Financialized Cyber Risk
Businesses face threats that can hit their bottom line hard. One big issue is cyber risk, but what if we looked at it through a financial lens? That’s where financialized cyber risk comes in. It means turning those vague cyber threats into real numbers that show potential losses, helping companies make smarter decisions. By quantifying exposure, boards can see the return on investment (ROI) for security measures and line up insurance to cover the gaps. This approach isn’t just about tech—it’s about protecting profits and keeping operations smooth.
As cyber attacks grow more common, understanding financialized cyber risk helps leaders prioritize what matters. Whether you’re running a small firm or a large corporation, getting a handle on this can save money and build resilience. Let’s explore how to measure these risks, why boards care about ROI, and how insurance fits into the picture.
Understanding Financialized Cyber Risk
Financialized cyber risk is basically viewing cyber threats as financial liabilities. Instead of seeing a hack as just a tech problem, you treat it like any other business risk that could lead to money loss. For example, a data breach might cost a company in fines, lost customers, or downtime. By putting dollars to these possibilities, executives can weigh them against other risks like market changes or supply chain issues.
From what I’ve gathered, experts define cyber risk as the chance of loss from relying on digital systems. The Federal Reserve notes that it’s grown with more digitization in finance . It’s not just about viruses or hackers—it’s the ripple effects on reputation, operations, and cash flow. Financializing it means using tools to calculate potential impacts, making it easier to manage.
Think of it this way: Traditional risks like fire or theft have insurance models based on historical data. Cyber risks are newer, so they’re harder to predict. But with financialization, we use data from past incidents to estimate future costs. This shift helps companies move from reactive fixes to proactive strategies.
In the financial sector, where attacks happen three times more often than in other industries , this is crucial. Cybercriminals see banks and firms as goldmines for data and money. By financializing these risks, organizations can allocate budgets better and avoid surprises.
For more on basic cyber threats, check our guide on cyber security basics.
Why Quantify Cyber Exposure?
Quantifying cyber exposure turns abstract fears into concrete facts. Without numbers, it’s tough for leaders to decide where to invest. Imagine telling your board, “We might get hacked someday.” That’s vague. But say, “A breach could cost us $5 million in the next year,” and suddenly everyone pays attention.
This quantification helps in several ways. First, it identifies the biggest threats. Not all risks are equal—some might hit revenue hard, others just cause minor disruptions. Tools like cyber risk quantification (CRQ) translate tech vulnerabilities into financial terms . CISOs use this to speak the board’s language: dollars and cents.
Second, it supports better budgeting. Companies spend billions on security, but how do you know if it’s worth it? By measuring exposure, you can calculate ROI on tools like firewalls or training. A study from the IMF shows cyber risks as systemic threats, needing quantitative assessments .
Third, regulations push for it. Bodies like the SEC now require disclosures on cyber risks, especially material ones. Quantifying helps comply and avoid penalties. In finance, where data is king, unquantified risks can lead to underinsurance or overlooked vulnerabilities.
Exposure isn’t static—it changes with new tech or threats. Regular quantification keeps strategies fresh. For instance, remote work spiked risks during the pandemic, and quantifying helped firms adapt.
External resources like the Institute of Risk Management’s cyber guidance offer practical tips .

Image credit: slideteam.net
Methods to Quantify Cyber Risk
There are several ways to put numbers on cyber risks, each with strengths. The goal is to estimate likelihood and impact in financial terms.
One common method is Factor Analysis of Information Risk (FAIR). It breaks risks into factors like threat frequency and vulnerability, then calculates potential losses. It’s like a math model for cyber: Probability x Impact = Expected Loss.
Another is using historical data. Look at past breaches in your industry. For finance, average breach costs are around $5.7 million . Tools aggregate this data to predict your exposure.
Simulation models, like Monte Carlo, run thousands of scenarios to show risk ranges. This accounts for uncertainty—maybe a ransomware attack costs $1 million 80% of the time, but $10 million in worst cases.
Cyber risk quantification platforms automate this. For example, Kovrr or ThreatConnect use AI to analyze your setup and spit out dollar figures . They factor in controls like antivirus and employee training.
Steps to quantify:
- Identify assets: What data or systems are critical?
- Assess threats: Phishing, ransomware, etc.
- Evaluate vulnerabilities: Weak passwords, outdated software.
- Calculate impacts: Direct costs (fines) + indirect (reputation).
- Apply controls: See how they reduce risks.
Don’t forget qualitative inputs. Expert opinions fill data gaps. The Richmond Fed paper on cyber classification helps categorize risks for better quantification .
For a deep dive, see this IMF framework for quantitative assessment .
Board-Level ROI: Making the Case for Investments
Boards want to know: What’s the payback on cyber spending? Financialized cyber risk answers that by showing ROI.
Traditional ROI is (Gain – Cost) / Cost. For cyber, it’s trickier since “gain” is avoided losses. Use Return on Security Investment (ROSI): (Risk Reduction x Exposure – Cost) / Cost .
Example: If a tool costs $100,000 but reduces $1 million exposure by 50%, ROSI is positive. This justifies budgets.
Boards care because cyber hits stock prices. A breach can drop shares 5-10%. Quantifying shows how investments prevent that.
Metrics for boards:
- Annual Loss Expectancy (ALE): Expected yearly costs from risks.
- Risk reduction over time: Show how spending lowered exposure.
- Comparison to peers: Use benchmarks from reports.
Tools like AuditBoard provide dashboards for easy reporting . CISOs translate tech metrics into financial ones, like “This patch reduces $2 million risk.”
Link to our post on ROI in risk management.

