Continuous Threat Exposure Management (CTEM)
Cyber threats are everywhere. Businesses face constant risks from hackers looking to exploit weaknesses in their systems. That’s where Continuous Threat Exposure Management, or CTEM, comes in. It’s a smart way to stay ahead of these dangers by constantly checking and fixing potential problems. This approach helps reduce the attack surface in real time, meaning you shrink the areas where attackers can strike before they even try.
Imagine your company’s network as a big house with many doors and windows. Without proper locks or alarms, burglars could get in easily. CTEM is like having a security team that checks every entry point around the clock, fixes loose locks right away, and even predicts where thieves might target next. It’s not just about reacting to break-ins; it’s about preventing them altogether.
This blog post dives into everything you need to know about Continuous Threat Exposure Management. We’ll cover what it is, why it matters, how to put it into action, and tips for making it work in your setup. Whether you’re a small business owner or part of a large IT team, understanding CTEM can make a huge difference in keeping your data safe. Let’s explore how implementing real-time attack surface reduction through CTEM can protect your organization from evolving cyber risks.

Image credit: NordLayer – Illustration of attack surface elements.
What is Continuous Threat Exposure Management?
Continuous Threat Exposure Management is a framework designed to help organizations identify, assess, and reduce their exposure to cyber threats on an ongoing basis. Coined by Gartner in 2022, CTEM shifts the focus from traditional vulnerability patching to a more holistic, proactive strategy. It looks at the entire attack surface – that’s all the points where an unauthorized user could try to enter or extract data from your systems.
Unlike older methods that just scan for known vulnerabilities once in a while, CTEM keeps things running continuously. It combines tools, processes, and people to monitor risks in real time. This means you’re not waiting for the next quarterly audit; you’re addressing issues as they pop up. For example, if a new misconfiguration appears in your cloud setup, CTEM helps spot it immediately and prioritize fixing it based on how much damage it could cause.
At its core, Continuous Threat Exposure Management involves five key stages: scoping, discovery, prioritization, validation, and mobilization. These steps form a cycle that repeats, ensuring your security posture improves over time. Scoping defines what assets matter most, like critical servers or customer data. Discovery finds all potential exposures, from software bugs to weak passwords. Prioritization ranks these based on risk level – a vulnerability in a public-facing app might score higher than one in an internal tool. Validation tests if these risks are exploitable in the real world, often using simulated attacks. Finally, mobilization gets teams to fix them quickly.
Why does this matter? Cyber attacks are getting smarter and faster. Ransomware, phishing, and supply chain breaches are common headlines. By implementing CTEM, you reduce the chances of these hitting your business hard. It’s like having a weather radar for storms – you see them coming and prepare accordingly.
In simple terms, Continuous Threat Exposure Management turns cybersecurity from a checklist task into a dynamic process. It aligns security efforts with business goals, ensuring that the most important parts of your operation stay protected. If you’re dealing with hybrid work environments or cloud services, CTEM is especially useful because it handles the complexity of modern IT setups.
For more on the basics of cybersecurity frameworks, check out our internal guide on vulnerability management basics.
The Five Stages of Continuous Threat Exposure Management
To make Continuous Threat Exposure Management work, you follow a cycle of five stages. Each one builds on the last, creating a loop that keeps your defenses strong. Let’s break them down one by one.
Stage 1: Scoping
Scoping is the starting point. Here, you define the boundaries of your attack surface. What assets are critical? Think about hardware, software, cloud resources, and even third-party vendors. You map out everything that could be a target.
For instance, a retail company might scope their e-commerce platform, payment systems, and employee devices as high-priority. This stage involves working with business leaders to understand what’s valuable. Without good scoping, you might waste time on low-risk areas while ignoring big threats.
Tools like asset inventory software help here. They automatically catalog your environment, making scoping easier and more accurate.
Stage 2: Discovery
Once scoped, discovery kicks in. This is where you hunt for exposures. Exposures aren’t just vulnerabilities; they include misconfigurations, shadow IT (unauthorized apps), and identity issues like over-privileged accounts.
Automated scanners and monitoring tools play a big role. For example, using network discovery tools to find forgotten servers or open ports. In real time, this stage uses AI to detect anomalies, like unusual data flows that could signal a brewing attack.
Discovery ensures nothing slips through the cracks. It’s continuous, so as your environment changes – say, adding a new app – it’s immediately scanned.

Image credit: DataDome – Real-time threat dashboard showing bot attacks and origins.
Stage 3: Prioritization
Not all risks are equal. Prioritization sorts them by potential impact. You use factors like exploitability, asset value, and threat intelligence to score each exposure.
