Cloud-Native Security Architectures
Cloud computing has changed how businesses build and run applications. But with great power comes greater responsibility—especially when it comes to keeping everything safe. That’s where Cloud-Native Security Architectures step in. These aren’t just add-on protections; they’re security built right into the DNA of your apps from the very beginning.
If you’re running containers, microservices, or Kubernetes clusters, traditional security tools often fall short. They were designed for old-school data centers with fixed servers and clear perimeters. Today’s environments are dynamic, scalable, and spread across multiple clouds. A single misconfiguration can expose sensitive data to the world in seconds.
In this post, we’ll walk through everything you need to know about Cloud-Native Security Architectures. You’ll learn what they are, why they matter more than ever in 2026, the core building blocks, practical ways to implement them, common pitfalls to avoid, and what the future holds. Whether you’re a developer, DevOps engineer, security professional, or business leader, you’ll come away with clear, actionable insights you can start using right away.

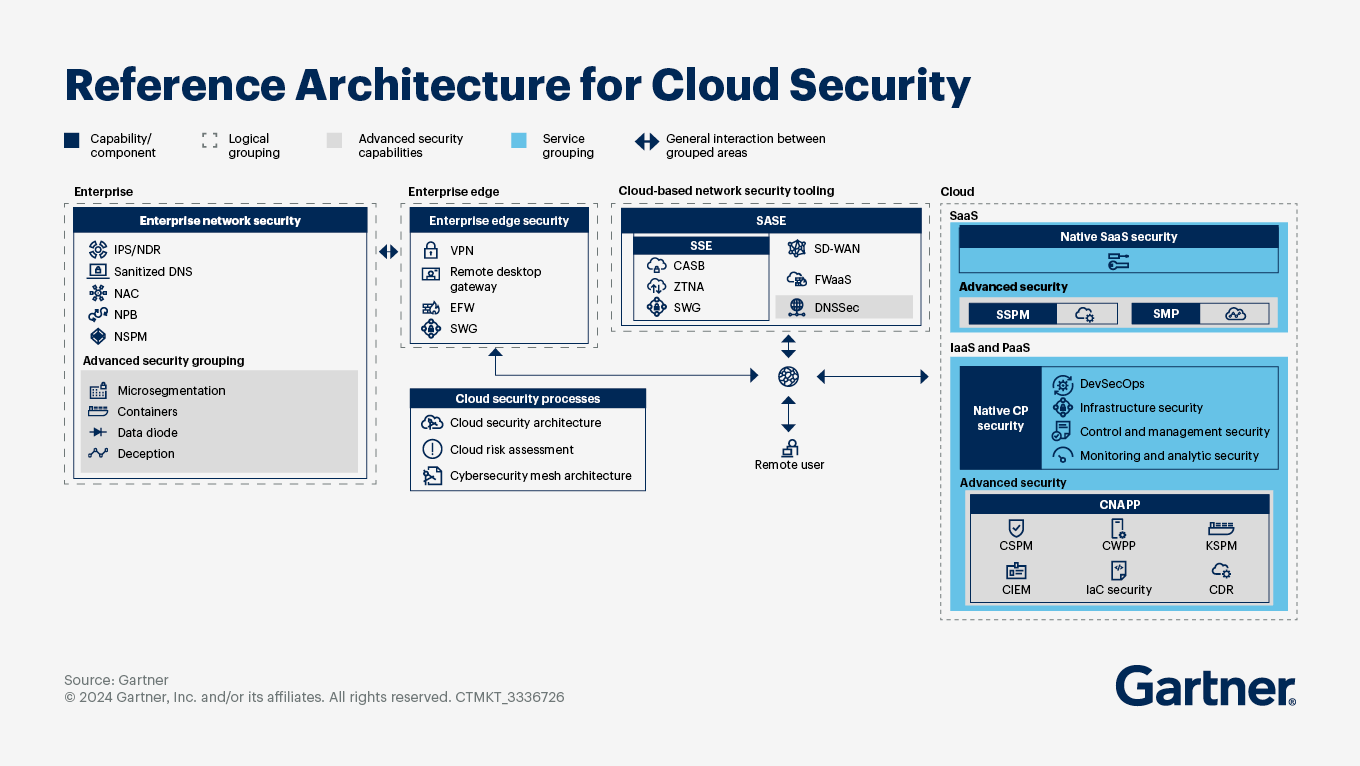
Image credit: Reference Architecture for Cloud Security from Gartner (gartner.com)
Why Cloud-Native Security Architectures Matter More Than Ever
Think about your favorite streaming service or online shopping app. It handles millions of users, updates multiple times a day, and scales automatically during peak hours. Behind the scenes, it’s built with containers that spin up and down in seconds, microservices talking to each other constantly, and data flowing across global regions.
