Cyber Capability Benchmarking
Businesses and organizations face constant risks from cyber attacks. Whether it’s a small company or a large corporation, everyone needs to know how strong their defenses are. That’s where cyber capability benchmarking comes in. It’s a way to measure and compare your cybersecurity strengths against standards or peers, helping you spot weaknesses and build better resilience against threats. With hackers getting smarter every day, understanding cyber capability benchmarking isn’t just helpful—it’s essential for staying safe in this unpredictable environment.
This post will about what cyber capability benchmarking means, why it matters, and how you can use specific metrics to gauge your organization’s resilience. We’ll look at real-world examples, tools, challenges, and even what’s coming next. If you’re running a business or handling IT security, this guide will give you practical insights to strengthen your setup.
What is Cyber Capability Benchmarking?
At its core, cyber capability benchmarking is about evaluating your organization’s ability to handle cyber threats. It’s like giving your security system a report card. You compare your practices, tools, and responses to industry standards or similar organizations to see where you stand.
Why do this? Well, the cyber world changes fast. New threats pop up all the time, from ransomware to phishing scams. Benchmarking helps you identify gaps before they become problems. For instance, it can show if your team responds quickly to incidents or if your systems are outdated.
According to a report from MITRE, cyber resiliency metrics focus on goals like anticipating, withstanding, recovering, and evolving from attacks . This ties directly into benchmarking because it gives you measurable ways to track progress. Without it, you’re guessing if your security investments are paying off.
Think of it as a health check for your digital assets. Just like you benchmark your website’s speed against competitors for better SEO (check out our post on website optimization tips for more on that), cyber capability benchmarking ensures your defenses are up to par.
The Evolving Cyber Threat Landscape
The threats we face today are more complex than ever. Hackers use advanced tools like AI to launch attacks, and the rise of remote work has opened new doors for vulnerabilities. In a volatile landscape, things like supply chain attacks or zero-day exploits can hit without warning.