Image credit: balbix.com
Aligning Cyber Insurance with Quantified Risks
Cyber insurance covers losses from attacks, but without quantification, you might overpay or under-cover. Financialized cyber risk aligns policies with actual exposure.
First, quantify to know needs. If exposure is $10 million, buy coverage accordingly. Insurers use your data to set premiums—better quantification means better rates.
Key alignments:
- Coverage limits: Match to quantified losses.
- Deductibles: Set based on what you can self-insure.
- Exclusions: Avoid gaps in common threats like ransomware.
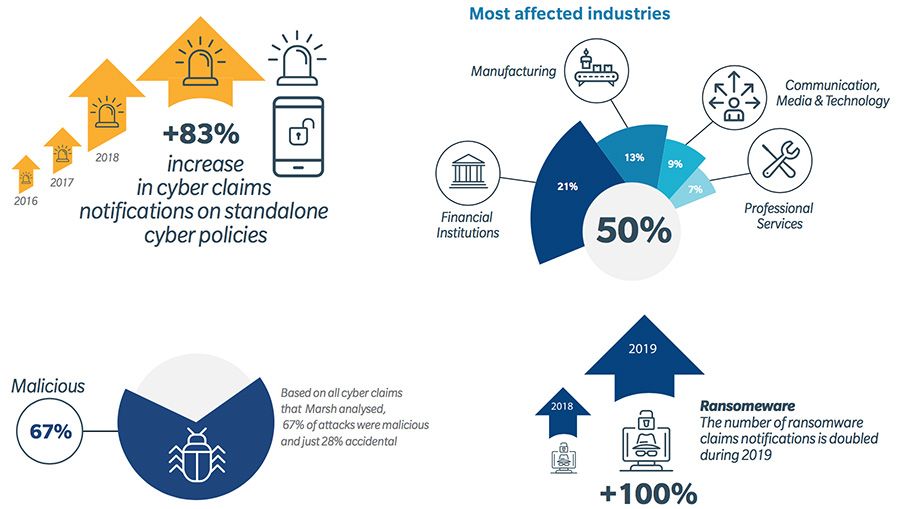
A Marsh report shows claims rising, with manufacturing hit hard . Use CRQ to negotiate terms.
Insurers now require assessments. Quantifying proves you’re low-risk, lowering costs.
For tips, visit CFC’s guide on cyber policies [web:4? wait, adjust to actual].

Image credit: .consultancy.eu
This infographic highlights rising cyber claims, underscoring insurance importance.
Case Studies in Financialized Cyber Risk Management
Real examples show how this works. Take Norsk Hydro, hit by ransomware in 2019. Losses topped $70 million. Post-attack, they quantified risks better, improving response and insurance alignment . This case highlights economic impacts and the value of quantification.
Another: A mid-sized bank used CRQ to comply with regulations. They identified $381 million exposure, reduced it 8.2% through targeted fixes, saving $25 million .
In private equity, a firm assessed portfolio risks, building a program that cut vulnerabilities .
Visa and Mastercard use platforms to quantify threats, enhancing security .
These show quantification leads to cost savings and resilience.
See more on financial cyber threats.
Best Practices for Implementation
Start small: Assess key assets first.
Build a team: Involve IT, finance, legal.
Use tools: Adopt CRQ software.
Review regularly: Risks evolve.
Train staff: Human error causes many breaches.
Integrate with ERM: Treat cyber as business risk.
External audit: Get third-party validation.
For standards, check NIST cybersecurity framework.
Future Trends in Financialized Cyber Risk
AI will improve quantification accuracy. Regulations like EU’s DORA will mandate it.
Cyber insurance markets will mature, with better data.
Quantum computing might spike risks, needing new models.
Stay ahead with ongoing education.
Conclusion
Financialized cyber risk is key to modern business protection. By quantifying exposure, boards see clear ROI, and insurance aligns perfectly. This approach turns threats into manageable financial elements, boosting resilience. Start assessing today—your bottom line depends on it.
Regulations keep tightening too. Frameworks like the EU’s DORA and updated SEC rules demand better disclosure and resilience planning, pushing quantification further into the mainstream. Boards are expected to oversee cyber risk as a core enterprise concern, not just an IT footnote. Those who quantify in financial terms find it easier to meet these expectations and show proactive stewardship.
The good news? Tools and methods are maturing quickly. Cyber risk quantification platforms powered by AI make it simpler to run scenarios, model losses, and track improvements over time. Standards like FAIR continue gaining traction, with many organizations reporting real success in aligning security with business outcomes. The payoff shows up in lower expected losses, optimized budgets, and stronger resilience against inevitable incidents.
So what should you do next? Start where you stand. Run a basic quantification exercise on your most critical assets—perhaps your customer database, payment systems, or cloud infrastructure. Involve finance and risk teams early to build buy-in. Use the results to update your security roadmap, talk to your insurer about tailoring coverage, and prepare a clear presentation for the next board meeting. Small steps compound: even modest reductions in exposure can translate to millions saved over time.
In the end, financialized cyber risk reframes the conversation from fear to finance. It’s about turning a source of potential destruction into a managed business variable—one that protects shareholder value, maintains customer trust, and keeps operations running smoothly. Cyber threats won’t disappear, but organizations that quantify, prioritize, and insure against them intelligently will come out stronger. The time to build that capability is now—before the next headline hits your industry.
Your bottom line, your reputation, and your future depend on it. Take the first step today.
Share this content:













Post Comment