Machine Identity Explosion
Businesses are moving faster than ever, relying on clouds, automation, and smart tech to get things done. But with all this progress comes a hidden challenge: the massive growth of machine identities (Machine Identity Explosion). These aren’t people logging in with usernames and passwords; they’re the behind-the-scenes players like apps, bots, and devices that keep everything running. This surge, often called the machine identity explosion, is hitting hybrid cloud setups hard, where on-prem systems mix with public and private clouds. If not handled right, it can lead to security gaps, compliance headaches, and even costly breaches.
Hybrid clouds offer the best of both worlds—flexibility from the cloud and control from on-site infrastructure. Yet, managing non-human identities (NHIs) at scale here is tricky. NHIs include service accounts, API keys, IoT devices, and AI agents, and they’re multiplying quickly. According to recent studies, they now outnumber human identities by ratios as high as 82:1 in some organizations. This post dives into what this explosion means, the hurdles it creates, and practical ways to tackle it. Whether you’re a IT manager in Jamshedpur or anywhere else, understanding this can help secure your setup without slowing down operations.
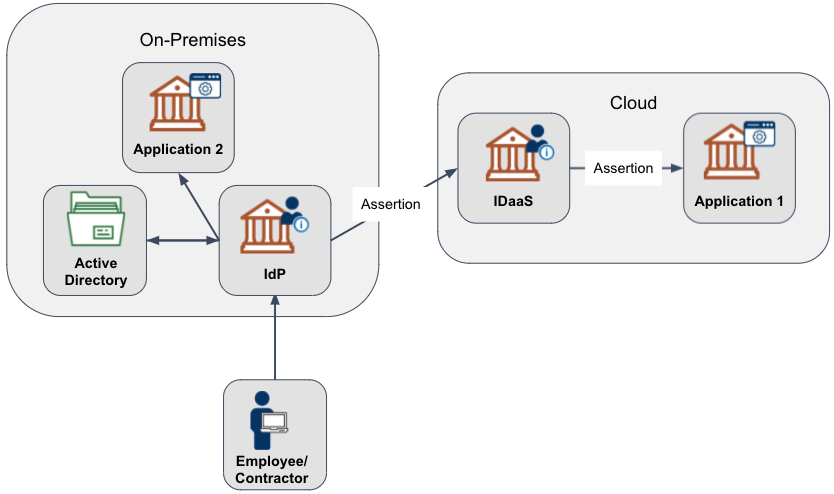
Image credit: IDManagement.gov – Diagram showing hybrid cloud identity management with on-premises and cloud components.
What is Machine Identity Explosion?
Let’s break it down simply. Machine identities are the digital IDs used by non-human entities to access resources. Think of them as passports for machines—they prove who (or what) is knocking on the door. The “explosion” refers to how these identities are growing out of control, driven by cloud adoption, microservices, and automation.
In hybrid clouds, this growth is even more pronounced. You have traditional servers on-site talking to cloud services like AWS or Azure. Each connection might need its own identity, like an API key or certificate. As businesses add more apps and devices, the number balloons. For example, a single microservice deployment can create dozens of new identities overnight.
Why does this matter? Unlike human users who might log in once a day, machines operate 24/7, often with high privileges. If one gets compromised, attackers can move laterally across your network. Reports show that NHIs are involved in a growing number of breaches because they’re often overlooked. Tools like secrets managers help, but the sheer volume demands better strategies.
To put it in perspective, consider a typical enterprise: A few years ago, you might have had 50,000 machine identities. Now, with DevOps pipelines and AI, that could jump to 500,000. That’s the explosion in action.
The Rise of Non-Human Identities in Hybrid Clouds
Hybrid clouds are popular because they let companies keep sensitive data on-prem while using cloud scalability for other tasks. But this setup breeds NHIs. Here’s why they’re rising:
First, cloud migration. When you move apps to the cloud, you create new identities for workloads, containers, and serverless functions. In a hybrid model, these interact with on-prem systems, multiplying connections.
Second, automation and AI. Tools like CI/CD pipelines generate temporary credentials automatically. AI agents, which are becoming common, need their own IDs to access data. Add IoT devices in manufacturing or healthcare, and you’ve got a web of identities.
Third, microservices architecture. Instead of monolithic apps, everything’s broken into small services, each with its own identity. In hybrid environments, this spans multiple providers, like AWS for storage and Azure for compute.
Statistics back this up: NHIs outnumber humans 20-100:1, depending on the industry. And with AI adoption, expect another 150% growth soon.
For more on cloud basics, check our internal guide to cloud security fundamentals.

Image credit: Software Analyst Cyber Research – Ecosystem of non-human identities including IAM, governance, and infrastructure layers.
Challenges in Managing Machine Identities
Managing this explosion isn’t easy. Hybrid clouds add layers of complexity. Here are the main hurdles:
- Visibility Issues: Many NHIs are created automatically and go undocumented. In hybrid setups, they’re scattered across on-prem directories like Active Directory and cloud providers. Without full visibility, you can’t secure them.
- Lifecycle Management: Machines have short lifespans—think ephemeral containers that last minutes. Rotating credentials or decommissioning old ones manually is impossible at scale.
- Over-Privileging: NHIs often get more access than needed, following the principle of least privilege in theory but not practice. This creates blast radii if compromised.
- Hybrid Complexity: Different environments use different tools. On-prem might rely on AD, while clouds have their own IAM systems. Syncing them leads to inconsistencies and security gaps.
- Compliance and Audits: Regulations like GDPR or HIPAA require tracking access. With exploding NHIs, proving who accessed what becomes a nightmare.
- Skill Gaps: Teams trained on human IAM struggle with machine-scale issues. Plus, developers create identities without security input, leading to shadow IT.
Real-world examples show the risks: The SolarWinds breach exploited machine identities to spread malware. In hybrid clouds, such incidents can cascade quickly.
For tips on overcoming IAM challenges, see our post on IAM best practices.