For example, recent years have seen a spike in ransomware, where attackers lock up your data and demand payment. According to Bitsight, third-party risks are a leading cause of breaches . This means even if your own systems are secure, a weak partner can bring you down.
Visualizing this helps. Here’s an infographic showing common threat points in modern networks:
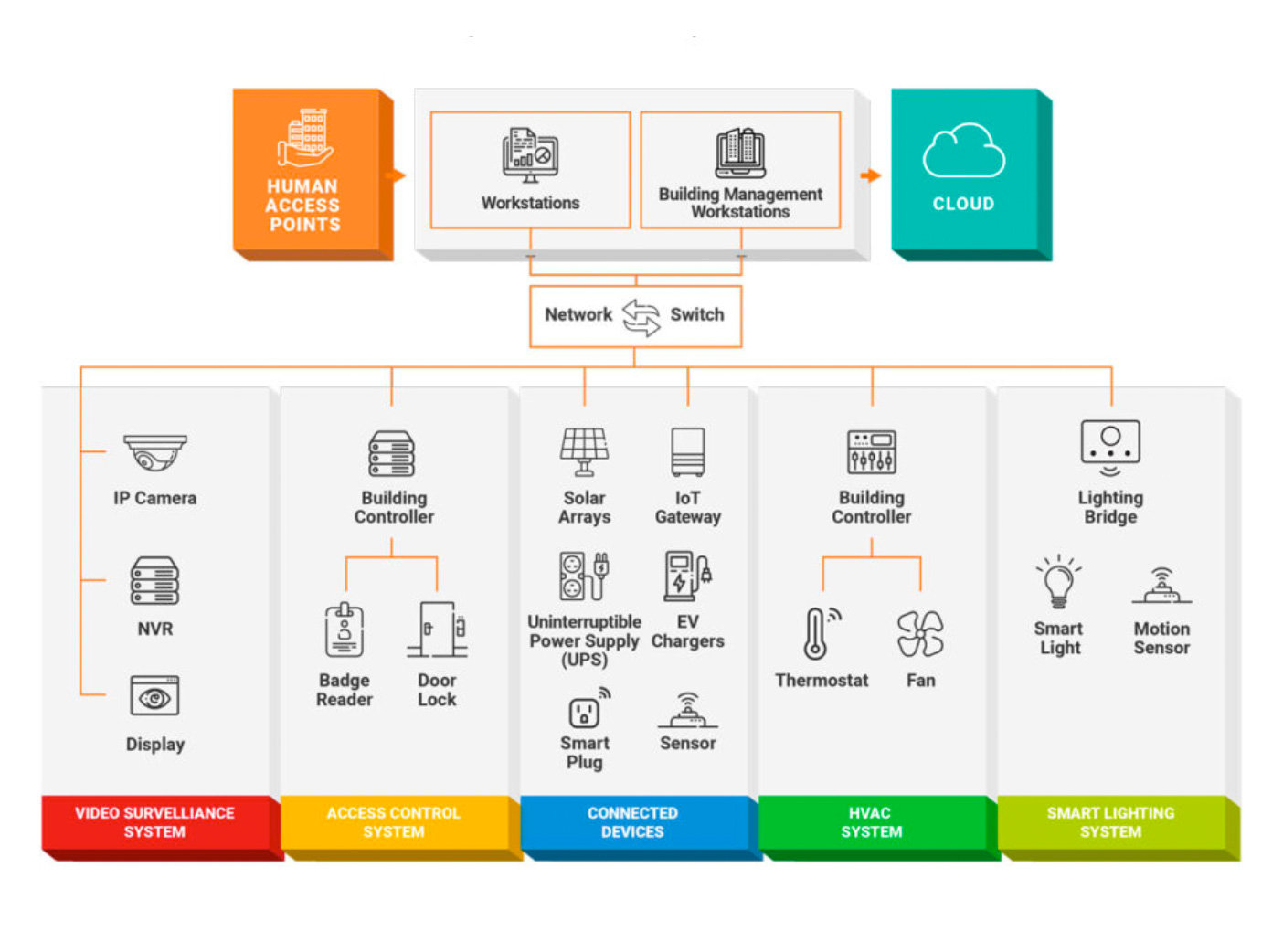
Credit: Industrial Defender – Infographic on Cyber Threat Landscape in Buildings
To measure resilience here, cyber capability benchmarking looks at how well you can spot and stop these threats. It’s not just about having antivirus software; it’s about having a full strategy.
Internally, we’ve covered similar topics in our guide to emerging cyber threats. Linking out to Help Net Security’s report on cyber metrics offers more on global trends.
Understanding Cyber Resilience
Cyber resilience goes beyond prevention—it’s about bouncing back from attacks. In a volatile threat landscape, resilience means your operations keep running even during an incident.
Key elements include detection, response, and recovery. For benchmarking, you measure how resilient you are using metrics tied to these areas. The MITRE framework breaks it down into goals: anticipate threats, withstand them, recover quickly, and adapt for the future .
Resilience isn’t static. It evolves with threats. For businesses, this means regular assessments to ensure your capabilities match the risks.
A good starting point is understanding your baseline. Use tools to scan for weaknesses, then benchmark against standards like NIST.
Key Metrics for Cyber Capability Benchmarking
Metrics are the heart of cyber capability benchmarking. They turn vague ideas into hard numbers. Here are some essential ones, drawn from industry sources.
Detection Metrics
- Mean Time to Detect (MTTD): How long it takes to spot a threat. Lower is better. InformationWeek notes this as a core metric for resilience .
- Detection Coverage: Percentage of systems monitored. Aim for 100% on critical assets.
Response Metrics
- Mean Time to Respond (MTTR): Time from detection to action. N-able highlights this for MSPs .
- Incident Response Effectiveness: Success rate in containing breaches.
Recovery Metrics
- Recovery Time Objective (RTO): Target time to restore operations.
- Recovery Point Objective (RPO): Acceptable data loss amount.
Overall Resilience Metrics
- Security Rating: Bitsight’s tool gives a score based on posture .
- Patch Compliance Rate: Percentage of systems updated promptly.
- Employee Awareness Score: From phishing tests.
From the FAIR Institute, metrics like number of attack scenarios identified help quantify progress .
