Triple Extortion Ransomware Evolution
In today’s digital world, cyber threats are everywhere, and one of the scariest ones is ransomware. You’ve probably heard stories about companies getting hit hard, losing access to their files and facing huge demands for money. But things have gotten even more complicated with something called triple extortion ransomware Evolution. This isn’t just about locking up your data anymore—it’s a multi-layered attack that can ruin reputations, disrupt operations, and even target people connected to the victim.
The evolution of ransomware from simple encryption schemes to these advanced extortion tactics shows how cybercriminals are always one step ahead. They started with basic demands, moved to stealing data, and now they’re adding extra pressure like denial-of-service attacks or harassing third parties. If you’re running a business or just handling personal data, understanding this shift is crucial. That’s why we’re diving into the triple extortion ransomware evolution, and more importantly, how to protect your backups and ensure data provenance to stay safe.
Backups used to be the go-to savior against ransomware, but attackers now target them too. Data provenance, which tracks where your data comes from and how it’s been handled, adds another layer of defense by helping spot tampering early. In this post, we’ll break it all down step by step, from the history to practical tips. By the end, you’ll have a clear plan to safeguard your systems.
What is Ransomware and Why Should You Care?
Ransomware is malicious software that sneaks into your computer or network and encrypts your files, making them unusable until you pay a ransom—usually in cryptocurrency like Bitcoin. It’s like a digital kidnapper holding your data hostage. The first known case popped up back in 1989 with the AIDS Trojan, which locked files on floppy disks and demanded payment via mail. But ransomware didn’t become a massive problem until the 2010s, when better encryption and anonymous payments made it profitable for hackers.
Why care? Because it’s not just big corporations getting hit. Small businesses, hospitals, schools, and even individuals are targets. In 2025, experts reported that ransomware attacks cost the global economy over $20 billion annually, with average downtime lasting weeks. Attackers use phishing emails, exploit software vulnerabilities, or even buy access from initial access brokers on the dark web.
The basic goal is extortion: pay up or lose your data forever. But as defenses improved—like better antivirus and backups—hackers adapted. They realized encryption alone wasn’t enough if victims could just restore from backups. That’s where the evolution kicks in, leading to more sophisticated methods.
If you’re new to this, think of ransomware as a virus that spreads quietly. It might sit dormant for days, mapping your network before striking. Common signs include files with weird extensions like .locked or ransom notes popping up on your desktop. Ignoring it isn’t an option; it can lead to data leaks, legal issues, and financial ruin.
For more on the basics, check out our guide on what is ransomware to get a fuller picture.
The Evolution of Ransomware Attacks
Ransomware has come a long way since its early days. It started simple but grew into a professional criminal enterprise. Let’s trace that path.
Single Extortion: The Early Days
In the beginning, ransomware was all about encryption. Hackers would infect a system, lock the files, and demand payment for the decryption key. This is single extortion. The 2005 GPCode malware was an early example, using weak encryption that was easy to crack. But by 2013, CryptoLocker upped the game with strong AES encryption and Bitcoin payments, infecting hundreds of thousands and raking in millions.
Victims had a choice: pay or lose data. Many paid because backups weren’t common back then. But as people got smarter about backing up, single extortion lost its edge. Organizations could restore files without paying, frustrating attackers.
Double Extortion: Adding Data Theft
Around 2019, groups like Maze introduced double extortion. They didn’t just encrypt—they stole sensitive data first. If you didn’t pay, they’d threaten to leak it on the dark web or sell it to competitors. This hit confidentiality hard, as even restoring from backups wouldn’t stop the leak.
Double extortion became the norm. In 96% of cases investigated by security firms, data was exfiltrated alongside encryption. It added reputational damage, legal fines from data breaches, and more pressure to pay. Ransomware-as-a-Service (RaaS) models made it easier for affiliates to join in, spreading the tactic wide.
Triple Extortion: The New Threat Landscape
Now we’re at triple extortion, where attackers layer on a third tactic. Beyond encryption and data theft, they might launch DDoS attacks to knock systems offline, contact customers directly with threats, or harass employees. The first big case was in 2020 with a Finnish psychotherapy firm, where hackers emailed patients demanding personal payments after stealing records.
