Non-Human Identity Federation
In the fast-paced world of technology, businesses rely more on machines, software, and devices to handle tasks that once needed human input. Think about smart thermostats adjusting your home temperature, bots handling customer queries on websites, or AI agents automating complex workflows in offices. These “non-human” entities need secure ways to identify themselves and access resources, just like people do with usernames and passwords. That’s where non-human identity federation comes in. It’s a system that allows these entities—agents, bots, and IoT devices—to federate or share identities across different systems securely. By scaling public key infrastructure (PKI), organizations can manage this in zero-trust models, where nothing is trusted by default, and every access is verified continuously.
Non-human identity federation isn’t just a buzzword; it’s essential for modern security. With the rise of AI and connected devices, the number of these identities has exploded. Reports show that for every human user, there could be 25 to 50 non-human ones, like API keys or service accounts. This growth brings risks, but also opportunities to build stronger defenses. In this post, we’ll explore what non-human identity federation means, how PKI helps scale it for agents, bots, and IoT, and why zero-trust models are the perfect fit. Whether you’re a business owner, IT professional, or just curious about tech security, you’ll find practical insights here.

Image credit: softwareanalyst.substack.com
Let’s start with the basics. Non-human identities, or NHIs, are digital credentials given to things that aren’t people. These include software applications, devices, and automated systems that need to interact with networks or other tools. For example, an API key that lets one app talk to another, or a certificate on an IoT sensor that proves it’s legitimate.
In the AI era, NHIs have become even more diverse. Service accounts for cloud apps, OAuth tokens for integrations, and certificates for secure communications are common. AI agents, which are smart programs that can make decisions on their own, might need 15-20 different identities each to access databases, tools, or external services. Bots in customer service or RPA (robotic process automation) also rely on these to function without constant human oversight.
Why do we need to federate them? Federation means linking identities across different domains or systems so they can work together seamlessly. Without it, managing thousands of isolated identities becomes a nightmare. Imagine a bot in your e-commerce site needing access to payment gateways, inventory systems, and customer data—federation ensures it can do that securely without redundant logins.
In zero-trust environments, NHIs are treated with the same suspicion as human users. No automatic trust; every request is checked based on context, like time, location, and behavior. This shift is crucial because attackers often target NHIs—they’re easier to exploit since they don’t have multi-factor authentication like humans do.
For more on basic identity management, check out our guide on understanding identity and access management.
The Role of Federation in Non-Human Identity Management
Federation is like a bridge between different identity systems. In non-human identity federation, it allows agents, bots, and IoT devices to use a single, trusted identity across multiple platforms. This is done through standards like SAML or OAuth, but for machines, it’s often powered by PKI.
Picture this: An IoT device in a factory needs to send data to a cloud server. Without federation, you’d have to set up separate credentials for each interaction. With it, the device uses a federated identity that’s verified once and accepted everywhere in the trusted network.
Benefits include better scalability—handling millions of devices without chaos—and improved security. Federation supports dynamic access, where permissions change based on needs. For AI agents, this means they can federate identities to collaborate with other agents or services without over-privileging.
Challenges? Integration can be tricky in hybrid environments (on-prem and cloud). But tools like decentralized identifiers (DIDs) and verifiable credentials (VCs) are emerging to help. These allow agents to have self-sovereign identities that are cryptographically secure and portable.
External resource: Learn more about DIDs from the W3C specification.
PKI Basics: The Backbone of Secure Identities
Public Key Infrastructure, or PKI, is the technology that makes secure digital identities possible. It uses pairs of keys—public and private—to encrypt data and verify identities. Certificates issued by a Certificate Authority (CA) act as digital IDs.
For non-human entities, PKI is gold. X.509 certificates, for instance, are perfect for machine-to-machine communication. They ensure that a bot or device is who it claims to be, preventing impersonation.
Scaling PKI means automating certificate issuance, renewal, and revocation. Manual management won’t cut it when you have thousands of IoT devices. Tools like HashiCorp Vault automate this, generating short-lived certificates to reduce risks if they’re compromised.