Visual dashboards make this easier. Check this example of a metrics dashboard:
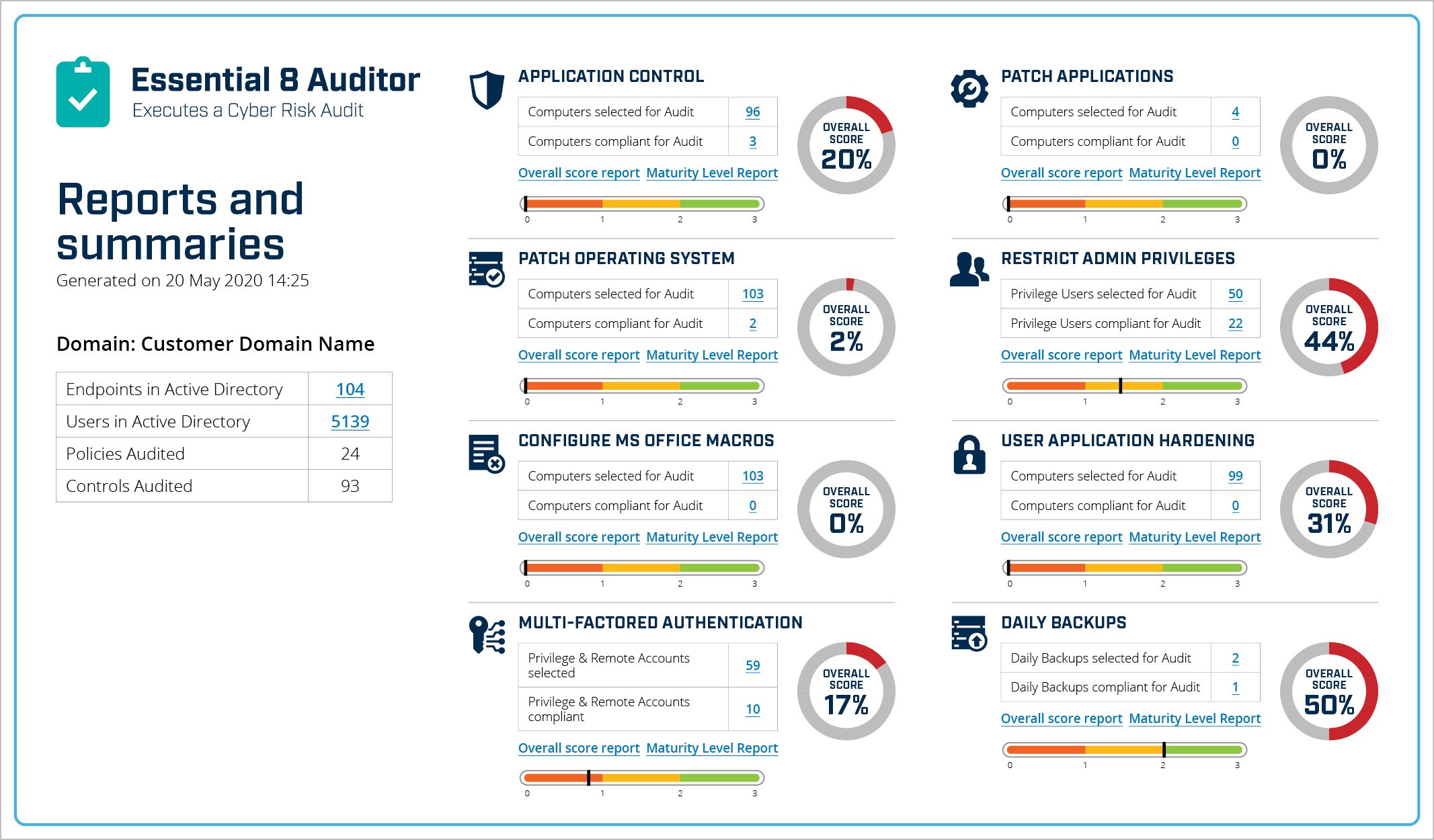
Credit: Huntsman Security – Cyber Security Metrics Dashboard
In our internal post on security metrics, we dive deeper into tracking these.
To expand, let’s list steps to calculate MTTD:
- Log all incidents.
- Note detection times.
- Average them out.
This simple process can reveal big issues.
Another metric from Sandia: Elapsed Time to Identify Failure (ETIF) . It’s crucial for quick recovery.
Benchmarking these against peers helps. For example, if your MTTR is 24 hours but industry average is 4, you know to improve.
Case in point: A financial firm might benchmark against FS-ISAC’s Threat Resilience Metric .
Frameworks for Cyber Capability Benchmarking
Frameworks provide structure. Popular ones include NIST CSF, ISO 27001, and CIS Controls.
NIST Cybersecurity Framework
NIST CSF has five functions: Identify, Protect, Detect, Respond, Recover . It’s flexible for benchmarking maturity.
Tiers range from partial to adaptive. Use it to score your program.
