How Cloud Security Protects Businesses from Data Breaches in 2025
Modern busine is now founded on cloud computing. From file storage to larger operation systems, almost everything now runs on the cloud. It assists the companies to labor quicker, reduce expenses and remain in touch with any part of the world. However, as a greater amount of data is transferred to the Internet, the dangers increase as well.
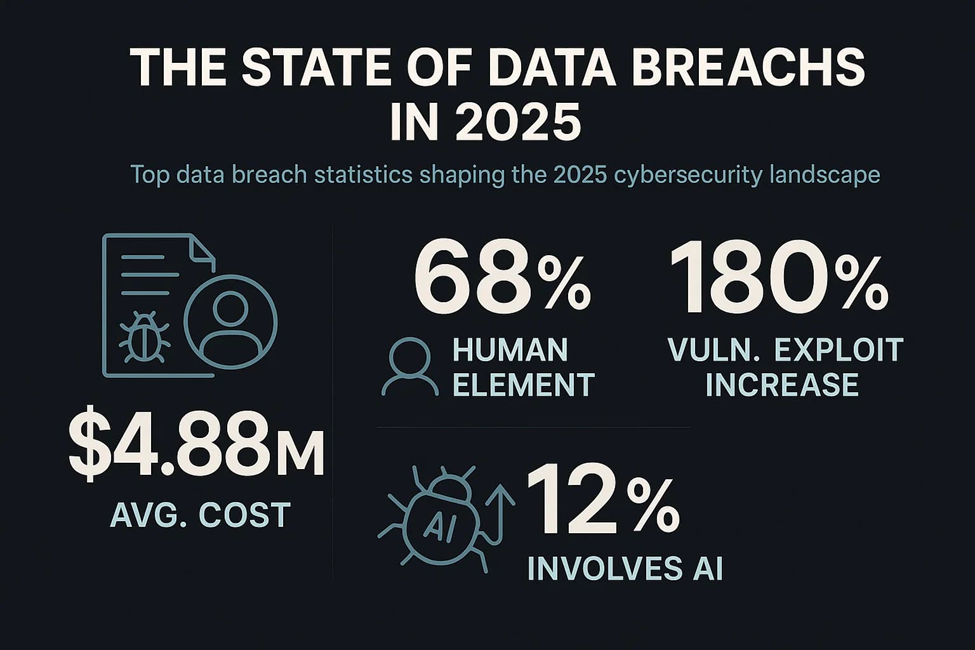
Cybercriminals are becoming more intelligent and organized. They are also use modern tools, automation and even artificial intelligence to discover security gaps.
In the year 2025, data breach is not just common, but also more advanced, fast, and difficult to detect. That is why cloud security is not optional any more, it is a necessity. Cloud security is not only effective in blocking hackers, but also in real time detecting and responding to the threats. In this guide we shall believe in how cloud security can save businesses to data breaches in the year 2025.
What Makes 2025 Riskier for Business Data?
The threats of cyber in 2025 are greater than ever. Cloud environments are the best targets since they have extensive valuable information. Recent reports indicate that nearly forty-five percent of data breaches currently occur in the cloud-based systems. The top causes are misconfigurations, poor passwords and poor access control.
Thieves do not steal information anymore. They also corrupt the backups, ransom, or sell business information online. Any violation will cost millions to recover and lost trust.
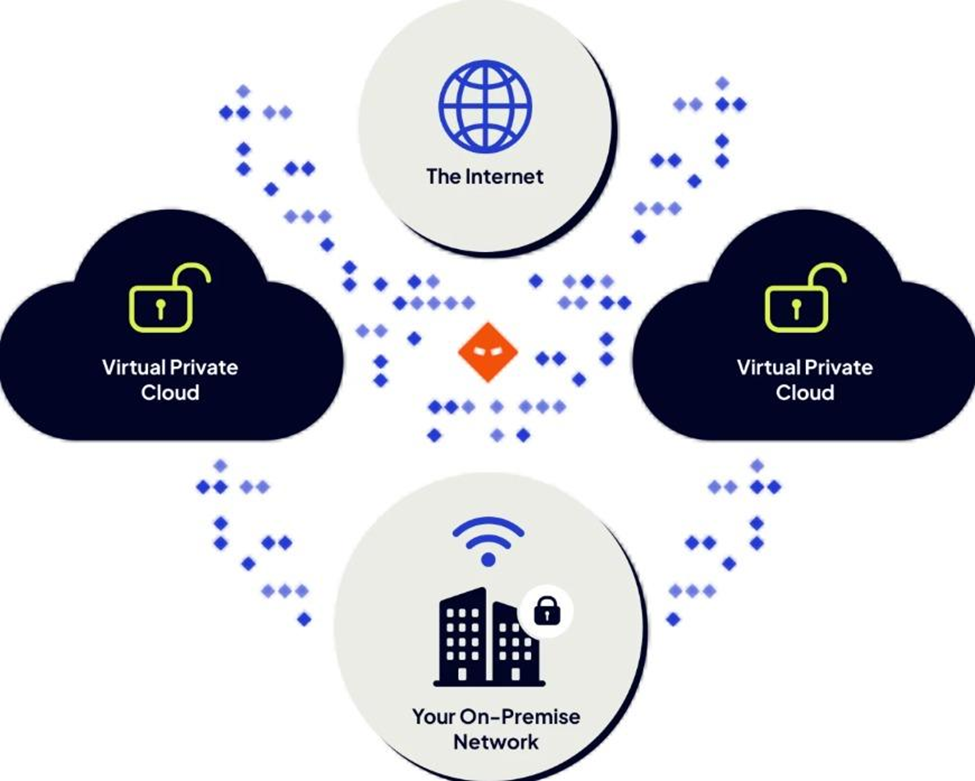
The risk is even higher with businesses that have multiple cloud providers in multi-cloud systems. Security management in various platforms is not easy and it may have loopholes. That is why it is the first step to achieve better protection to understand these threats.
