How to Build Cyber Resilience Against AI-Powered Attacks
Businesses everywhere are scrambling to protect themselves. That’s where cyber resilience against AI-powered attacks comes in. It’s not just about blocking threats—it’s about preparing your organization to absorb hits, keep running, and bounce back stronger.
Imagine waking up to find your company’s systems locked by ransomware that changed its code every few seconds, or getting a video call from what looks exactly like your CEO asking for an urgent $25 million wire transfer. These aren’t sci-fi scenarios anymore. In 2025 and early 2026, AI-powered attacks have become real, fast, and incredibly hard to spot.
You’ll learn what these new attacks look like, why old-school security isn’t enough anymore, and exactly how to build strong cyber resilience against AI-powered attacks step by step. Whether you run a small business in Jamshedpur or manage IT for a larger company, these practical tips will help you stay safer in 2026 and beyond.

Image credit: Dreamstime (Futuristic shield protecting network symbolizing cybersecurity)
What Exactly Are AI-Powered Attacks?
AI-powered attacks use artificial intelligence to make hacking faster, smarter, and more convincing than anything humans could do alone. Traditional hackers might send the same spam email to thousands of people and hope a few click. AI does something much scarier.
It studies your LinkedIn profile, your recent emails, even the way you write, then creates a message that feels completely personal. In tests, AI-generated phishing emails got clicked 54% of the time—more than four times better than regular ones.
Here are the main types you need to know:
- Deepfake scams: Attackers create fake videos or voice recordings. In one 2024 Hong Kong case, criminals used deepfake video of an entire team in a fake conference call and tricked a finance worker into sending $25.6 million. A similar Arup deepfake fraud in early 2026 reportedly cost another company $25 million.
- Smart phishing and vishing: AI writes perfect emails or makes phone calls with cloned voices. Tools can generate thousands of unique versions that dodge spam filters.
- Polymorphic malware: This malware uses AI to rewrite its own code constantly. BlackMamba and PromptLock are early examples—new strains appear that antivirus software has never seen before.
- Autonomous AI agents: These are like robot hackers that plan entire attacks on their own—scanning for weaknesses, writing exploits, moving through networks, and stealing data without a human touching the keyboard.
- Adversarial attacks on AI systems: Hackers trick company AI tools (like chatbots or hiring software) into giving away secrets or behaving badly.
CrowdStrike’s 2026 Global Threat Report showed an 89% jump in these AI-enabled attacks in just one year. IBM and other researchers saw phishing linked to generative AI surge by over 1,200%. The numbers are climbing fast, and small businesses are often the easiest targets because they think “it won’t happen to us.”
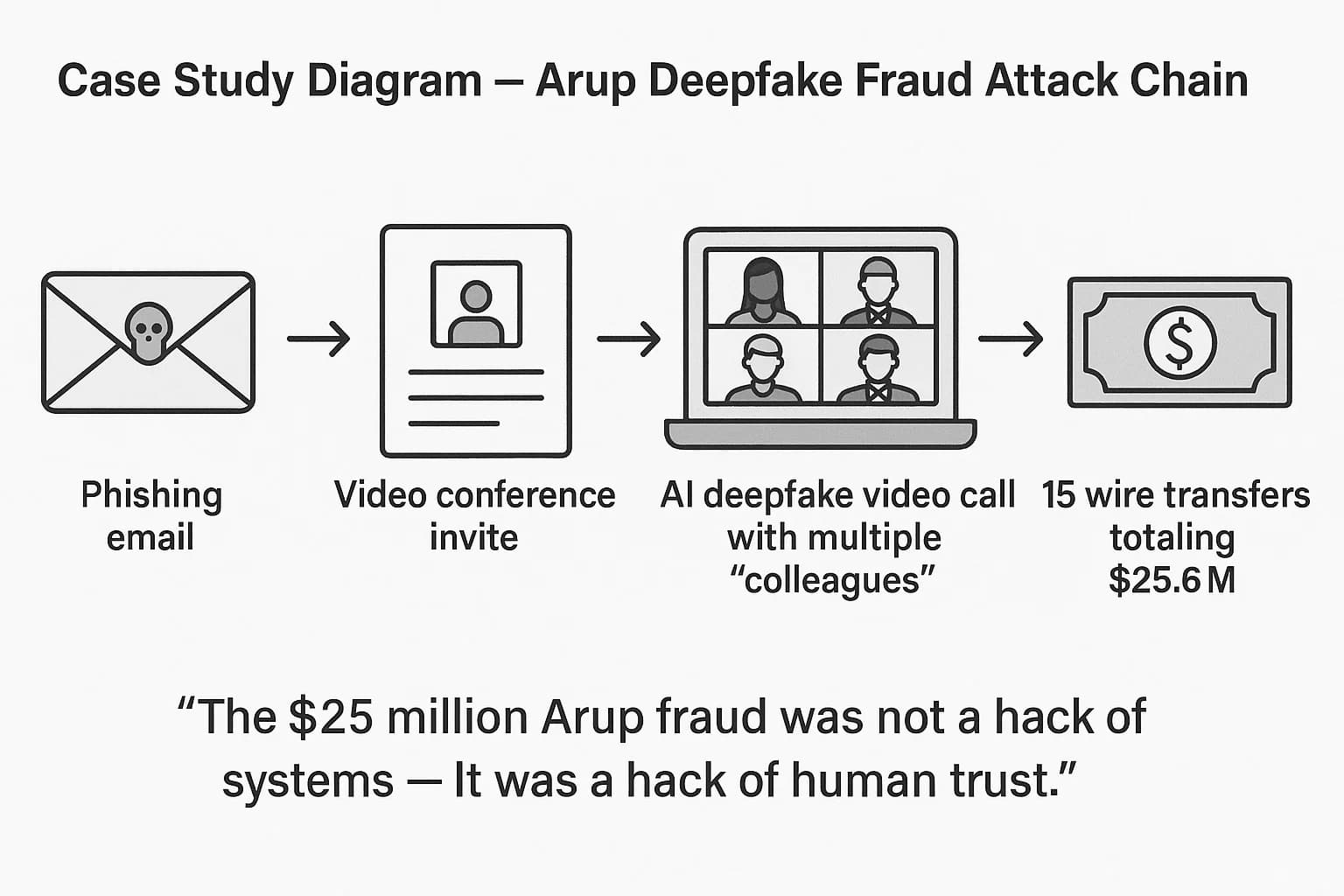
Image credit: Deepstrike.io (Case study diagram of Arup deepfake fraud attack chain)
Why Old Cybersecurity Methods No Longer Work
