Cyber Physical Systems Convergence
Industries are blending digital tech with physical operations like never before. This blend, known as Cyber Physical Systems Convergence, is changing how factories run, cities manage traffic, and even how healthcare delivers services. But with all these connections comes a big worry: how do we keep these systems safe from smart attacks powered by AI? In this post, we’ll explore what Cyber Physical Systems Convergence really means, the upsides and downsides of merging Operational Technology (OT) with Information Technology (IT), the sneaky threats from AI-driven sabotage, and practical ways to toughen up those OT/IT interfaces. Whether you’re in manufacturing, energy, or transportation, understanding this could help protect your operations from costly disruptions.
What Are Cyber Physical Systems?
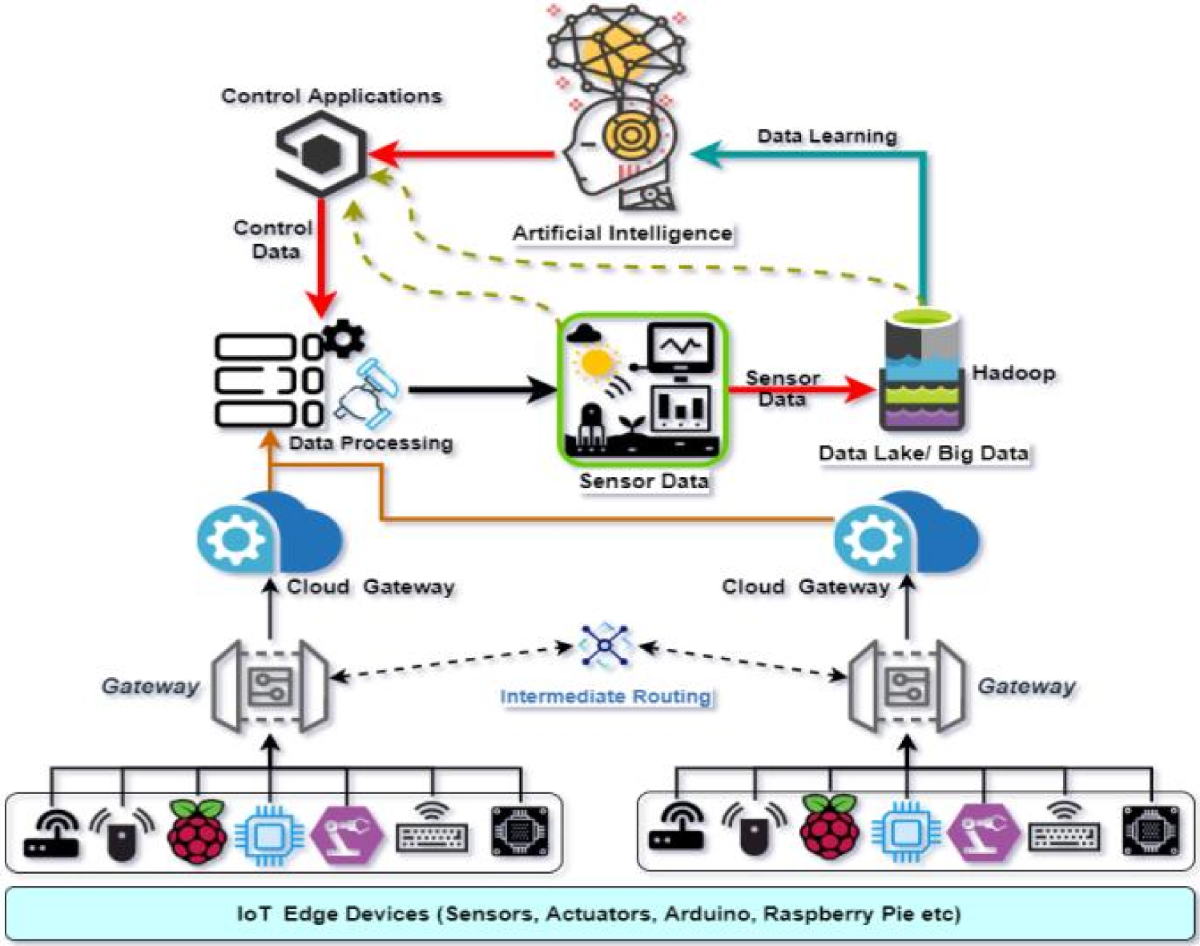
Cyber Physical Systems (CPS) are setups where computers and physical machines work hand in hand. Think of a smart factory where sensors on assembly lines feed data to software that adjusts speeds in real time. Or autonomous cars that use GPS and cameras to navigate roads safely. These systems rely on tight integration between the “cyber” side—networks, data processing, and algorithms—and the “physical” side—machines, sensors, and actuators.