A high-severity CVE in a non-critical system might rank lower than a medium one in your core database. Tools integrate with threat feeds to update scores dynamically. This stage prevents overwhelm – your team focuses on what matters most, reducing the attack surface efficiently.
Stage 4: Validation
Validation tests if prioritized risks are truly exploitable. This often involves ethical hacking techniques, like penetration testing or breach simulations.
For real-time attack surface reduction, automated validation tools run safe exploits to confirm vulnerabilities. If a risk doesn’t hold up under testing, it drops in priority. This stage adds realism, ensuring you’re not chasing ghosts.
Stage 5: Mobilization
Finally, mobilization is about action. You assign fixes to teams, track progress, and verify resolutions. This could mean patching software, revoking access, or updating policies.
Mobilization ties back to scoping, restarting the cycle. It’s key for real-time reduction – quick fixes shrink the attack surface immediately.
By cycling through these stages, Continuous Threat Exposure Management keeps your organization resilient. For deeper insights into similar cycles, see our post on the cybersecurity lifecycle.
Why Real-Time Attack Surface Reduction Matters in CTEM
The attack surface is the sum of all possible entry points for attackers. It includes websites, APIs, emails, and more. As businesses grow, so does this surface – think remote work adding personal devices or cloud adoption exposing new endpoints.
Real-time attack surface reduction is a core part of Continuous Threat Exposure Management. It means shrinking that surface as threats emerge, not after a breach. Traditional methods might scan monthly, but real-time uses constant monitoring to detect and mitigate instantly.
Why is this important? Cyber threats evolve quickly. A new exploit can spread globally in hours. Real-time reduction buys time, limiting damage. For example, if a zero-day vulnerability hits, CTEM tools can isolate affected systems automatically.
Benefits include lower breach costs, better compliance (like GDPR or HIPAA), and peace of mind. Studies show organizations with proactive approaches suffer fewer incidents. In a world where data is gold, reducing exposure in real time protects your reputation and bottom line.
To learn more about attack surfaces, visit CrowdStrike’s guide on exposure management (dofollow link).
Implementing Continuous Threat Exposure Management Step by Step
Ready to implement Continuous Threat Exposure Management? Here’s a practical guide.
First, assess your current setup. Audit tools, processes, and team skills. Identify gaps – do you have visibility into all assets?
Next, choose technologies. Look for platforms that integrate scanning, prioritization, and automation. Popular ones include Tenable, Qualys, or open-source options like OpenVAS.
Build a team. Involve IT, security, and business stakeholders. Train them on CTEM principles.
Start small. Pilot in one department, like finance, before scaling.
Set metrics. Track things like mean time to remediation or exposure reduction percentage.
Integrate with existing workflows. Link CTEM to incident response plans.
For real-time aspects, use SIEM systems for alerts and orchestration tools for auto-fixes.
Challenges? Budget constraints or resistance to change. Overcome by showing ROI – fewer breaches mean savings.
Implementation takes time, but the payoff is a stronger, more adaptive security posture.

Image credit: Ammar Hasayen – Diagram of Attack Surface Reduction components in Microsoft Defender.
Tools and Technologies for Effective CTEM
No Continuous Threat Exposure Management program is complete without the right tools. Here’s a roundup.
Vulnerability scanners like Nessus detect weaknesses across networks.
Attack surface management tools, such as Cortex Xpanse, map external exposures.
For prioritization, risk scoring platforms use AI to weigh threats.
Validation needs BAS (Breach and Attack Simulation) tools like Cymulate.
Mobilization? Ticketing systems like Jira integrate with security ops.
Cloud-specific: AWS GuardDuty or Azure Sentinel for real-time monitoring.
Open-source alternatives: ZAP for web scanning, Metasploit for testing.
Choose based on your size and needs. Small businesses might start with free tools; enterprises need enterprise-grade integration.
For a full list, check Wiz’s academy on CTEM tools (dofollow link).
Case Studies: CTEM in Action
Real-world examples show Continuous Threat Exposure Management’s power.
A financial firm used CTEM to reduce exposures by 40% in six months. They scoped critical apps, discovered shadow IT, and validated with simulations, preventing a potential ransomware attack.
A healthcare provider implemented real-time monitoring, catching a phishing attempt early and mobilizing fixes within hours.
Tech giant Microsoft promotes CTEM-like features in Defender, helping users shrink attack surfaces dynamically.
These cases highlight how CTEM turns theory into results, saving money and headaches.
See our case study on healthcare cybersecurity for more.
Challenges in Adopting Continuous Threat Exposure Management
Despite benefits, challenges exist.