Think of traditional security like a strong castle wall with guards at the gate. It worked great when attackers used ladders and ropes. But now the enemy has drones, invisibility cloaks, and robots that tunnel under the wall in seconds.
Signature-based antivirus looks for known bad files. AI malware creates new files every time, so there’s no signature to match.
Rule-based firewalls block certain patterns. AI attacks blend perfectly with normal traffic.
Even human teams can’t keep up. One AI agent can make thousands of requests per second—faster than any person could ever respond.
That’s why we need cyber resilience against AI-powered attacks. Resilience means the system doesn’t just try to stop every single attack (impossible now). It assumes some attacks will get through and focuses on limiting damage and recovering quickly.
What Cyber Resilience Really Means Today
Cyber resilience is the ability of your people, processes, and technology to prepare for, withstand, recover from, and adapt to cyber threats—especially the AI-powered ones.
It has four simple pillars:
- Prepare – Know your risks and train everyone.
- Withstand – Make it hard for attackers to move around or do big damage.
- Recover – Get back to normal fast with good backups and plans.
- Adapt – Learn from every incident and get stronger.
NIST and CISA both updated their frameworks in 2025 to include AI-specific guidance. The NIST Cybersecurity Framework Profile for Artificial Intelligence and the AI Risk Management Framework are free resources worth reading.

Image credit: National Cybersecurity Alliance (Employees in a cybersecurity training workshop)
Step 1: Start with a Honest Risk Assessment
You can’t protect what you don’t know. Begin by mapping everything.
- List all your devices, cloud accounts, AI tools, and third-party services.
- Ask: Where is our sensitive data? Who can access it? What AI systems do we use (even simple chatbots count)?
- Look for weak spots like old software, shared passwords, or employees working from home on personal laptops.
Use free tools from CISA or simple spreadsheets at first. For bigger companies, consider frameworks like NIST SP 800-53 or the Cyber Resilience Review.
Do this assessment every six months because new AI tools and threats appear constantly.
Pro tip: Involve people from every department. The marketing team might be using an AI content tool you didn’t know about that connects to your customer database.
Read our earlier post on basic asset inventory for small businesses
Step 2: Train Your People to Spot AI Tricks
Your employees are the first and last line of defense. Regular “click here” training isn’t enough anymore.
Modern training should cover:
- How to spot deepfake videos (look for unnatural blinking, lighting mismatches, or audio that doesn’t match lip movements).
- Never trust urgent requests for money or data without verifying through another channel (call the person on a known number).
- Recognizing AI-written emails that sound too perfect or use unusual phrasing.
- Safe use of AI tools inside the company (don’t paste sensitive data into public ChatGPT, for example).
Run simulated attacks monthly using AI-generated phishing and deepfake videos. Tools like Keepnet or custom setups work well. Celebrate people who report suspicious stuff instead of punishing mistakes.
