s the foundation that keeps your AI safe, trustworthy, and ready for real-world use. In this complete guide, we’ll walk through everything step by step in simple terms. You’ll learn what Identity and Access Management really means for AI agents, why it matters so much, the main challenges, proven best practices, helpful tools, real examples, and what the future holds.
Whether you’re a developer, IT leader, or business owner, this post will give you clear, actionable insights to protect your AI investments.

Image credit: CyberArk blog on identity security – futuristic digital security scene showing AI elements with locks and access controls.
What Exactly Is Identity and Access Management?
Identity and Access Management (often shortened to IAM) is the set of processes, policies, and technologies that control digital identities and their permissions. Think of it as the security guard at the door of your company’s digital world.
At its core, Identity and Access Management answers three big questions:
- Who or what is trying to get in? (Authentication – proving identity)
- What should they be allowed to do? (Authorization – granting permissions)
- How do we keep track and make sure everything stays safe? (Auditing and governance)
For regular users like employees, Identity and Access Management might involve passwords, multi-factor authentication (MFA), single sign-on (SSO), and role-based access controls (RBAC). But AI agents are different. They aren’t humans sitting at a desk. They’re software that can act on their own, make decisions, and chain multiple steps together.
So, Identity and Access Management for AI agents treats these agents like special “machine identities” or “workload identities.” Each agent gets its own unique ID, just like a user account, but designed for non-stop, autonomous operation.
For example, an AI customer service agent might need to read order history from your database but should never be able to delete customer records or access payroll data. Identity and Access Management enforces that boundary automatically.
Traditional Identity and Access Management tools were built for humans and static apps. AI agents move fast, change behavior based on new information, and sometimes work across different systems or even spawn smaller helper agents. That’s why modern Identity and Access Management needs to be more dynamic, context-aware, and focused on machines.

Image credit: Akira AI – detailed flowchart showing AI agent authentication and authorization flow with ephemeral credentials and policy checks.
Understanding AI Agents and Why They Need Special Identity and Access Management
AI agents are autonomous programs powered by large language models (like GPT or Claude) combined with tools and memory. They don’t just answer questions—they plan, act, use APIs, learn from results, and keep going until the goal is complete.
There are different types:
- Simple agents: Follow fixed steps, like a chatbot that books meetings.
- Advanced agentic AI: Make decisions, call other tools, delegate to sub-agents, and operate for hours or days.
- Multi-agent systems: Teams of agents working together, like one researching, another writing, and a third reviewing.
These agents interact with emails, databases, CRMs, payment systems, and even external websites. Without strong Identity and Access Management, an agent could accidentally (or maliciously if compromised) access far more than it should.
Here’s why standard user-focused Identity and Access Management falls short:
- Agents work 24/7 without breaks.
- Their actions can be unpredictable because they adapt in real time.
- They often act “on behalf of” a human but need their own separate identity for accountability.
- They can spawn new agents, creating chains of permissions.
- One breach could let an attacker control thousands of automated tasks.
That’s why Identity and Access Management for AI agents borrows from machine identity practices (like workload identities in clouds) but adds extra layers for autonomy and risk.
A 2025 Cloud Security Alliance report found that many organizations are already deploying hundreds of AI agents but lack proper governance. Only about 18% feel highly confident their current Identity and Access Management systems can handle agent identities safely.