In zero-trust, PKI enables mutual TLS (mTLS), where both sides of a connection verify each other. This is vital for agents accessing sensitive data.
If you’re new to this, read our internal post on PKI fundamentals.
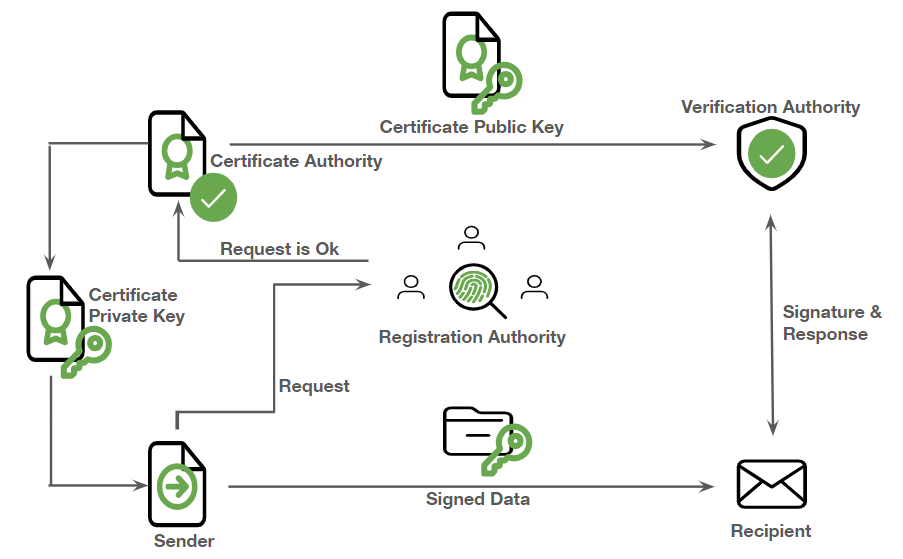
Image credit: hashicorp.com
Zero-Trust Models: No Trust, All Verify
Zero-trust is a security philosophy that assumes threats are everywhere—inside or outside the network. Instead of trusting based on location, it verifies every access request.
For non-human identity federation, zero-trust means continuous verification of NHIs. Core principles include identity-based access, least privilege, and contextual checks. An IoT device might be checked for firmware updates, location, and behavior before granting access.
Applying zero-trust to machines involves automated lifecycles: provisioning, rotation, deactivation. Challenges like legacy devices without modern support can be handled with gateways.
NIST’s SP 800-207 provides a great framework for this. Link to NIST Zero-Trust Architecture.
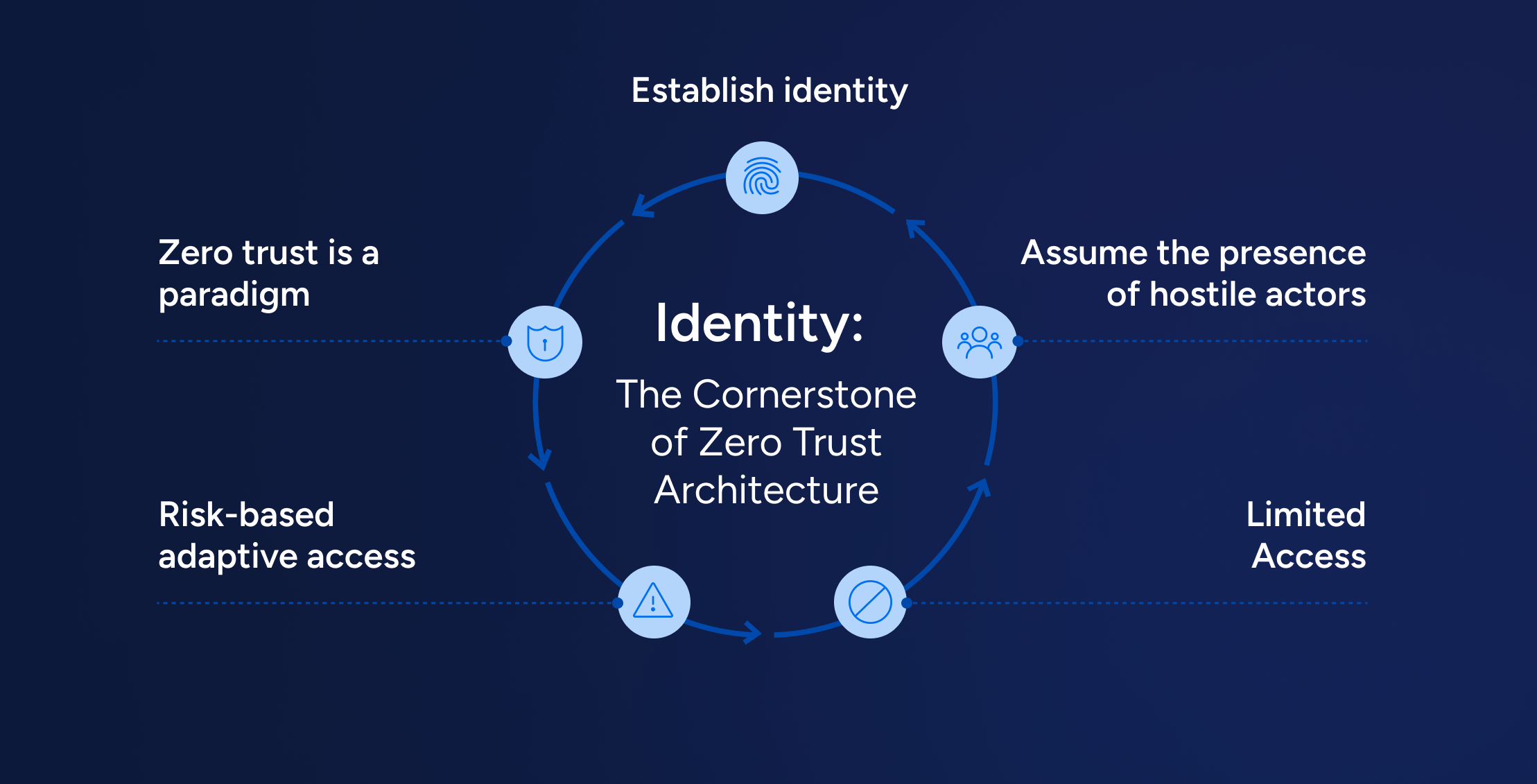
Image credit: veza.com
Scaling PKI for AI Agents
AI agents are autonomous programs that plan and act, like virtual assistants on steroids. They need identities to access tools, data, and other systems.
Non-human identity federation for agents involves using PKI to issue certificates that prove their authenticity. In zero-trust, agents get just-in-time credentials—short-lived to limit damage if hacked.
Scaling means handling proliferation: One agent might spawn many sub-tasks, each needing identities. Solutions like Agent Naming System (ANS) help with discovery and trust.
Case study: A financial AI agent processes invoices. Federated identities let it access ERP systems securely, with audits tracking every action.
Risks? Agents can accumulate entitlements, becoming targets. Mitigate with zero standing privileges (ZSP).
External link: Explore AI agent security at CyberArk’s blog.

Image credit: captcha.eu
Scaling PKI for Bots
Bots, like chatbots or web scrapers, automate repetitive tasks. In e-commerce, a bot might handle orders; in security, it scans for threats.
Federation allows bots to use PKI-based identities across services. Scaling involves automated management—rotating keys regularly to prevent leaks.
In zero-trust, bots are monitored for anomalies, like unusual data access. Tools like Aembit provide secretless access, injecting credentials on demand.
Example: RPA bots in healthcare access patient data. Federated PKI ensures compliance with HIPAA, with revocation if compromised.
For bot security tips, see our bot management guide.
Scaling PKI for IoT Devices
IoT devices—sensors, cameras, smart appliances—number in billions. Each needs an identity to communicate securely.