Data overload: Too many alerts can fatigue teams. Solution: Better prioritization.
Integration issues: Old systems don’t play nice with new tools. Start with compatible ones.
Skill gaps: Not everyone knows CTEM. Invest in training.
Cost: Tools aren’t cheap. But breaches cost more – average $4.45 million per IBM.
Cultural resistance: Shift from reactive to proactive takes buy-in.
Overcome by starting small, measuring success, and communicating wins.
Best Practices for Successful CTEM Implementation
To nail Continuous Threat Exposure Management:
Foster collaboration between teams.
Use automation wherever possible for real-time responses.
Stay updated with threat intelligence feeds.
Review and refine the cycle regularly.
Align with business risks, not just tech ones.
Document everything for audits.
These practices ensure CTEM delivers ongoing value.
For best practices in related areas, read our guide on threat intelligence.
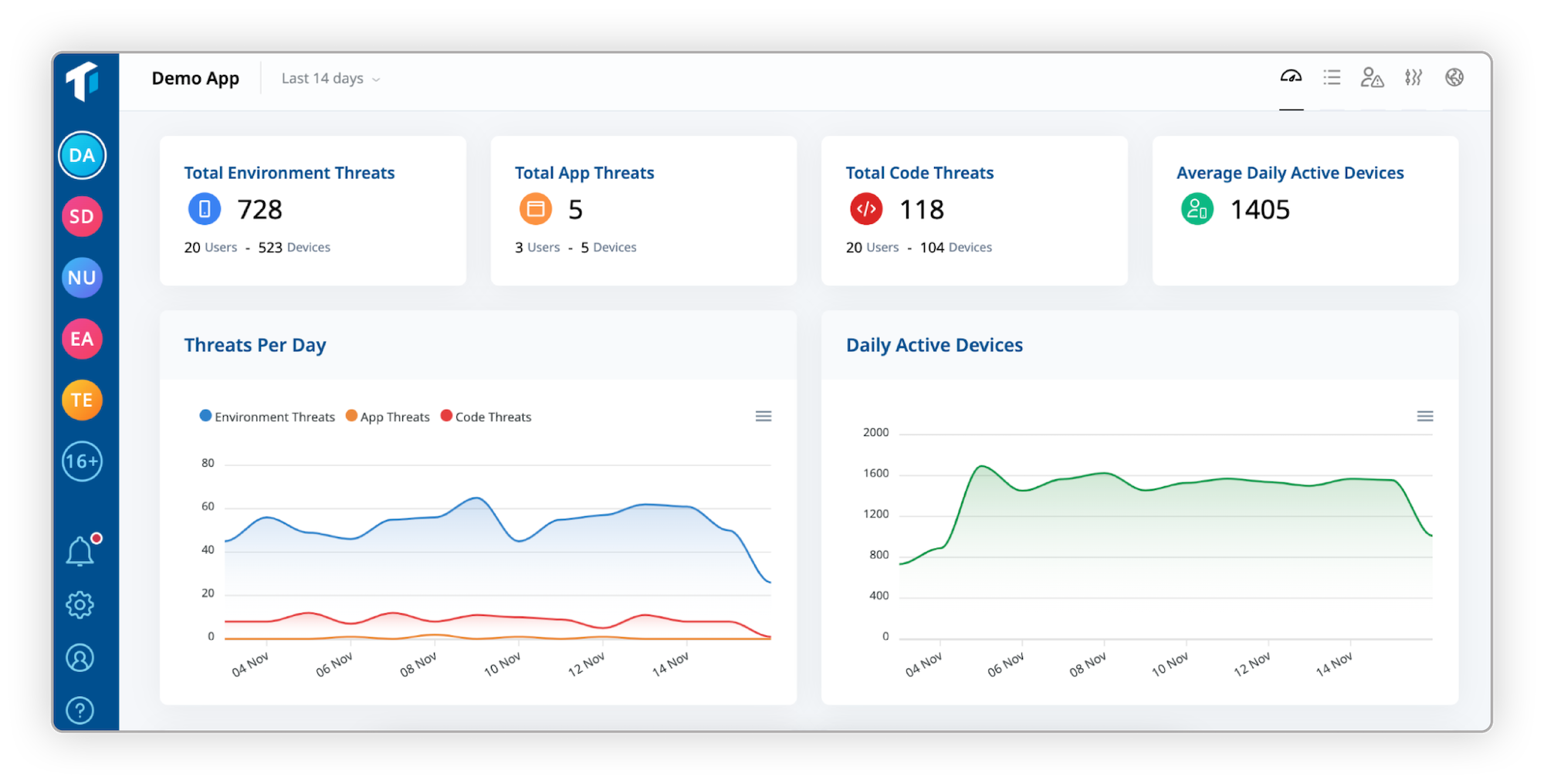
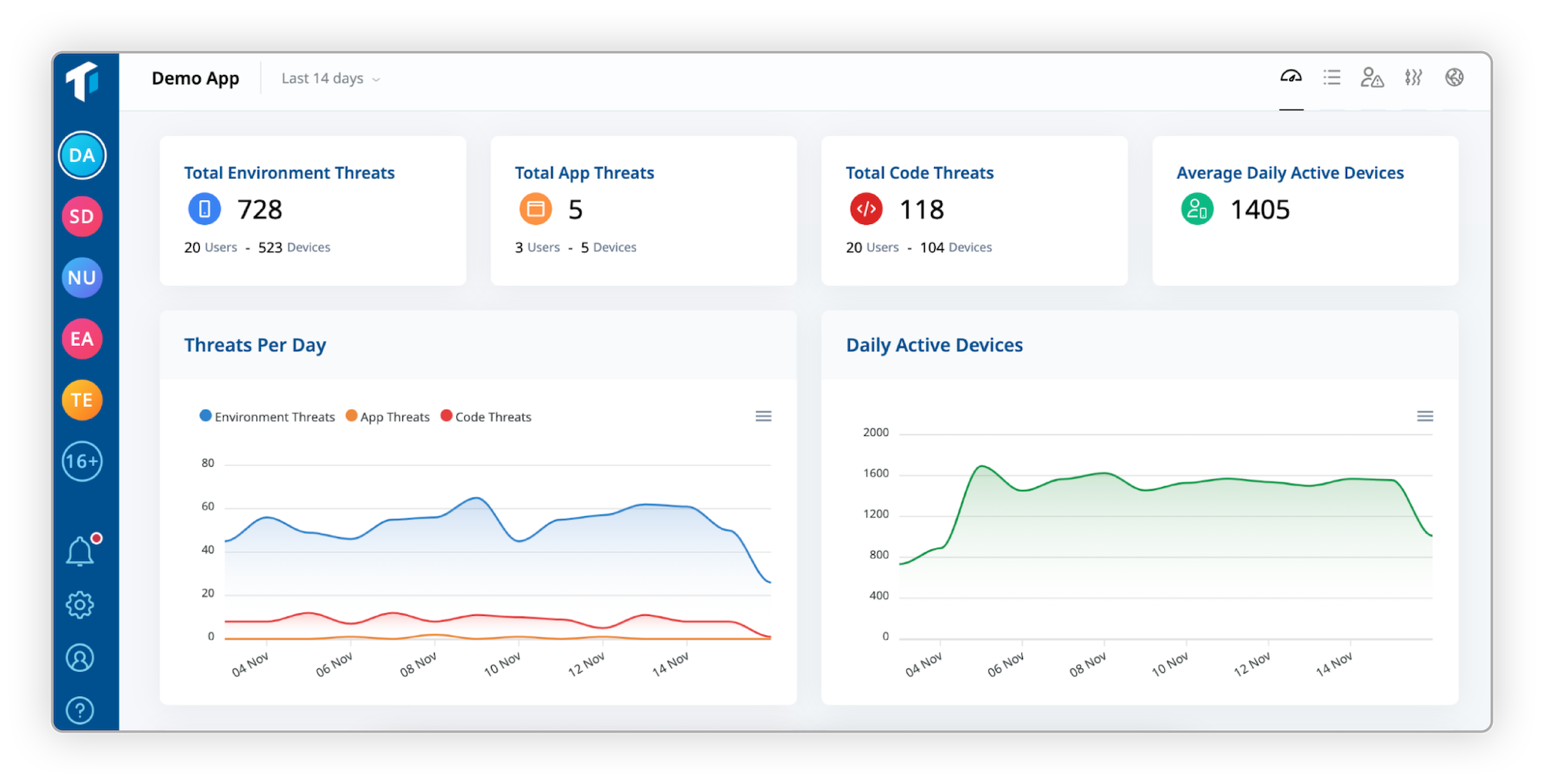
Image credit: Guardsquare – Threat monitoring dashboard for mobile apps.
Conclusion
Continuous Threat Exposure Management is a game-changer for cybersecurity. By implementing real-time attack surface reduction through its five stages, you can stay ahead of threats and protect what matters most. It’s not just tech; it’s a mindset shift to proactive defense.
Start assessing your needs today. With the right approach, CTEM can make your organization more secure and resilient. For expert advice, explore Gartner’s CTEM resources
Share this content:













Post Comment