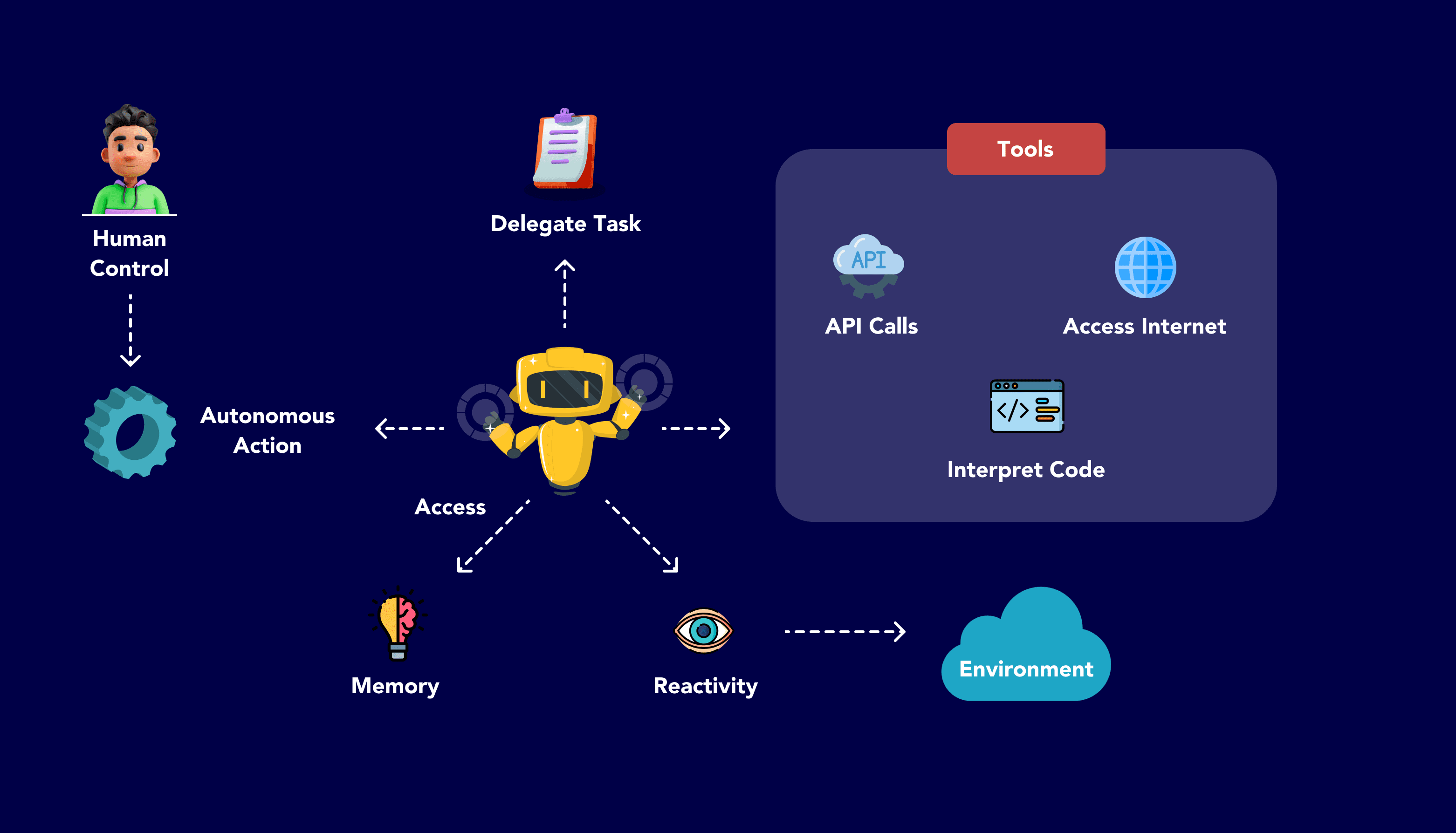
Image credit: Codoid – clear diagram explaining AI agent components including human control, autonomous action, tools, and environment access.
Why Identity and Access Management Is Critical for AI Agents
Let’s make this real. Suppose your sales team uses an AI agent to qualify leads from email and LinkedIn. The agent logs into your CRM, checks deal history, and suggests next steps. Without proper Identity and Access Management:
- It might use a shared admin account (huge risk if compromised).
- It could access every customer’s full financial data instead of just contact info.
- If the agent gets tricked by bad input, it might delete records or send unauthorized emails.
- Auditing who did what becomes impossible— was it the agent or a hacker?
Good Identity and Access Management prevents all that. It:
- Gives each agent a unique, verifiable identity tied to its owner or purpose.
- Applies the principle of least privilege (only the minimum access needed for the current task).
- Uses short-lived credentials that expire quickly.
- Logs every single action with clear “who, what, when, and why.”
- Allows human oversight for sensitive steps (human-in-the-loop).
- Supports quick revocation if something looks suspicious.
Benefits go beyond security:
- Compliance: Easier to meet GDPR, HIPAA, SOC 2, or ISO standards because access is documented and controlled.
- Efficiency: Agents run smoothly without constant manual approvals for routine tasks.
- Trust: Customers and partners feel safer knowing your AI systems are tightly governed.
- Scalability: As you add more agents, Identity and Access Management grows with them without chaos.
In short, strong Identity and Access Management turns AI agents from potential risks into reliable, auditable team members.
Key Components of Identity and Access Management for AI Agents
Effective Identity and Access Management for AI agents rests on several interconnected pieces. Let’s break them down simply.