Traditional security puts a big wall around everything—like a castle moat. Cloud-native setups don’t have a single wall. Instead, they’re more like a bustling city with many neighborhoods, streets, and buildings. You need security at every street corner, inside every building, and even between rooms.
Recent industry reports show cloud-related incidents continue to rise. Misconfigurations remain the top cause of breaches, and attackers are getting smarter about exploiting the speed and complexity of modern deployments. At the same time, regulations like GDPR, CCPA, HIPAA, and emerging AI-specific rules demand stronger controls.
Cloud-Native Security Architectures solve this by making security automatic, scalable, and integrated into every layer. They follow the “shift left” mindset—catching problems early in development rather than after deployment. They embrace zero trust, where nothing is automatically trusted, no matter where it lives. And they use automation so security keeps pace with rapid releases.
By the end of this post, you’ll understand how to design these architectures so your teams can move fast without compromising safety. Let’s start with the basics.
What Exactly Are Cloud-Native Security Architectures?
Cloud-Native Security Architectures refer to security designs specifically created for applications built using cloud-native technologies. These include containers (like Docker), orchestration platforms (like Kubernetes), microservices, serverless functions, and infrastructure as code.
The key difference from traditional security? Everything is baked in from day one. Security isn’t a separate team or tool that reviews things at the end. It’s part of the code, the pipelines, the runtime environment, and the underlying cloud infrastructure.
At its heart, this approach follows the Cloud Native Computing Foundation (CNCF) guidance. It treats security as a shared responsibility across developers, operations, and security teams—often called DevSecOps.
These architectures are:
- Layered: Protection at code, container, cluster, and cloud levels (more on the famous 4 Cs below).
- Dynamic: They adapt as resources scale up or down.
- Automated: Policies, scans, and responses happen without manual intervention.
- Immutable: Once something is deployed, it’s treated as unchangeable—any update means a fresh, verified version.
- Observable: You get full visibility into what’s happening across distributed systems.
In simple terms, imagine building a house. Traditional security is like adding locks after the house is built. Cloud-native security is like designing reinforced doors, smart cameras, and secure foundations while the blueprints are still being drawn.
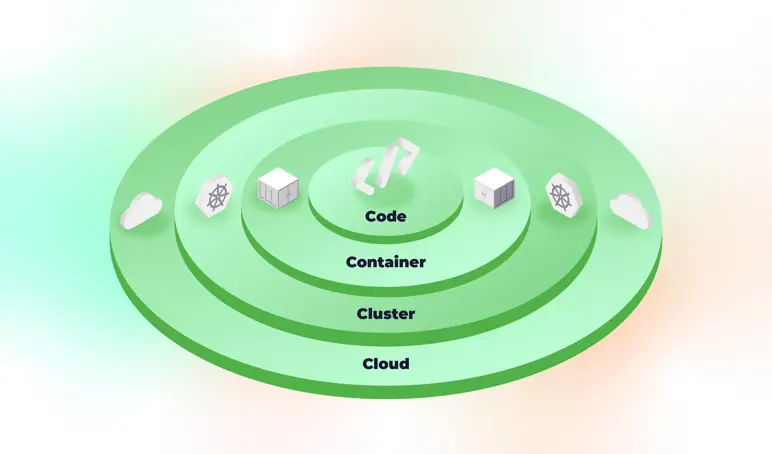
Image credit: Illustration of the 4 Cs of Cloud-Native Security from intercept.cloud
Breaking Down the 4 Cs of Cloud-Native Security
One of the most helpful frameworks for understanding Cloud-Native Security Architectures comes from the CNCF and has been widely adopted across the industry. It’s called the 4 Cs: Code, Container, Cluster, and Cloud. Each layer builds on the one inside it, so a weakness in any layer can affect the whole system. Let’s explore each one in detail.