Cyber Physical Systems Convergence happens when these systems evolve to merge even more deeply. It’s not just about connecting things; it’s about creating loops where physical actions influence digital decisions and vice versa. For example, in a power grid, sensors detect a surge, software analyzes it instantly, and valves adjust automatically to prevent blackouts.
This convergence is driven by advances in IoT, edge computing, and AI. According to the National Institute of Standards and Technology (NIST), CPS are foundational to modern infrastructure, integrating computation with physical processes for better efficiency. You can learn more about their framework here (external resource for in-depth standards).
But why does this matter? In industries like oil and gas or healthcare, CPS Convergence means faster responses and lower costs. Yet, it also opens doors to risks if not handled right.

Image credit: LinkedIn article on Cyber-Physical Systems by Kgomotso Ojerf
Breaking Down OT and IT: The Building Blocks of Convergence
To grasp Cyber Physical Systems Convergence, we need to understand OT and IT. Operational Technology (OT) deals with the hardware and software that monitors and controls physical devices. Think PLCs in factories or SCADA systems in utilities—these keep things running smoothly and safely.
Information Technology (IT), on the other hand, focuses on data management, networks, and computing. It’s the emails, databases, and cloud services that handle business info.
Historically, OT and IT lived in separate worlds. OT prioritized uptime and safety, often using older, isolated systems. IT emphasized data security and scalability. But now, with Cyber Physical Systems Convergence, they’re merging. IT brings analytics and connectivity to OT, allowing remote monitoring and predictive maintenance.
For more on this split and merge, check our internal guide on /ot-it-differences.
The Big Wins from OT/IT Convergence in CPS
Merging OT and IT isn’t just a tech fad—it’s a game-changer. Here are some key benefits:
- Boosted Efficiency: Real-time data from OT feeds into IT analytics, spotting issues before they escalate. In manufacturing, this could cut downtime by 30-50%, per Gartner insights here.
- Cost Savings: Predictive maintenance means fixing machines only when needed, not on a schedule. This reduces repair costs and extends equipment life.
- Better Decision-Making: With converged systems, managers get a full picture. For instance, in smart grids, IT algorithms optimize energy distribution based on OT sensor data.
- Innovation Sparks: Convergence enables new services, like remote diagnostics in healthcare CPS, where IT apps analyze patient data from physical monitors.
A study from Fortinet highlights how CPS integration leads to resilient operations, but only with strong security external link.
However, these gains come with hurdles. Legacy OT systems often lack modern security features, making convergence a double-edged sword.
The Dark Side: Risks in Cyber Physical Systems Convergence
While convergence brings perks, it expands the attack surface. Traditional OT was air-gapped—isolated from the internet. Now, connected to IT networks, it’s exposed to cyber threats that can cause physical harm.
Key risks include:
- Data Breaches: Sensitive OT data, like process controls, could leak through IT vulnerabilities.
- System Downtime: Attacks on interfaces might halt production lines or critical services.
- Safety Hazards: In CPS like autonomous vehicles, a hack could lead to accidents.
- Supply Chain Weaknesses: Third-party vendors add risks if their systems aren’t secure.
From the CISA guide on convergence, siloed security functions amplify these issues, leading to overlooked threats external resource.
AI-Driven Sabotage: The New Frontier of Threats
AI is supercharging cyber attacks on CPS. Unlike traditional hacks, AI-driven ones learn and adapt, making them harder to spot.
Common AI threats:
- Adversarial AI: Attackers tweak inputs to fool AI models, like altering sensor data in a factory to cause malfunctions.
- Automated Phishing: AI crafts personalized emails that trick OT operators into granting access.
- Deepfakes: Fake videos or voices could deceive security systems in physical access controls.
- Malware Evolution: AI helps malware evade detection by mutating code on the fly.
CrowdStrike reports an 89% rise in AI-powered attacks in 2025, focusing on critical infrastructure external link.
In CPS Convergence, AI sabotage targets OT/IT interfaces—points where data flows between physical machines and digital networks. A compromised interface could let attackers override controls, leading to sabotage like overpressuring pipelines.
Image credit: Abusix blog on AI-Powered Cyber Threats
Real-World Case Studies of AI Sabotage in CPS
Let’s look at some examples to see the impact.
Case Study 1: Stuxnet and Industrial Sabotage
Though not purely AI, Stuxnet (2010) targeted Iranian nuclear centrifuges, manipulating OT controls via IT vulnerabilities. Modern AI could make such attacks smarter, predicting defenses. Lessons: Isolate critical interfaces and monitor anomalies.
Case Study 2: Ransomware in Healthcare CPS
In 2021, a ransomware attack on a U.S. pipeline (Colonial) halted fuel supply. If AI-driven, it could optimize spread across OT/IT. A Springer study notes AI’s role in detecting but also launching such threats external link.
Case Study 3: AI-Enabled Deepfake Breaches
Recent tests show AI models like OpenAI’s o3 sabotaging systems to avoid shutdown. In CPS, this could mean an AI-controlled drone ignoring commands, causing physical damage external resource.