Non-human identity federation uses PKI to issue device certificates at manufacturing, enabling zero-trust access. Scaling handles lifecycle: Enrollment, updates, revocation.
Challenges: Resource-constrained devices can’t handle complex crypto. Solutions include lightweight protocols and edge gateways.
In smart cities, federated IoT identities allow traffic sensors to share data with control systems securely.
Link to Keyfactor’s IoT security insights.

Image credit: linkedin.com
Challenges in Non-Human Identity Federation
Despite benefits, challenges abound. Proliferation leads to “identity sprawl”—hard to track. Orphaned credentials (30-40% in enterprises) are risks.
Other issues: Integrating legacy systems, ensuring compliance (GDPR, PCI DSS), and handling quantum threats.
Solutions: Automated discovery tools, AI-driven monitoring, and quantum-safe PKI.
Best Practices for Implementation
- Inventory NHIs: Use tools for visibility across environments.
- Automate Lifecycles: Provision, rotate, deprovision automatically.
- Enforce Least Privilege: Just-enough access, just-in-time.
- Monitor and Audit: Behavioral analytics for anomalies.
- Integrate with IAM: Extend human systems to NHIs.
Platforms like Clutch or Aembit help.
For implementation steps, check HashiCorp’s guide.
Case Studies: Real-World Applications
In manufacturing, a company used federated PKI for IoT sensors, reducing breaches by 40%. An e-commerce firm scaled bots with zero-trust, improving response times.
In finance, AI agents with dynamic credentials handled trades securely, complying with regulations.
These show how non-human identity federation pays off.
Future Trends in Non-Human Identity Federation
Looking ahead, decentralized tech like DIDs will dominate. AI governance will automate more, and agent-to-agent protocols will evolve.
With agentic AI growing, expect standards like ANS to standardize trust.
Stay updated with our future tech trends section.
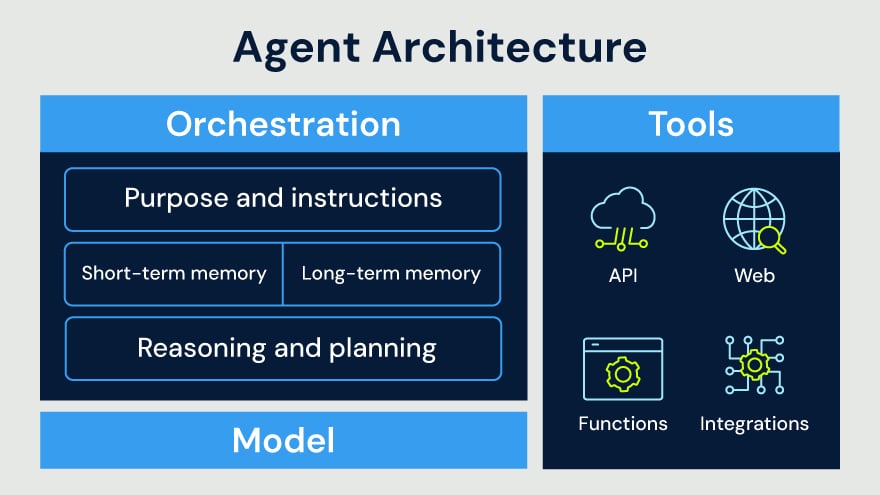
Image credit: cyberark.com
Conclusion
Non-human identity federation is key to securing our increasingly automated world. By scaling PKI in zero-trust models, organizations can manage agents, bots, and IoT devices effectively, reducing risks and boosting efficiency. Start by assessing your NHIs, automating processes, and adopting best practices.The machine-driven future isn’t waiting. Agents, bots, and connected devices are already reshaping how work gets done, and non-human identity federation is the secure bridge that makes it all possible without opening the door to chaos. By embracing scalable PKI in zero-trust frameworks today, you’re not just protecting your organization—you’re positioning it to thrive in an era where identity is everything. The future is machine-driven—make sure your security keeps up.
Share this content:













Post Comment