Here’s a diagram of the NIST framework:
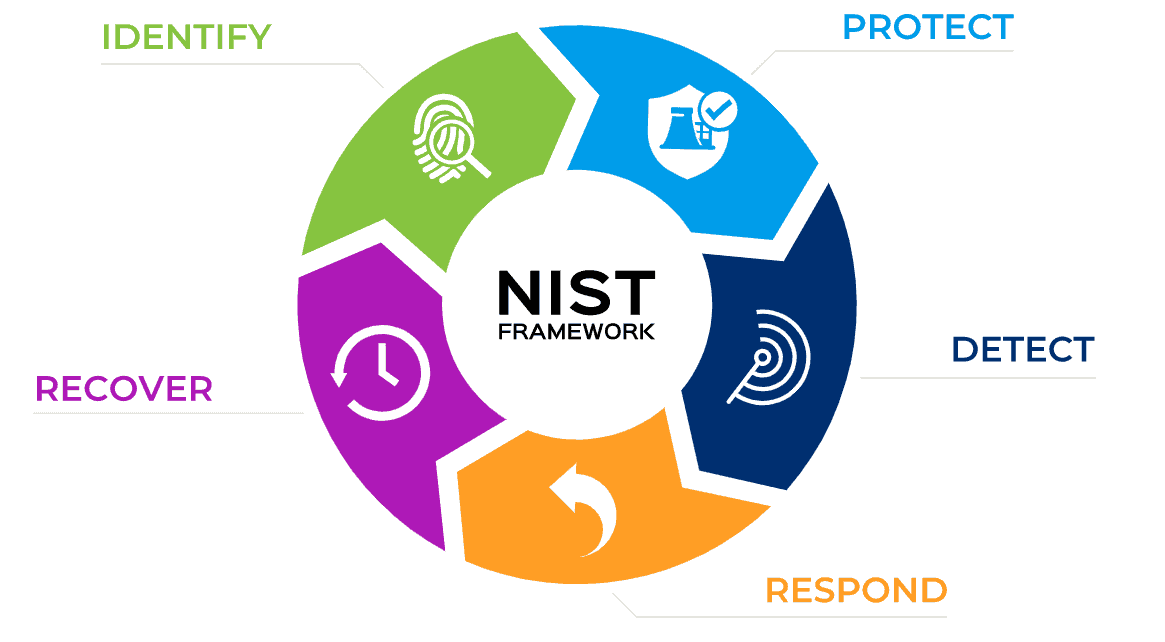
Credit: University of South Carolina – NIST Cybersecurity Framework Diagram
Compare to ISO 27001, which focuses on ISMS . NIST is US-centric, ISO international.
CIS Benchmarks offer configuration guides .
For implementation, map your controls to these. CyberSaint explains benchmarking to NIST .
External: NIST’s official site.
Tools and Technologies for Benchmarking
Tools automate benchmarking. Examples:
- Bitsight Security Ratings: Tracks performance .
- C2M2: From DOE, evaluates maturity .
- CIS-CAT Pro: Assesses against Benchmarks .
- EY Benchmarking Tool: Visualizes posture .
Screenshots help visualize:
Credit: Center for Internet Security – CIS Benchmarking Tools Screenshot
OpenVAS and Nessus for vulnerability scanning .
For AI, Cybench benchmarks LLMs for cyber tasks .
Case Studies in Cyber Capability Benchmarking
Seeing how others have tackled cyber capability benchmarking brings the concept to life. These real-world examples show how organizations and governments use metrics to boost resilience, spot weaknesses, and adapt to threats. They highlight the value of comparing your setup against standards or peers, often leading to better security and fewer disruptions. Let’s explore a few in detail, pulling from studies and reports that demonstrate practical applications.
First, consider the PwC Global Cyber Benchmarking Study, which looks at how countries build cyber resilience through policies, collaborations, and laws. This study surveyed experts from 11 countries across four continents, including Canada, Germany, France, Hong Kong, Israel, Morocco, the Netherlands, Singapore, South Africa, Tunisia, and Ukraine. The methodology involved 40 questions on three main areas: national standards (like strategies and certifications), organizational capabilities (such as dedicated agencies and training programs), and legislation (covering data privacy and risk assessments). Key findings show that successful countries integrate cyber security into bigger goals like economic growth and public safety. They emphasize public-private partnerships and align with international standards. For example, the study introduces the “Cyber Skyward Curve,” a four-phase framework to guide progress from fragmented policies to a culture of resilience. In practice, countries like Singapore and Israel stand out for their strong investments in skills and research, helping them benchmark and improve resilience scores. This approach has led to better enforcement of laws and faster responses to attacks, reducing vulnerabilities in critical sectors.