Code – The Innermost Layer
Everything starts with the application code itself. Secure code is the foundation. This means writing code that avoids common vulnerabilities like injection attacks, using up-to-date libraries, and following secure coding practices.
In practice, teams use static application security testing (SAST) tools during development. They scan for secrets accidentally committed to repositories and enforce code reviews with security checklists. Supply chain security also matters here—making sure open-source dependencies haven’t been tampered with.
A real benefit? When code is secure from the start, you reduce the number of issues that show up later, saving time and money.
Container – Packaging Your Applications
Containers package your code along with its dependencies into lightweight, portable units. But containers can introduce risks if not handled properly—think vulnerable base images or overly permissive configurations.
Security at this layer includes scanning container images for known vulnerabilities before they’re pushed to registries. You sign images to verify they haven’t been altered. You also run containers with the least privileges possible and avoid running them as root.
Tools that perform image scanning and runtime protection help here. The goal is to make sure every container that starts in your environment is clean and stays that way.
Cluster – The Orchestration Layer
Most cloud-native apps run on Kubernetes or similar orchestrators. The cluster manages hundreds or thousands of containers, networking, storage, and scaling.
At the cluster level, you apply network policies to control which pods can talk to each other. You use pod security standards to enforce rules on what containers can do. Role-based access control (RBAC) limits who can manage the cluster. And you monitor the control plane for suspicious activity.
A well-secured cluster feels invisible to attackers—no easy entry points, and lateral movement is blocked.
Cloud – The Foundation Layer
This is the underlying infrastructure provided by AWS, Azure, Google Cloud, or your chosen provider. Even though the provider handles physical security, you’re responsible for configuring resources correctly.
This includes proper identity and access management (IAM), encrypting data at rest and in transit, enabling logging and monitoring, and using cloud-native firewalls or web application firewalls.
The shared responsibility model is crucial here: the provider secures the cloud, but you secure what you put in it.
When all four layers work together in your Cloud-Native Security Architectures, you create defense in depth that matches the speed and flexibility of modern apps.
Image credit: CNAPP and 4 Cs visualization from LinkedIn post by Bill Ho (linkedin.com)
Core Principles That Guide Effective Cloud-Native Security Architectures
Beyond the 4 Cs, successful architectures rest on timeless principles adapted for the cloud era.
Zero Trust is the biggest one. Never trust, always verify. Every request—whether from inside or outside the network—must be authenticated and authorized. In practice, this means mutual TLS between services, continuous validation of identities, and micro-segmentation so a compromised pod can’t reach everything else.
Shift Left Security means moving security checks earlier in the development lifecycle. Instead of waiting for a penetration test after deployment, you scan code as it’s written, test infrastructure as code, and run security gates in CI/CD pipelines.
Automation Everywhere is non-negotiable. Manual processes can’t keep up with hundreds of deployments per day. Policy as code (using tools like Open Policy Agent) lets you define rules once and enforce them automatically.
Immutable Infrastructure treats servers and containers as disposable. If something changes or looks suspicious, you replace it with a fresh, known-good version rather than patching on the fly.