One company I know reduced successful phishing by 70% after they started showing real deepfake examples in training sessions.
External resource: CISA’s free cybersecurity training materials – https://www.cisa.gov/topics/cybersecurity-best-practices
Step 3: Switch to Zero Trust – Never Trust, Always Verify
Zero Trust is one of the best ways to build cyber resilience against AI-powered attacks. The idea is simple: trust no one and nothing by default.
Every user, device, and application must prove who they are every single time they want access. Even if someone is already inside your network, they can’t roam freely.
How to start:
- Use multi-factor authentication everywhere (and make it phishing-resistant, like hardware keys).
- Segment your network so finance systems don’t talk directly to marketing tools.
- Monitor every login and data access in real time.
- Apply least-privilege rules—people only get access to what they need for their job.
Many organizations saw huge improvements after moving to Zero Trust. Microsoft, Google, and others publish free guides.
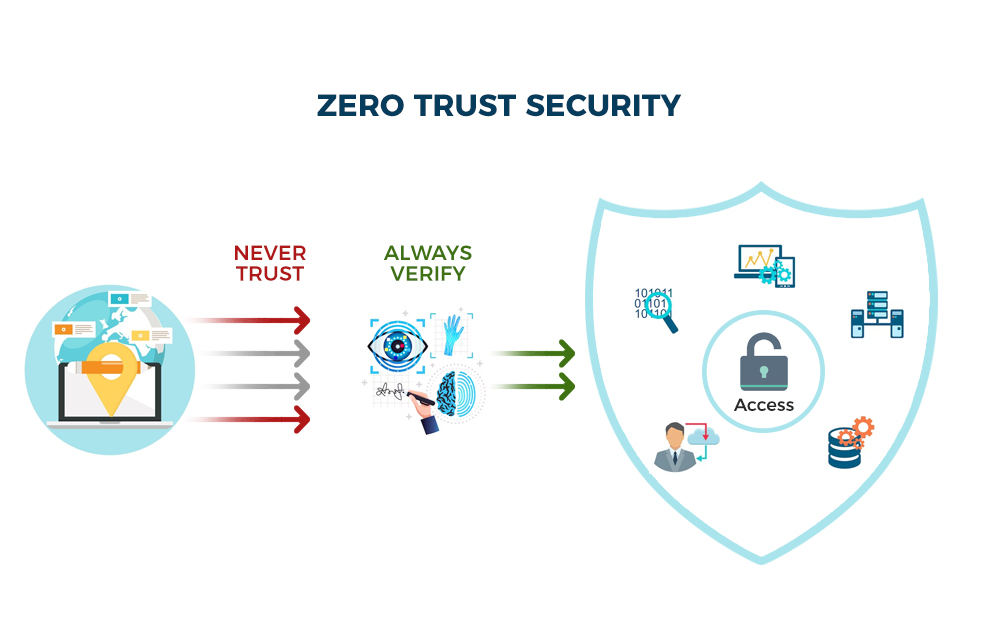
Image credit: Brickwork India (Zero Trust security architecture diagram)
Check our detailed Zero Trust implementation guide for Indian businesses
Step 4: Use AI to Fight AI
Yes, you read that right. The same technology attackers use can defend you.
AI-powered security tools can:
- Spot unusual behavior faster than humans (someone downloading 10 GB at 2 a.m. when they never do that).
- Analyze millions of emails and flag the sneaky ones.
- Automatically isolate infected devices before the malware spreads.
- Predict attacks by studying patterns across thousands of companies.
Examples of tools that do this well include Darktrace (which stopped a ransomware attack in a healthcare client before files were encrypted), CrowdStrike Falcon, and Microsoft Defender with AI features.
You don’t need to be a big corporation. Many affordable options now exist for small and medium businesses in India.