1. Identity Provisioning and Lifecycle Management
Every AI agent needs its own identity from the start. This includes:
- Creating a dedicated machine identity (not sharing human accounts).
- Linking it to a human sponsor or business owner for accountability.
- Using standards like SCIM (System for Cross-domain Identity Management) to automate creation, updates, and removal.
- Just-in-time (JIT) provisioning for temporary agents that spin up for one task and disappear.
When the agent finishes its job or gets retired, Identity and Access Management must fully de-provision it—revoke all tokens, delete permissions, and archive logs.
2. Authentication for AI Agents
Authentication proves the agent is who it says it is. For agents, avoid simple passwords or long-lived API keys (too easy to steal).
Better options:
- Workload identities (like AWS IAM roles or Google Cloud workload identity federation).
- Mutual TLS certificates or JWT tokens with strong signing.
- OAuth 2.1 with PKCE for secure flows.
- For agents acting on behalf of users: On-Behalf-Of (OBO) flows or Client-Initiated Backchannel Authentication (CIBA) so the human approves asynchronously without giving away credentials.
Detection is key too—Identity and Access Management systems should spot when a session comes from an AI agent using behavioral signals.
3. Authorization and Access Control
This decides “what can the agent do?”
Modern approaches for AI agents:
- Role-Based Access Control (RBAC) as a starting point, but go further with Attribute-Based Access Control (ABAC) or Policy-Based Access Control (PBAC) that considers context like time, task goal, data sensitivity, and risk score.
- Fine-grained permissions down to specific API calls or database queries.
- Scope attenuation in delegation chains—if Agent A gives a task to Agent B, Agent B gets even narrower permissions.
- Dynamic policies that change in real time based on the agent’s behavior or external threat data.
Always follow least privilege: Give access only for the exact task and time needed.
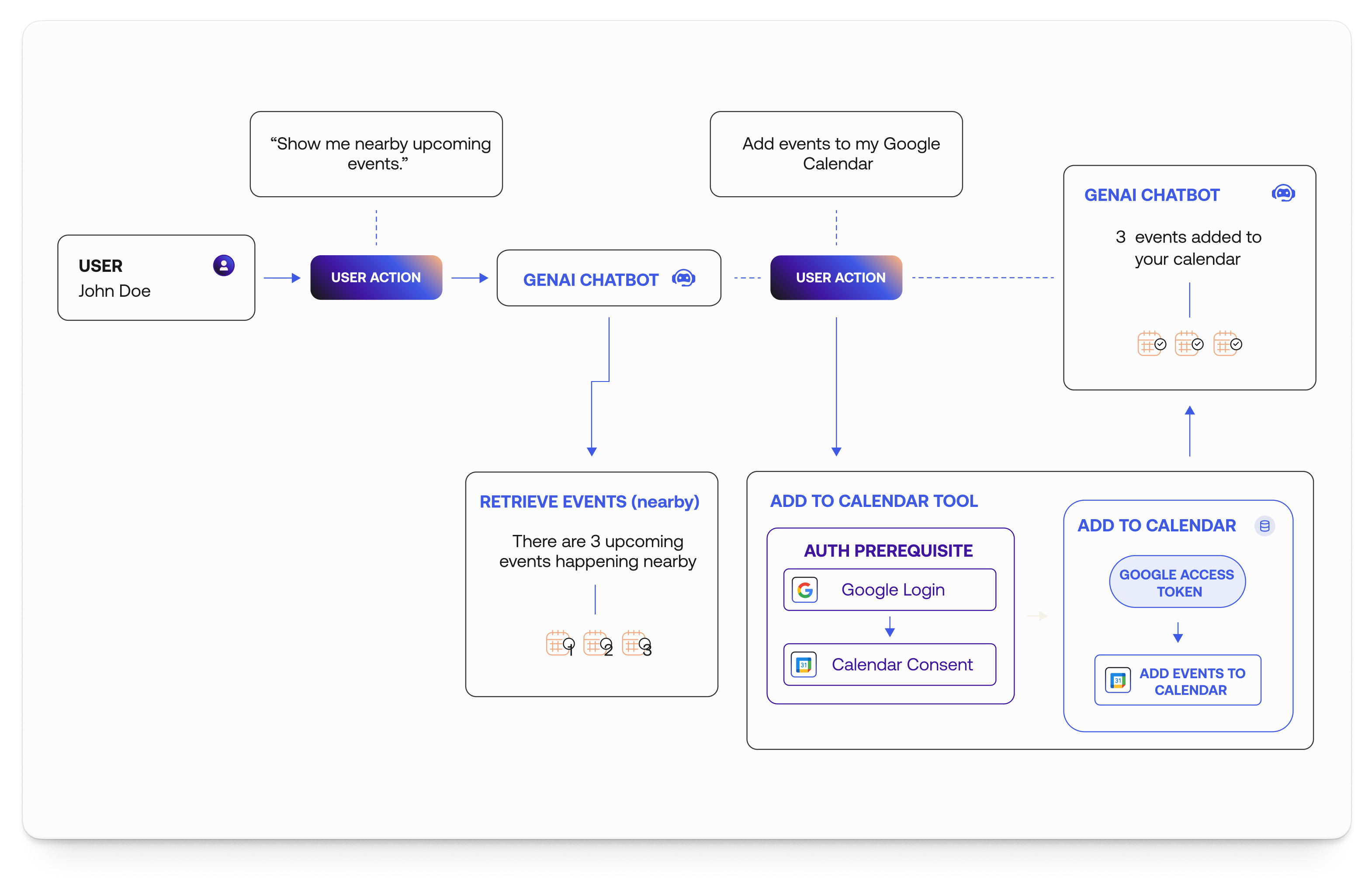
Image credit: Auth0 blog – practical example flowchart of user delegating to GenAI chatbot with proper authentication and consent steps.
4. Auditing, Monitoring, and Governance
Visibility is everything. Good Identity and Access Management logs:
- Every authentication attempt.
- Authorization decisions (why allowed or denied).
- Actual actions taken by the agent.
- Changes to the agent’s permissions or identity.
Tools use AI ironically to monitor other AI—spotting anomalies like an agent suddenly accessing unusual data or making too many requests.