Least Privilege ensures users, services, and processes have only the minimum permissions needed—and those permissions are reviewed regularly.
Defense in Depth layers multiple controls so that if one fails, others still protect you.
Secure by Default means systems come with safe settings out of the box. Turning on extra risky features should require deliberate action and approval.
These principles aren’t theoretical. Organizations that follow them report fewer incidents, faster recovery, and happier development teams because security stops feeling like a blocker.
Key Components You’ll Find in Strong Cloud-Native Security Architectures
Let’s look at the practical pieces that make these architectures work.
Identity and Access Management (IAM)
Modern IAM goes beyond simple usernames and passwords. It includes short-lived credentials, just-in-time access, and context-aware decisions (who is requesting, from where, on what device, at what time). Federated identity with single sign-on and multi-factor authentication are table stakes.
Network Security and Service Mesh
In microservices environments, traffic flows in complex patterns. A service mesh like Istio adds encryption, traffic control, and observability without changing application code. Network policies in Kubernetes act like internal firewalls.
Image credit: Istio service mesh architecture from Medium article by Harsh
Secrets Management
Never hard-code passwords or API keys. Use dedicated tools to store, rotate, and inject secrets securely at runtime.
Vulnerability and Compliance Management
Continuous scanning for vulnerabilities in code, containers, and infrastructure. Cloud Security Posture Management (CSPM) tools check configurations against best practices and compliance frameworks.
Runtime Protection
Even the best prevention can miss something. Runtime tools watch for anomalous behavior inside running containers and clusters, blocking threats in real time.