This evolution shows hackers targeting the full CIA triad: confidentiality (data leaks), integrity (tampering with systems), and availability (DDoS or encryption). Groups like REvil and Conti pioneered this, making attacks more devastating. In triple extortion, the ransom isn’t just for decryption—it’s to avoid broader chaos.
Why the shift? Better defenses forced it. With immutable backups and zero-trust security, hackers need multiple levers to force payment. Triple extortion ransomware evolution has turned it into a full extortion business, not just malware.
Here’s a quick timeline of key milestones:
- 1989: AIDS Trojan – First ransomware.
- 2013: CryptoLocker – Phishing-spread encryption.
- 2017: WannaCry – Global worm affecting millions.
- 2019: Maze – Introduces data exfiltration.
- 2020: Triple extortion emerges with third-party targeting.
This progression highlights how cybercriminals adapt. For a deeper look, see this evolution overview from Fortinet.
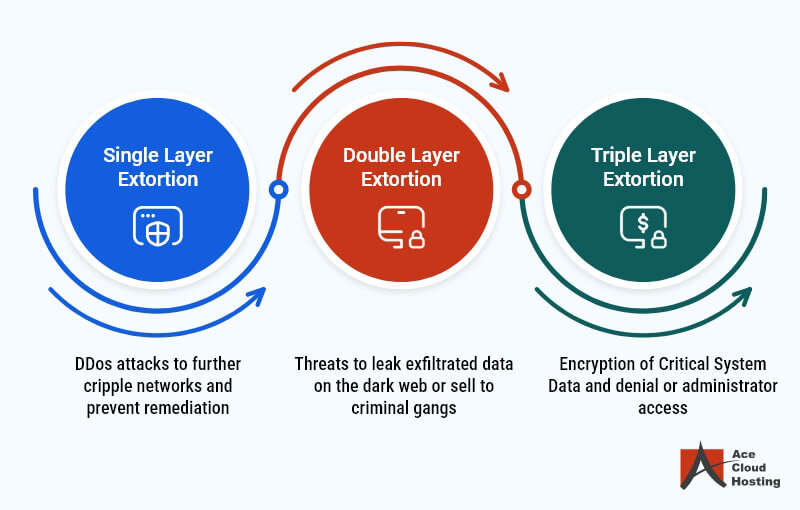
Credit: Ace Cloud Hosting via acecloudhosting.com
What is Triple Extortion Ransomware?
Triple extortion ransomware takes the pain to another level. In a standard attack, hackers infiltrate via phishing or vulnerabilities, encrypt files, steal data, and then add a third element like DDoS or direct threats to associates.
How it works: First, encryption locks your systems (availability hit). Second, data exfiltration threatens leaks (confidentiality). Third, something extra—like overwhelming your website with traffic or emailing clients saying their data is at risk unless you pay.
Examples include Avaddon, which combined encryption, leaks, and DDoS, or Clop, which contacted victims’ partners. It’s ruthless because even if you restore backups, the third layer keeps the pressure on.
The mechanics involve tools like Cobalt Strike for persistence, exfiltration via cloud services, and bots for DDoS. Attackers often disable backups first, making recovery harder.
This tactic is part of multi-extortion trends, sometimes escalating to quadruple with media harassment. It’s why triple extortion ransomware evolution is so alarming—it’s not just tech; it’s psychological warfare.
For prevention basics, our ransomware prevention guide has more details.
Real-World Examples of Triple Extortion
Let’s look at some cases to see the damage.
The 2020 Vastaamo attack in Finland: Hackers stole patient records from a therapy center, encrypted systems, and then emailed patients demanding €200 each not to leak their sessions. The company faced bankruptcy, and the CEO was charged for poor security.
In 2021, REvil hit a supply chain firm, encrypting data, stealing files, and launching DDoS on their sites until payment. They demanded millions, and leaks included customer info.
More recently, in 2025, groups like LockBit 3.0 used triple tactics against healthcare providers, threatening to contact patients directly if ransoms weren’t paid.