Governance includes regular access reviews, automated alerts for over-privileged agents, and integration with broader security platforms.
5. Delegation and Human-in-the-Loop Controls
Agents often work for humans, so Identity and Access Management must support safe delegation:
- Never let agents impersonate users fully (creates audit gaps).
- Use explicit consent flows with clear scopes.
- For high-risk actions (money transfers, data deletion), require fresh human approval via push notification or out-of-band method.
- Support recursive delegation with clear chains so you always know the full path of authority.
These components work together to create a robust Identity and Access Management framework tailored for AI agents.
Common Challenges in Identity and Access Management for AI Agents
Implementing Identity and Access Management for AI agents isn’t always smooth. Here are the biggest hurdles organizations face:
- Dynamic and Unpredictable Behavior: Traditional rules assume fixed actions. AI agents adapt, so static policies break easily. One day the agent needs sales data; next day it might need marketing tools based on new insights.
- Scale and Speed: Hundreds or thousands of agents can appear quickly. Manual management becomes impossible. Lifecycle events (provision, update, revoke) must be automated but still secure.
- Delegation Complexity: Agents delegating to other agents creates long chains. Without proper scope narrowing, privileges can snowball dangerously.
- Consent Fatigue and Asynchronous Operations: Users can’t approve every micro-action. Agents working hours later need durable but revocable authority without constant pings.
- Discovery and Visibility Gaps: Many teams don’t even know all the AI agents running in their environment (shadow AI agents built by developers).
- Integration Across Systems: Agents cross cloud providers, on-prem systems, and third-party APIs. Identity and Access Management must federate trust without weakening security.
- Compliance and Accountability: Regulators want clear trails showing who authorized what. Mixing human and agent actions can blur lines.
- Performance Overhead: Adding heavy Identity and Access Management checks shouldn’t slow down fast AI workflows.
Real surveys from 2025-2026 show over 60% of organizations struggle with over-privileged agents and weak discovery. Addressing these early saves headaches later.
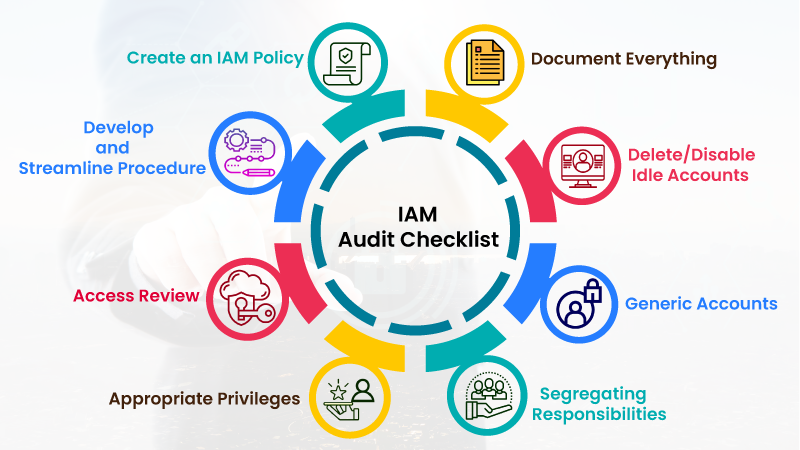
Image credit: Veritis – colorful IAM audit checklist infographic highlighting key governance steps.