Observability and Incident Response
Logs, metrics, and traces from every layer feed into centralized platforms. When something looks wrong, automated playbooks can isolate affected resources quickly.
Cloud-Native Application Protection Platforms (CNAPP)
These all-in-one platforms combine many of the above capabilities into a single pane of glass. They’re becoming the standard for enterprises because they reduce tool sprawl.
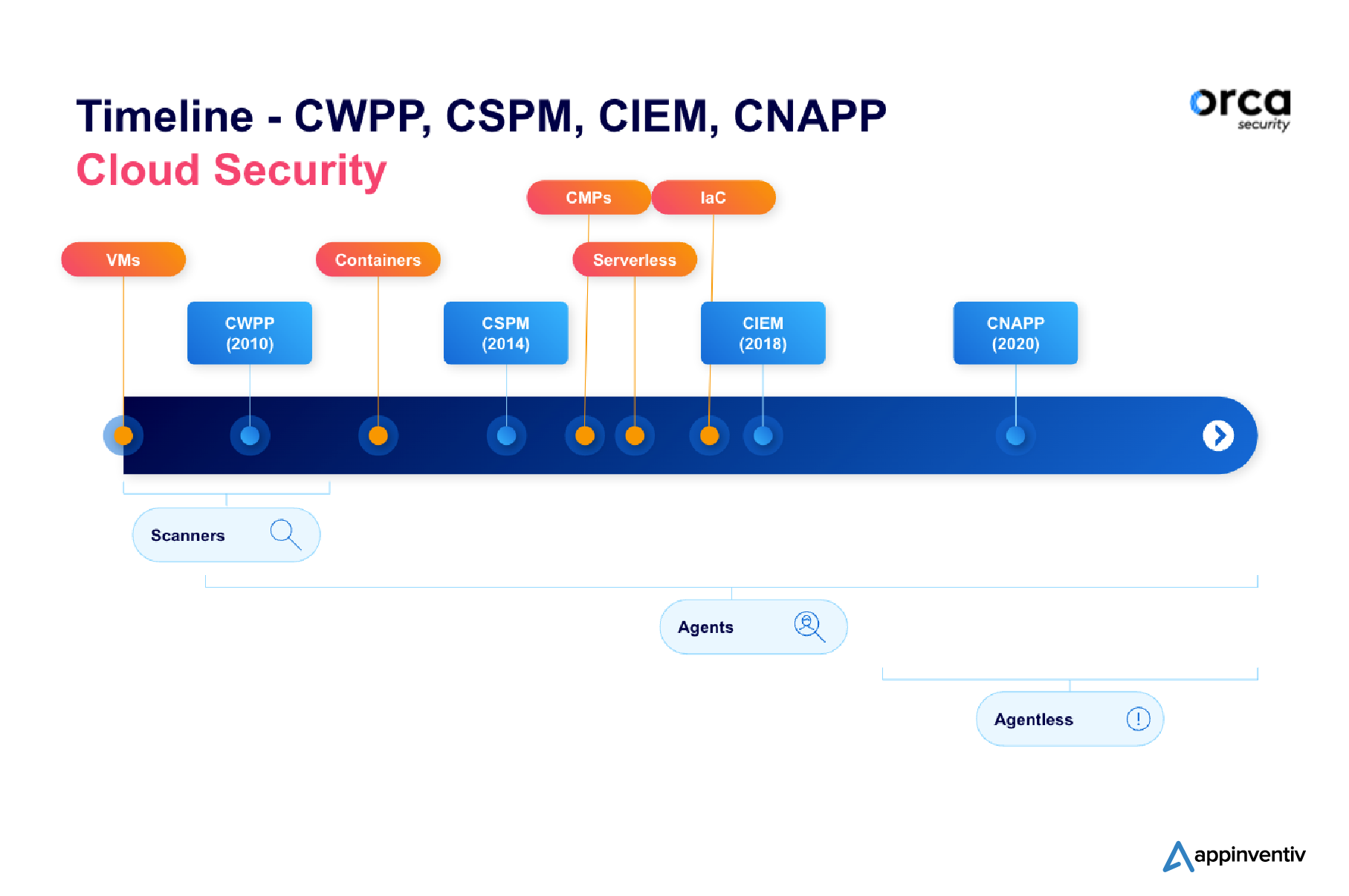
Image credit: CNAPP evolution timeline from appinventiv.com
Together, these components create Cloud-Native Security Architectures that are proactive rather than reactive.
How to Implement Cloud-Native Security Architectures in Your Organization
Implementation doesn’t happen overnight, but a phased approach works well.
Start with assessment. Map your current applications, identify which are already cloud-native or candidates for modernization, and review existing security controls. Look for quick wins like enabling basic encryption and fixing obvious misconfigurations.
Next, define your target architecture. Choose your orchestration platform, decide on a service mesh if needed, and document security policies for each of the 4 Cs.
Integrate security into pipelines. Add scanning steps, policy checks, and approval gates. Train teams on secure coding and infrastructure as code best practices.
Roll out gradually. Begin with non-production environments, then move to low-risk production workloads. Use feature flags and canary deployments to minimize risk during rollout.
Monitor, measure, and improve. Track metrics like mean time to detect issues, number of vulnerabilities remediated early, and compliance score. Hold regular retrospectives to refine the architecture.
Many organizations find that starting small with one application or team builds momentum and proves value quickly. Over time, the practices spread naturally across the enterprise.