Image credit: Bacancy Technology – Diagram of hybrid cloud security challenges like data leakage and poorly defined SLAs.
Best Practices for Managing Non-Human Identities
Don’t panic—there are ways to tame this beast. Focus on a unified approach that covers discovery, governance, and protection.
- Implement Zero Trust for All Identities: Treat every access request as untrusted, whether human or machine. Use continuous verification and micro-segmentation to limit damage.
- Automate Discovery and Inventory: Use tools to scan environments continuously. Assign ownership to every NHI—tie them to teams or apps for accountability.
- Enforce Least Privilege: Scope permissions tightly. Review and adjust regularly with automation to prevent privilege creep.
- Rotate Secrets Automatically: Use vaults to manage keys and certificates. Rotate them often to reduce exposure.
- Monitor Behavior: Set baselines for normal activity. Use AI to detect anomalies, like a bot accessing unusual data.
- Unify Governance Across Hybrid Environments: Adopt platforms that work across clouds and on-prem. This ensures consistent policies.
- Integrate with DevOps: Make security part of pipelines. Use IaC to provision identities securely from the start.
- Conduct Regular Audits and Drills: Test your setup with simulations. Ensure compliance through automated reporting.
Following these can cut risks by up to 90% in some cases. For external resources, check CyberArk’s guide on machine identity security.

Image credit: Software Analyst Substack – Wheel diagram of cloud-native identity management platform stages.
Tools and Technologies for Machine Identity Management
You can’t do this manually—tools are key. Here’s a roundup:
- Identity Governance Platforms: SailPoint or Saviynt for managing lifecycles across hybrid setups.
- Secrets Managers: HashiCorp Vault or CyberArk for storing and rotating credentials.
- Cloud IAM Tools: AWS IAM, Azure AD, or Google Cloud IAM for provider-specific control, but unify them.
- NHI-Specific Platforms: Entro or Axonius for discovery and behavior analysis.
- Certificate Managers: Venafi (now CyberArk) or AppViewX for handling TLS/SSL at scale.
- ITDR Solutions: CrowdStrike or Silverfort for threat detection focused on identities.
Choose based on your hybrid needs. For example, BeyondTrust integrates PAM with machine management. Explore Okta’s workforce identity cloud for seamless integration.
Our tool comparison post has more details.

Image credit: Sprinto.com – Components of hybrid cloud security including user authentication and SIEM.
Case Studies: Real-World Wins and Lessons
Learning from others helps. Here are examples:
- Netflix’s SPIFFE/SPIRE Framework: They use open-source standards for microservices authentication. This cut security incidents by 60% in their hybrid cloud.
- Financial Firm’s AI Agent Breach: An attacker used stolen credentials to query an AI for data. Lesson: Secure NHIs with MFA and monitoring.
- SolarWinds Attack: Misused certificates spread malware to thousands. Post-incident, companies adopted automated certificate management.
- Microsoft Teams Outage: Expired certificate downed services. Now, automation prevents such lapses.
These show that proactive management pays off. In one study, proper NHIM reduced exposure by 90%.
For more stories, read Cloud Security Alliance’s NHI survey report.
Future Trends in Machine Identity Management
Looking ahead, things will evolve. AI will play a bigger role in predicting risks and automating governance. Quantum threats mean shifting to post-quantum crypto.
Expect more agentic AI, where systems self-manage identities. Decentralized identities using blockchain could add traceability.
Non-human focus will dominate IAM, with tools blending human and machine management. Passwordless auth will extend to machines.
Stay ahead by following trends from KuppingerCole’s identity innovations.

Image credit: Device Authority – AI brain with circuits illustrating machine identity management transformation.
Conclusion
The machine identity explosion is real, especially in hybrid clouds where NHIs scale rapidly. But with the right practices—zero trust, automation, and unified tools—you can manage them effectively. This not only boosts security but also supports business growth.
Start by assessing your current setup: Inventory NHIs, tighten privileges, and invest in tools. Remember, ignoring this can lead to breaches, but mastering it turns a challenge into a strength.
the machine identity explosion is reshaping how we think about security in hybrid clouds. Ignore it, and you risk blind spots that could lead to major incidents. Embrace it with unified visibility, automation, least privilege, and continuous monitoring, and you build a resilient foundation that supports growth, AI adoption, and innovation without constant fear of compromise.
If you’re just starting, begin small: inventory your NHIs this quarter, pilot tighter controls on high-risk ones, and evaluate unified platforms. The payoff is worth it—stronger security, fewer surprises, and the confidence to scale confidently in this machine-first world.
For more practical guidance, revisit our earlier sections on best practices or tools. You can also explore resources like CyberArk’s insights on AI agents and identity risks or the Cloud Security Alliance’s State of Non-Human Identity report.
Stay ahead of the explosion—your future self (and your organization) will thank you.
Share this content:














Post Comment