Best Practices for Implementing Identity and Access Management for AI Agents
Here’s a practical, battle-tested playbook drawn from industry leaders like OpenID Foundation, Ping Identity, Curity, and cloud providers. Follow these to build strong Identity and Access Management.
- Treat Agents as First-Class Identities Give every agent its own dedicated identity tied to a verified owner. Use workload identity federation where possible. Avoid shared accounts or human impersonation.
- Apply Least Privilege Everywhere Start with zero access and grant only what’s needed for the specific task. Use short-lived tokens (minutes, not days). Review and tighten permissions regularly.
- Use Standard Protocols, Don’t Reinvent Stick to OAuth 2.1, OpenID Connect, SCIM for provisioning, and emerging standards like Model Context Protocol (MCP) for tool connections. This ensures interoperability and security updates.
- Enable Secure Delegation, Not Impersonation Always use OBO flows so tokens clearly show both the human principal and the acting agent. This keeps audit trails clean.
- Add Human Oversight for Sensitive Actions Build in human-in-the-loop checks using CIBA or out-of-band approvals. For very high-risk tasks, require multi-person approval or biometric-style verification that’s hard for AI to fake.
- Implement Continuous Monitoring and Anomaly Detection Log everything. Use behavioral analytics to flag unusual agent patterns—like accessing new data types or running at odd hours. Automate revocation on suspicion.
- Automate Lifecycle Management Use policy-as-code to define agent creation, updates, and de-provisioning. Integrate with your CI/CD pipelines so new agents get proper Identity and Access Management from day one.
- Design for Context-Aware and Dynamic Policies Policies should consider who the agent belongs to, what task it’s doing, current risk level, data sensitivity, and even the agent’s past behavior.
- Separate Authentication from Authorization Use Policy Enforcement Points (PEP) and Policy Decision Points (PDP) so decisions can adapt without changing core code.
- Plan for Recursive Delegation and Multi-Agent Teams Build in scope attenuation and chain tracking so nested agents never inherit too much power.
- Regular Audits and Access Reviews Schedule quarterly reviews where human sponsors certify that their agents still need their current permissions.
- Educate Your Team Developers, security teams, and business users all need to understand agent Identity and Access Management basics. Make it part of your AI governance policy.
Following these practices turns Identity and Access Management from a checkbox into a competitive advantage.
Internal link: Learn how to combine this with Zero Trust principles in our guide to modern cloud security.
Step-by-Step Guide to Roll Out Identity and Access Management for Your AI Agents
Ready to get started? Here’s a phased approach:
Phase 1: Discovery (1-2 weeks) Inventory all existing AI agents. Map what data and systems each touches. Identify owners.
Phase 2: Foundation (2-4 weeks) Set up central Identity and Access Management platform supporting machine identities. Configure workload identity federation with your clouds.
Phase 3: Pilot (4 weeks) Pick 2-3 low-risk agents. Implement full Identity and Access Management—provisioning, authentication, authorization, logging. Test delegation and revocation.
Phase 4: Scale and Automate Roll out to all agents. Add policy-as-code, monitoring integrations, and automated reviews.
Phase 5: Optimize and Govern Run regular audits, gather feedback, refine policies, and stay updated on new standards.
Start small, measure results (like reduced over-privileged access or faster incident response), then expand.
Popular Tools and Technologies for Identity and Access Management in AI
Many mature solutions now support AI agents well:
- Cloud-Native: AWS IAM with workload identities and IAM Policy Autopilot for AI-assisted policy creation. Google Cloud IAM for fine-grained control and Vertex AI integration. Azure AD with managed identities.
- Specialized IAM Platforms: Okta (strong AI agent identity features), Ping Identity (excellent best practices for delegation), Auth0 (user-friendly for developers building agent tools).
- Enterprise Governance: Sailpoint, Saviynt, or ConductorOne for identity security posture management tailored to agents.