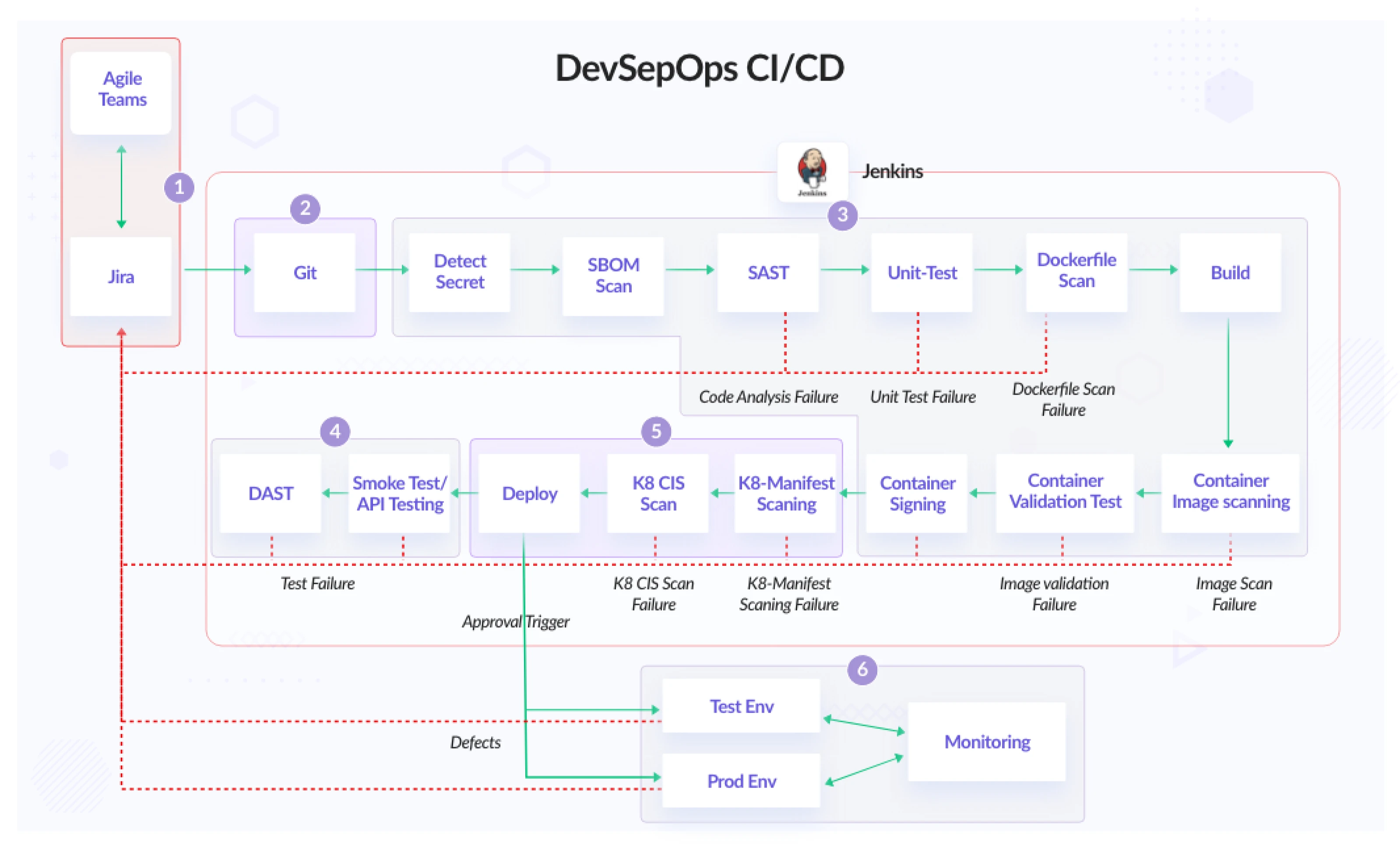
Image credit: Detailed DevSecOps CI/CD pipeline from infracloud.io
Best Practices for Cloud-Native Security Architectures in 2026
Here are proven practices that leading teams follow today:
- Adopt Zero Trust as the default model.
- Use infrastructure as code with built-in security scanning.
- Implement strict pod security standards and network policies.
- Rotate credentials and certificates automatically.
- Encrypt everything—data at rest, in transit, and even in use where possible.
- Enable comprehensive logging and monitoring with anomaly detection.
- Conduct regular chaos engineering and security tabletop exercises.
- Automate compliance reporting to stay audit-ready.
- Choose CNAPP solutions that provide unified visibility across clouds.
- Foster a culture where security is everyone’s responsibility through training and incentives.
- Keep supply chain security top of mind with SBOMs (Software Bill of Materials) and signed artifacts.