These show how triple extortion hits beyond the victim, affecting ecosystems. Lessons? Patch vulnerabilities fast and segment networks.
The Impact of Triple Extortion on Businesses and Individuals
The fallout is huge. Businesses face downtime costing $8,500 per minute on average, plus ransom payments averaging $1.8 million. Leaks lead to lawsuits, fines under GDPR or CCPA, and lost trust.
For individuals, if personal data is involved—like in healthcare—it’s identity theft risk or emotional distress. Small businesses might close; 60% shut down within six months of an attack.
Reputational damage is long-term. Customers flee, stocks drop (public companies lose 8% value post-breach). And with third-party targeting, it ripples out.
On a positive note, strong defenses can mitigate this. Read about cyber insurance options to buffer financial hits.
Protecting Your Backups from Triple Extortion Ransomware
Backups are your lifeline, but attackers know that. In 98% of attacks, they try to delete or encrypt backups. So, how do you protect them?
Follow the 3-2-1-1-0 rule: 3 copies of data, on 2 different media, 1 offsite, 1 immutable, 0 errors in testing.
Immutable backups can’t be changed or deleted for a set time—use WORM (Write Once, Read Many) storage. Air-gapped backups are offline, unreachable by networks.
Test restores regularly; CISA recommends quarterly drills. Use encryption on backups and multi-factor authentication for access.
Segment backups from main networks, and monitor for anomalies. Tools like Veeam offer ransomware detection in backups.
If using cloud, ensure providers follow zero-trust and have recovery SLAs. For more, see Microsoft’s Azure backup guide.