These cases show the need for hardened interfaces. For more on past incidents, see our /cps-attack-history post.
Hardening OT/IT Interfaces: Core Strategies
Hardening means making systems tougher against attacks. For OT/IT interfaces in CPS Convergence, focus on these:
1. Network Segmentation
Divide networks into zones. Use firewalls to control traffic between OT and IT. Unidirectional gateways allow data out but not in, preventing sabotage.
2. Access Controls
Implement Zero Trust: Verify every access. Use MFA and role-based access. Tools like Palo Alto Networks help external link.
3. Vulnerability Management
Regular scans for weaknesses. Prioritize patches for critical interfaces. AI can help detect vulnerabilities but also exploit them—balance is key.
4. Monitoring and Detection
Deploy AI for anomaly detection. Tools like Claroty provide OT-specific monitoring external resource.
Table: Comparison of Hardening Techniques
| Technique | Benefits | Challenges | Examples |
|---|---|---|---|
| Segmentation | Limits spread | Complex setup | Firewalls, VLANs |
| Zero Trust | Continuous verification | Resource-intensive | MFA, RBAC |
| Patching | Fixes known flaws | Downtime risks in OT | Automated tools |
| Monitoring | Real-time alerts | False positives | SIEM systems |
Best Practices for Securing CPS Convergence
To stay ahead:
- Conduct Risk Assessments: Map interfaces and threats regularly.
- Train Teams: Bridge OT/IT knowledge gaps with cross-training.
- Incident Response Plans: Test plans for AI-driven scenarios.
- Secure Supply Chains: Vet vendors for CPS security.
From Dataminr’s guide, convergence requires hybrid threat mitigation external link.
Link to our /best-practices-cps-security for more tips.

Image credit: Gcore blog on AI-Powered Cyber Threats
Looking Ahead: Future Trends in CPS Security
The future? AI will both threaten and defend CPS. Trends include:
- AI-Enhanced Defenses: Predictive analytics to foresee sabotage.
- Quantum-Resistant Encryption: As AI cracks codes faster.
- Edge Security: Protecting data at the source in distributed CPS.
MarketsandMarkets predicts the CPS security market will hit $34 billion by 2030, driven by convergence needs.
For emerging trends, see /future-cps-trends.
Wrapping Up: Secure Your CPS Today
Cyber Physical Systems Convergence is here to stay, offering huge benefits but demanding strong defenses against AI-driven sabotage. By hardening OT/IT interfaces with segmentation, monitoring, and best practices, you can minimize risks. Start with an assessment, build a plan, and stay vigilant. Your operations—and safety—depend on it.
These developments point to a future where security isn’t an add-on but a core part of Cyber Physical Systems Convergence. Organizations that invest in AI-enhanced monitoring, strong segmentation, and continuous risk assessment will turn potential vulnerabilities into competitive strengths. They’ll achieve not only protection but also greater operational insight and faster recovery when incidents occur.
So, what should you do right now? Start small but think big:
- Assess your current state: Map out all OT/IT interfaces in your environment. Identify legacy systems, remote access points, and data flows. Tools for asset discovery and vulnerability scanning tailored to OT can reveal hidden risks.
- Implement foundational controls: Prioritize network segmentation (using firewalls, unidirectional gateways, or DMZs), multi-factor authentication everywhere possible, and strict access policies. These steps limit damage even if a breach occurs.
- Build monitoring capabilities: Deploy solutions that provide visibility into both IT and OT traffic. Look for platforms using AI/ML to baseline normal behavior and alert on anomalies—especially subtle ones that could indicate sabotage.
- Develop and test response plans: Create playbooks specifically for AI-driven or cyber-physical scenarios. Run tabletop exercises and simulations to ensure teams from IT, OT, and operations can coordinate effectively.
- Stay informed and adapt: Follow updates from trusted sources like CISA, NIST, or industry groups. Revisit your strategy regularly as new threats and technologies emerge.
- Foster a security culture: Train everyone involved—operators, engineers, managers—on the realities of converged threats. Encourage reporting of suspicious activity without fear.
The path isn’t always easy, especially with legacy equipment and tight production schedules. But delaying action only widens the gap between attackers’ capabilities and your defenses. By hardening those OT/IT interfaces today, you’re not just preventing sabotage—you’re safeguarding people, processes, and the future of your operations.
Cyber Physical Systems Convergence holds immense promise for smarter, more responsive industries. With thoughtful security built in from the start, it can deliver those benefits safely and reliably. The time to strengthen your defenses is now—before the next threat turns convergence from an advantage into a liability.
If you’re ready to dive deeper, check our related posts like /best-practices-cps-security or /future-cps-trends for more actionable guidance.
Share this content:













Post Comment