- Prepare for AI-powered threats by using AI-powered defenses too.
- Test your architectures regularly with red team exercises that simulate real cloud-native attack paths.
Following these consistently dramatically reduces your risk profile while maintaining velocity.
Real-World Examples of Cloud-Native Security Architectures in Action
A large financial services company moved its core banking platform to Kubernetes. They implemented a service mesh for encrypted east-west traffic, policy as code for all deployments, and runtime protection that blocked a cryptomining attempt within minutes of detection. Their time to remediate vulnerabilities dropped by over 70%.
A healthcare provider used the 4 Cs framework to secure patient data apps across multiple clouds. They achieved HIPAA compliance with automated controls and reduced manual audit effort by 80%.
These aren’t rare success stories anymore—they’re becoming the norm for organizations that treat Cloud-Native Security Architectures as a strategic advantage rather than a cost center.
Common Challenges and Practical Solutions
Challenge 1: Complexity and tool sprawl. Solution: Start with a CNAPP that consolidates capabilities. Standardize on a small set of tools across teams.
Challenge 2: Skills gap. Solution: Invest in cross-training. Developers learn basic security, security teams learn cloud-native concepts. Use managed services where possible.
Challenge 3: Balancing speed and security. Solution: Automate everything possible. Make secure paths the easiest paths for developers.
Challenge 4: Multi-cloud or hybrid environments. Solution: Use vendor-agnostic tools and abstractions like service meshes that work consistently everywhere.
Challenge 5: Supply chain risks. Solution: Implement full provenance tracking and verify every artifact.
With thoughtful planning, these challenges become manageable.
Popular Tools and Technologies Supporting Cloud-Native Security Architectures
Open-source favorites include:
- Kubernetes with its built-in security features
- Istio or Linkerd for service mesh
- Vault for secrets
- Falco for runtime detection
- OPA/Gatekeeper for policy enforcement
- Trivy or Clair for image scanning
Commercial platforms like Wiz, Sysdig, Orca Security, and Palo Alto Networks Prisma Cloud offer comprehensive CNAPP capabilities with excellent multi-cloud support.
Explore official resources:
- CNCF Cloud Native Security Whitepaper
- Kubernetes Security Documentation
- Istio Security Best Practices
Internal link: Read our deep dive on Zero Trust implementation here
Future Trends Shaping Cloud-Native Security Architectures
Looking ahead to late 2026 and beyond:
- AI and machine learning will drive smarter threat detection and automated response.
- Post-quantum cryptography will start appearing in cloud services to prepare for future computing threats.
- GitOps will become the standard way to manage both infrastructure and security policies.
- Greater emphasis on data-centric security as applications become more distributed.
- Tighter integration between security and observability platforms.
- Regulatory requirements will continue to evolve, pushing more automation in compliance.
Organizations that stay ahead of these trends will turn security into a competitive differentiator.
Wrapping Up: Start Building Your Cloud-Native Security Architectures Today
Cloud-Native Security Architectures represent the evolution of how we protect applications in a world that never stops changing. By embracing the 4 Cs, zero trust principles, automation, and layered defenses, you create systems that are not only secure but also resilient, scalable, and developer-friendly.
The journey requires commitment across teams, but the payoff is enormous: fewer breaches, faster innovation, and peace of mind as your business grows.
Ready to take the next step? Assess your current setup against the principles we’ve covered. Pick one area—maybe container image scanning or network policies—and strengthen it this week. Small consistent improvements compound into world-class security.
If you found this guide helpful, share it with your team and bookmark it for reference. For more on related topics like DevSecOps pipelines or multi-cloud strategies, explore the rest of our blog.
Security isn’t a destination—it’s a continuous journey. With the right Cloud-Native Security Architectures, you’ll be well-equipped for whatever comes next in the cloud.
Share this content:













Post Comment