Don’t forget: Backups alone aren’t enough against triple extortion, as data leaks persist. Combine with other defenses.

Credit: NordLayer via nordlayer.com
Our backup best practices post dives deeper.
The Role of Data Provenance in Cybersecurity
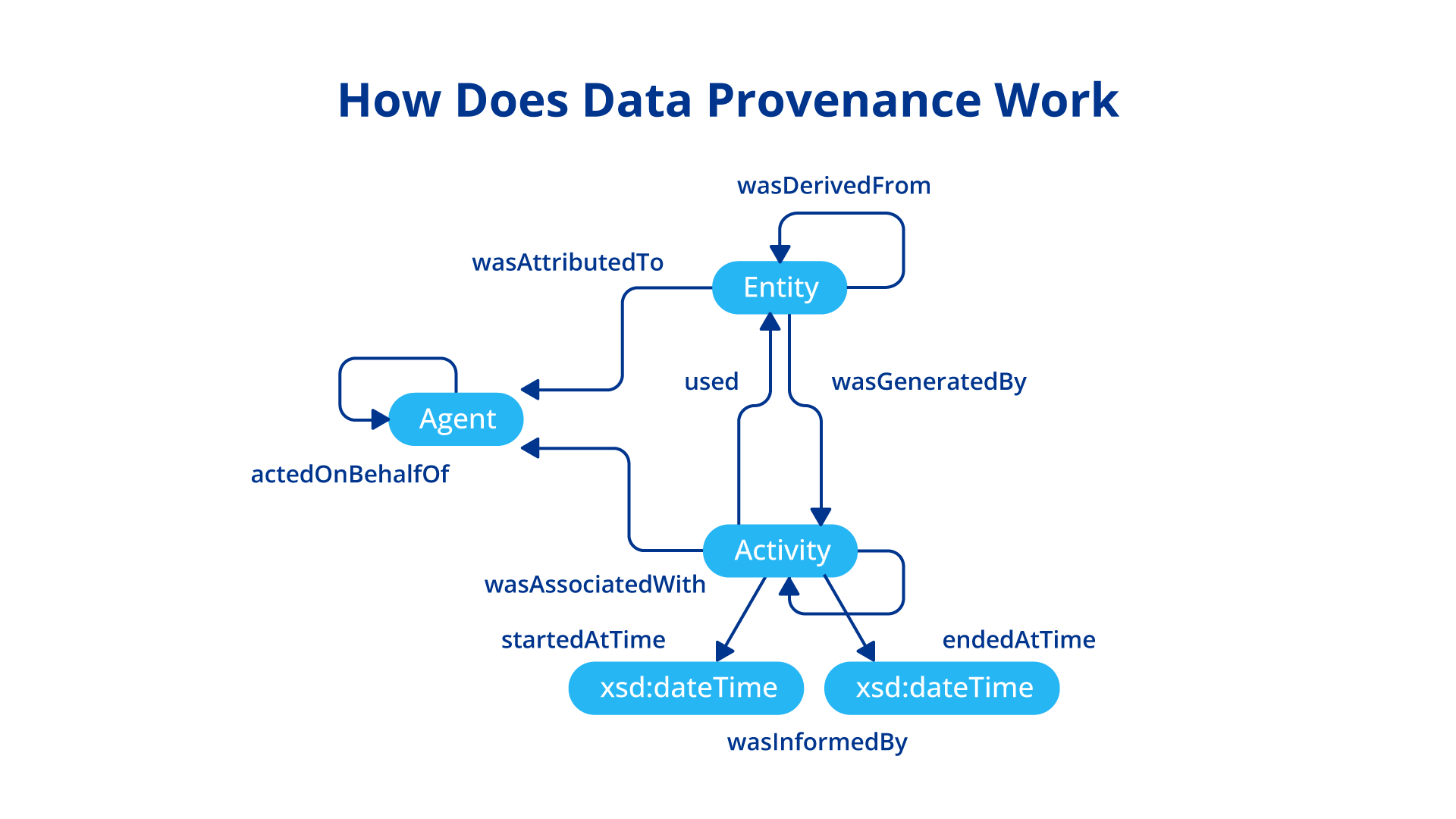
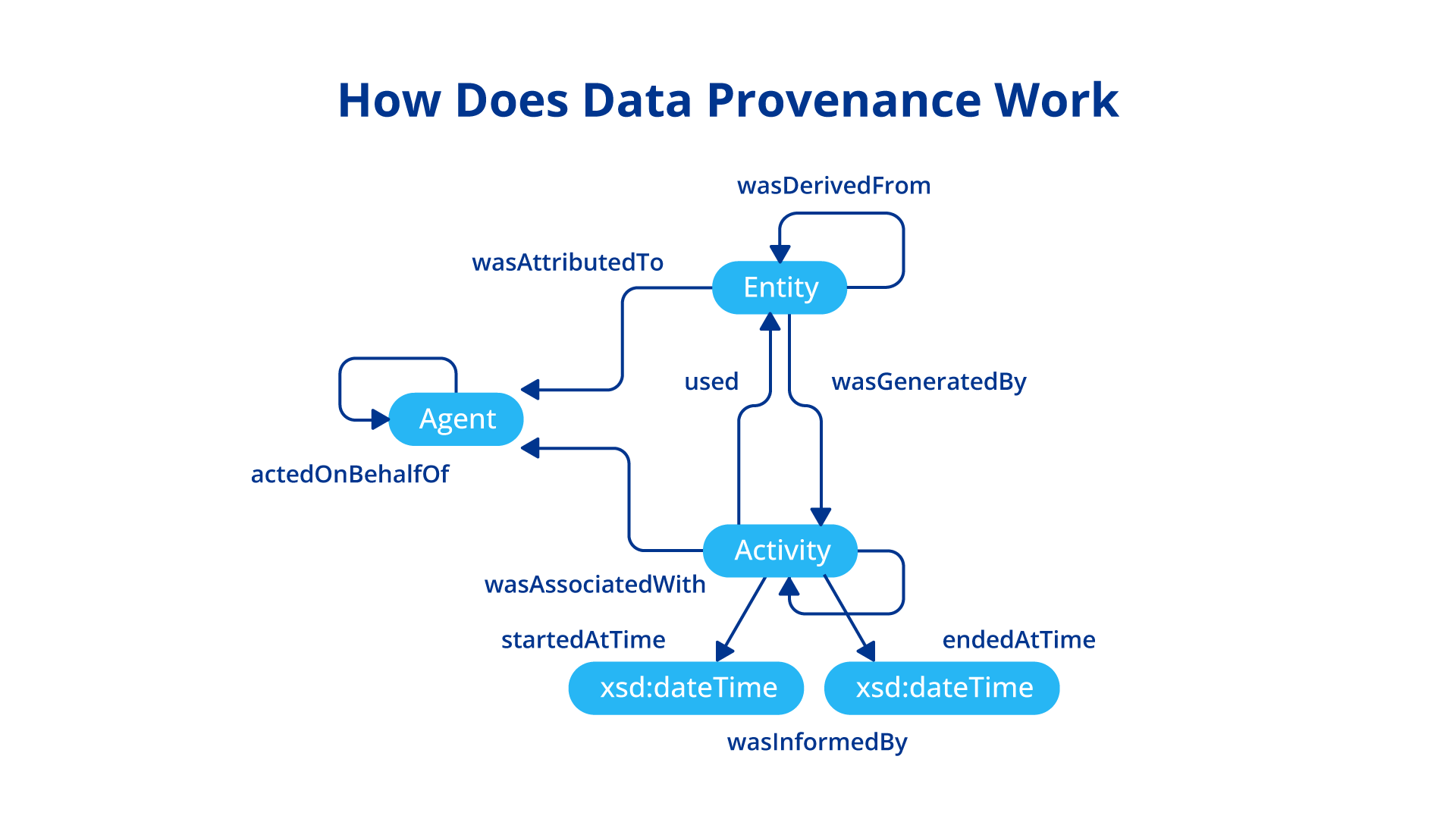
Data provenance is like a digital chain of custody. It records a dataset’s origin, changes, and handling—who touched it, when, and how. In cybersecurity, it’s key for spotting tampering or breaches.
For ransomware, provenance helps trace how attackers accessed data, identifying entry points. If data is altered, provenance flags it, preventing use of compromised info.
It supports incident response: Track breach sources, affected data, and spread. In AI and big data, it ensures models aren’t poisoned.
Provenance uses graphs or logs, like PROV model, linking entities, activities, and agents. Tools like blockchain add immutability.
In ransomware context, it counters integrity attacks by verifying data history.
For implementation tips, check CSIRO’s research on provenance.
Strategies to Ensure Data Provenance
To implement provenance, start with logging: Capture all data interactions using tools like Apache NiFi or custom scripts.
Use standards like W3C PROV for structured records. Integrate with SIEM systems for real-time monitoring.
Blockchain for tamper-proof provenance—each change is hashed and linked.
In cloud environments, use AWS Provenance or similar services.
Challenges: Overhead can slow systems, so optimize with sampling. Privacy—anonymize sensitive parts.
Best practices:
- Automate capture at source.
- Verify with digital signatures.