- Open Standards Tools: Keycloak for self-hosted OAuth/OpenID, SPIFFE/SPIRE for workload identities.
- Emerging AI-Specific: Solutions focusing on MCP servers, dynamic policy engines, and agent-specific governance from vendors like Curity or Strata.
Choose based on your stack—many offer free tiers or trials to test agent scenarios.
External resource: Explore AWS IAM best practices for AI workloads
External resource: Read the full OpenID Foundation whitepaper on Identity Management for Agentic AI
Real-World Examples of Identity and Access Management for AI Agents
Company A, a fintech firm, used Identity and Access Management with OBO delegation and CIBA approvals. Their AI fraud-detection agent now reviews transactions on behalf of analysts but requires human sign-off for blocks over $10,000. Result: 40% faster processing with zero unauthorized access incidents.
Company B, an e-commerce giant, implemented workload identities and continuous monitoring. When one marketing agent started querying unusual customer segments, the system auto-revoked access and alerted the team—preventing a potential data leak.
These stories show Identity and Access Management in action delivers both security and business speed.
Future Trends in Identity and Access Management for AI Agents
Looking ahead to 2026 and beyond:
- Agentic IAM as a new category—fully autonomous governance where AI helps manage other AI identities.
- Wider adoption of verifiable credentials and decentralized identities for cross-organization agent trust.
- Quantum-resistant cryptography baked into agent tokens.
- Built-in privacy controls so agents handle personal data without exposing it.
- Seamless integration with physical systems (robots, IoT) under unified Identity and Access Management.
- Regulatory frameworks specifically for agent identities, similar to today’s data protection laws.
Organizations that invest in forward-looking Identity and Access Management today will lead the AI wave safely.

Image credit: Harvard Extension School – professionals collaborating on AI and cybersecurity strategies in a modern office.
Conclusion
Identity and Access Management for AI agents isn’t just another security checkbox—it’s the enabler that lets you unlock the full power of autonomous AI without fear. By giving agents proper identities, tight controls, clear audit trails, and smart delegation, you create systems that are secure, compliant, and truly helpful.
Start today: Inventory your agents, pick one to secure properly, and build from there. The investment in solid Identity and Access Management will pay off many times over in risk reduction and operational confidence.
Your AI agents are ready to work hard. Make sure Identity and Access Management is there to keep them safe.
Internal link: Ready to build your first secure AI agent? Check our beginner’s guide here.
What are your biggest concerns with AI agent security? Drop a comment below—I’d love to hear and help.
Frequently Asked Questions About Identity and Access Management for AI Agents
What is the main difference between regular IAM and IAM for AI agents? Regular IAM focuses on human users with predictable behavior. IAM for AI agents handles autonomous, dynamic machine entities that need ephemeral credentials, context-aware policies, and strong delegation support.
Do AI agents need their own separate identities? Yes, absolutely. Treating them as first-class machine identities improves accountability, simplifies auditing, and reduces risks compared to sharing human credentials.
How does least privilege work with unpredictable AI agents? Use just-in-time access, short-lived tokens, and dynamic policies that evaluate the current task context. Start narrow and expand only when the agent proves the need through approved workflows.
Can small businesses implement Identity and Access Management for AI agents? Yes! Start with cloud-native tools like AWS IAM or free tiers of Okta/Auth0. Focus on basics—unique agent identities, least privilege, and logging—then scale up.
What standards should I follow for IAM in AI? Key ones include OAuth 2.1, SCIM, OpenID Connect, and emerging guidance from OpenID Foundation and CSA on agentic AI. Cloud providers also publish excellent reference architectures.
How do I handle agents that work across multiple companies? Use identity federation, verifiable credentials, and cross-domain trust models. Start with clear contracts and audited delegation flows.
Is human-in-the-loop always required? Not for every action, but for sensitive or high-risk ones, yes. Modern IAM supports asynchronous approvals so agents don’t get blocked unnecessarily.
What happens if an AI agent’s credentials get compromised? Strong IAM makes recovery fast—revoke the specific identity instantly, review logs for impact, rotate related secrets, and re-provision a clean agent.
How does Identity and Access Management help with compliance? It creates clear, tamper-proof audit trails showing exactly which agent did what, when, and under whose authority. This simplifies audits for GDPR, SOC 2, and more.
Where can I learn more about advanced IAM for AI? Check resources from Ping Identity, Okta’s AI identity guides, the OpenID whitepaper, and your cloud provider’s security blogs.
Share this content:














Post Comment