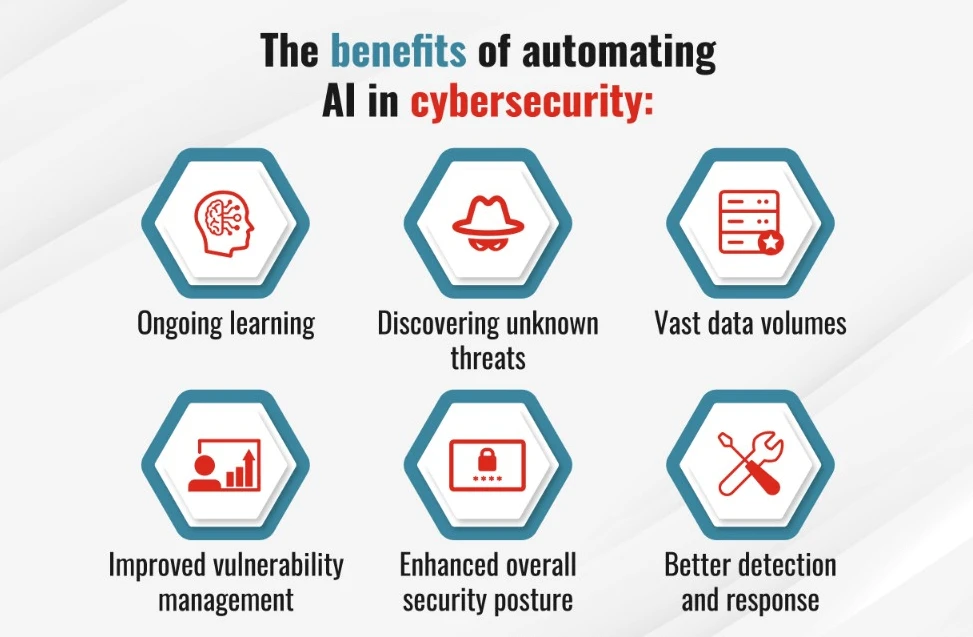
Image credit: Fortinet (Benefits of AI in cybersecurity infographic)
Step 5: Build a Strong Security Operations Center (Even a Small One)
A SOC is your 24/7 monitoring team or service. With AI, it becomes much more powerful.
Modern SOCs use XDR (extended detection and response) that pulls data from endpoints, email, cloud, and networks and lets AI connect the dots.
If you can’t afford a full in-house team, managed detection and response (MDR) services are a smart choice for many Indian companies.

Image credit: Dreamstime (Cybersecurity team in a modern SOC)
Step 6: Create Bulletproof Backup and Recovery Plans
Assume the worst will happen. Good backups are your insurance policy.
Follow the 3-2-1 rule: 3 copies of data, on 2 different types of media, with 1 copy offsite or in the cloud and air-gapped (not always connected).
Test restores every quarter. Make sure your backups themselves aren’t infected.
For AI-powered ransomware that tries to delete or encrypt backups, immutable storage (write-once, read-many) is essential. Many cloud providers now offer this.
Real Stories: What Worked and What Didn’t
Attack example: In 2025, a manufacturing firm lost millions when AI-generated polymorphic ransomware spread through their network in under 20 minutes. Traditional antivirus missed it completely.
Success story: A bank using Darktrace’s AI system detected unusual lateral movement caused by an autonomous agent and stopped it before any data left the building.
Deepfake win: One company trained staff to always verify video calls with a pre-agreed secret question. When a deepfake CEO appeared, the employee asked the question, the deepfake failed, and the scam was stopped.
These stories show that cyber resilience against AI-powered attacks is possible when preparation meets the right technology.
Image credit: ESET (Illustration of AI-written ransomware threat)
Tools and Resources Worth Checking
- NIST AI Risk Management Framework: https://www.nist.gov/itl/ai-risk-management-framework
- CISA Cybersecurity Best Practices: https://www.cisa.gov/topics/cybersecurity-best-practices
- CrowdStrike 2026 Global Threat Report (free summary available on their site)
- MITRE ATLAS matrix for AI-specific threats
- Free training from StaySafeOnline.org
For Indian businesses, also check MeitY and CERT-In guidelines—they released updated AI security advisories in late 2025.
Mistakes That Can Undo All Your Hard Work
- Thinking “we’re too small to be targeted” – AI attacks are cheap and automated now.
- Using the same password everywhere.
- Ignoring third-party risks (your vendor’s breach can become yours).
- Only updating software when something breaks.
- Treating security as an IT problem instead of a whole-company responsibility.
Avoid these and you’re already ahead of most organizations.
What the Future Holds – And How to Stay Ready
By 2027, experts predict agentic AI (systems that act completely on their own) will be common in both attacks and defense. Quantum computing may break current encryption, so post-quantum cryptography is already being tested.
Stay resilient by:
- Keeping systems updated.
- Reviewing your security every quarter.
- Building relationships with local cybersecurity communities in India.
- Budgeting for ongoing training and tools.
Image credit: Researchwire (Quantum computing and AI future trends illustration)
Final Thoughts
Building cyber resilience against AI-powered attacks isn’t about buying one magic tool or following a checklist once. It’s a continuous process of learning, adapting, and working together.
Start small. Pick one area this week—maybe updating your training or mapping your data flows. Every step makes you harder to attack and faster to recover.
Your business, your customers, and your peace of mind are worth it. The threats are real, but so are the solutions. Organizations that act now will thrive while others struggle.
If you found this helpful, share it with your team. And feel free to reach out in the comments—I read every one and love discussing real-world challenges Indian businesses face with AI threats.
Stay safe out there.
Share this content:














Post Comment