- Audit regularly.
- Train teams on provenance tools.
This ties back to triple extortion by ensuring stolen data’s origin is traceable, aiding forensics.
Credit: Astera via astera.com
See our data management strategies for related advice.
Best Practices for Overall Protection Against Triple Extortion
Layer your defenses. Start with employee training—phishing simulations cut risks by 70%.
Implement zero-trust: Verify every access. Use EDR (Endpoint Detection and Response) for anomaly detection.
Patch promptly; vulnerabilities like Log4j are exploited fast.
Network segmentation limits spread.
Cyber insurance covers ransoms, but don’t rely on it—focus on prevention.
Incident response plan: Test it yearly.
Monitor dark web for leaked data.
For small businesses, affordable tools like free antivirus and cloud backups work.
Link to CISA’s StopRansomware guide for official advice.
Future Trends in Ransomware and Extortion Tactics
Looking ahead, expect more AI-driven attacks—automated phishing, faster exfiltration.
Quadruple extortion might become standard, with media and regulator involvement.
Ransomware targeting IoT and supply chains will rise.
Defenses? AI for detection, quantum-resistant encryption.
Regulation like mandatory reporting will help.
Stay updated via Checkpoint’s ransomware hub.
Conclusion
Triple extortion ransomware evolution has made cyber threats more complex, but with solid backups and data provenance, you can fight back. Protect your data, train your team, and stay vigilant. If hit, don’t pay—report to authorities. By following these steps, you’ll reduce risks and keep your operations running smooth.
Share this content:













Post Comment