Another strong example comes from MITRE’s work on cyber resiliency metrics and scoring through use cases. MITRE developed a methodology to create scenarios that test resilience under different conditions, like operational stresses or threats. The process involves building use cases with elements such as architectures, threats, and metrics for scoring effectiveness. One detailed example is the “Vehicle Use Case,” which simulates a cyber attack on connected vehicles, measuring things like anticipation of threats and recovery times. This helps organizations benchmark their capabilities by applying analytic methods to notional examples, identifying trade-offs, and assigning scores. The outcome? Companies can see where their resilience falls short—say, in withstanding attacks—and make targeted improvements. This has been applied in defense and transportation sectors, showing how benchmarking leads to more adaptive systems that evolve with threats.
Moving to the public sector, the Government of Canada’s GC Enterprise Cyber Security Strategy is a solid case of building resilience at a national level. Launched in May 2024, this initiative aims to secure digital services amid rising threats like espionage and supply chain risks. Objectives include articulating cyber risks for better decisions, preventing attacks with “secure by design” principles, and fostering a skilled workforce. Strategies involve a Target Security Operating Model (TSOM) aligned with policies like the Policy on Government Security, incorporating zero trust and data-centric approaches. They’ve set up Purple Teams for testing, improved vulnerability management, and mandated training. Outcomes include faster threat detection, better inter-departmental coordination, and stronger data protection. While specific metrics aren’t detailed, the strategy uses maturity models for continuous compliance, benchmarking progress against frameworks like NIST. This has helped Canada reduce disruptions in services, with plans for endpoint security and third-party risk management to keep resilience high.
From the academic side, a survey of cyber resilience case studies in scientific literature reveals diverse approaches to benchmarking. Researchers reviewed studies that focus on risk assessments, framework evaluations, and new tools for measuring resilience. Some cases emphasize complex risk management processes, while others propose custom frameworks. Key implications include the need for adaptable metrics that cover anticipation, recovery, and adaptation. For instance, one study applied resilience metrics to a water treatment plant, identifying gaps and improving defenses against cyber threats. This shows how benchmarking can quantify maturity levels, from basic to advanced, helping organizations in critical infrastructure like power grids or healthcare to prioritize spending and benchmark against standards.
Finally, in critical infrastructure, the InfraGuard Cybersecurity Framework offers a metric for resilience in vital systems. This model measures maturity through three pillars: Cyber as a Shield (protection), Cyber as a Space (operations), and Cyber as a Sword (response). Applied to power grids, healthcare, and airports, it scores organizations on levels from incomplete to sophisticated. A case study on a water plant used this to map gaps, integrate with NIST and ISO, and boost metrics like incident recovery time. Outcomes include fewer false positives in alerts and better benchmarking against peers, proving that structured metrics lead to stronger, more quantifiable resilience.
These cases underline a common theme: benchmarking isn’t a one-time task. It drives ongoing improvements, from policy tweaks in governments to tech upgrades in industries. Organizations that regularly compare their metrics see fewer breaches and quicker recoveries, turning potential disasters into manageable events.
For more inspiration, check out the World Economic Forum’s cyber resilience case studies, which cover various industries. Internally, see our cyber case study series for more examples.
Challenges in Cyber Capability Benchmarking
It’s not easy. Challenges include:
- Data Quality: Inaccurate data skews metrics .
- Talent Shortages: Hard to find experts .
- Overconfidence: 94% think they’re ready, but scores say otherwise .
- Scalability: For large systems .
- Evolving Threats: Benchmarks outdated quickly .
Wavestone notes plateaus in maturity .
Solutions: Use AI for automation .
Future Trends in Cyber Capability Benchmarking
Looking ahead, AI will dominate. Trends:
- AI-Driven Metrics: Predictive analytics .
- Quantum Security: New benchmarks needed .
- Zero Trust Integration: In all frameworks .
- GenAI Risks: 97% report issues .
Illustrations capture this:
Credit: Security Magazine – Cybersecurity Trends Illustration
Gartner predicts AI reshaping defenses .
SentinelOne on 2026 trends .
How to Implement Cyber Capability Benchmarking
Step-by-step:
- Assess current state.
- Choose framework (e.g., NIST).
- Select metrics.
- Use tools for data.
- Compare to benchmarks.
- Act on gaps.
- Review regularly.
Budget for it—cyber spending rises .
For small businesses, start simple.
Conclusion
Cyber capability benchmarking is your roadmap to resilience in a tough threat landscape. By using metrics, frameworks, and tools, you can measure and improve your defenses. Don’t wait for a breach—start benchmarking today.
Remember, it’s ongoing. Stay updated with trends and adjust.
For more, explore MDIC’s benchmarking report.
Thanks for reading! Share your thoughts below.
Share this content:













Post Comment