What Is Cloud Security and How It Works
Cloud security is a combination of instruments, procedures, and regulations that defend the cloud information, applications, and networks. It doesn’t just block hackers. It also assists businesses to regulate access to information and files that are sensitive and remain secure. Cloud security is based on a shared responsibility. This implies that the cloud provider maintains the infrastructure, although the business is required to safeguard its data and access by the user.
Major coponents of cloud security are:
- Identity and Access Management (IAM): Fing who has access to the system.
- Encryption: It protects both the information during transit and storage.
- Tracking software: Monitor and identify suspicious behavior.
- Firewalls and security policies: block malicious connections.
When these layers work together, they create a strong defense against breaches.
The role of Cloud Security in Data Breach Protection of Businesses
Multi-factor authentication and strong identity controls are employed in cloud security. This complicates hacker intrusion even in case they receive a password. The encrypted information appears in the form of random code to any person who does not possess the key to unlock the code. Thus, even in the event of stolen data, it will be of no help to attackers.

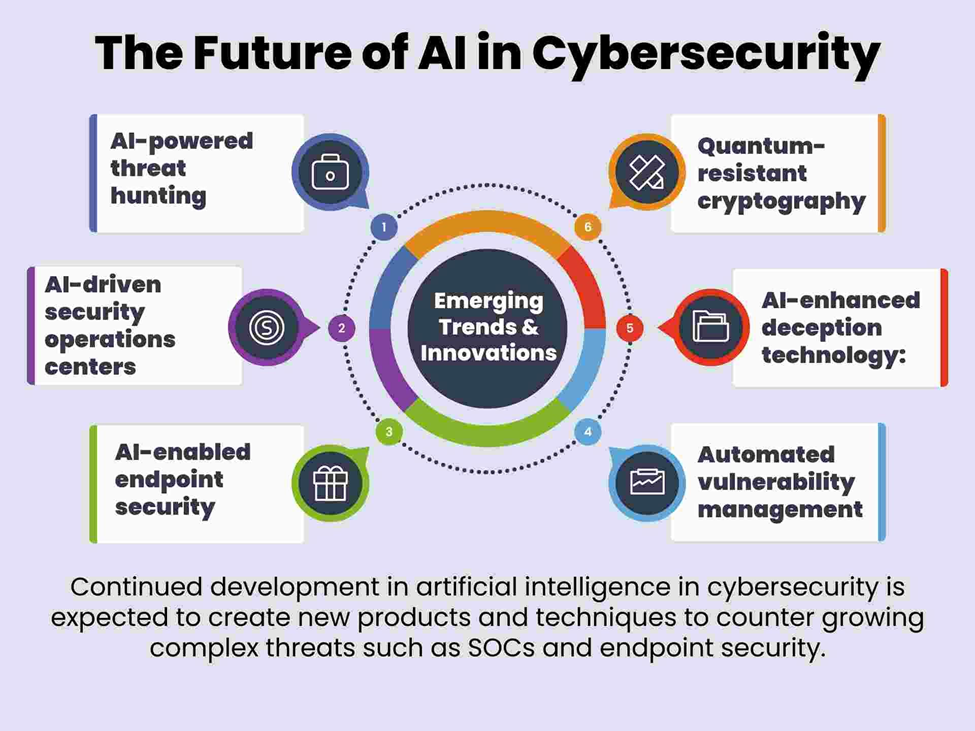
In the case of modern clouds, AI is employed to identify suspicious activity in real time. Notices can assist companies to take action before a leakage. The cloud systems automatically store information in secure sites. Companies can easily recover clean copies even when an attack has taken place.
Laws such as the GDPR and HIPAA need strict protection for data. Cloud security assists the businesses to remain compliant and not to face hefty fines.
Simply stated, cloud security ensures the security of hackers and information. It has the potential to lower downtime and expenditures and carry an adverse impact on business.
Key Cloud Security Strategies for 2025
Cloud data security needs to have a strategy. Some of the strategies any business should implement this year are highlighted below.
1. Implement Stringent Access Control.
Only authorized individuals should access business data. Also, multi-factor authentication and least privileges to the user should be assigned.
2. Encrypt Everything
Encryption of the file and then storage or sharing should always be taken. Secure data on-demand and encrypt data on-the-fly.
3. Detect and Review Constantly
Detect these misconfigurations and prevent them within a short period of time. You can use tools like Cloud Security Posture Management.
4. Automate Jobs Relate to Security
The automation aids in responding and detecting attacks more quickly. AI is now used in responding to real-time within many 2025 cloud systems.
5. Employee Training
Most of the breaches still occur via human error. Frequent training keeps the teams informed about phishing and other unsafe practices.
Top Cloud Security Mistakes to Avoid
Despite the excellent tools, it is still possible that businesses commit certain errors that allow hackers to enter the institution. Here are the biggest ones:
- Misconfigured Storage Buckets: One of the primary reasons of leaks lies in the accidental publicity of cloud storage.
- Weak Passwords: Using simple passwords can make you accounts easy targets.
- Absence of Visibility: Without observing, unsure behavior often goes unnoticed.
- Avoid Software Updates: Outdated apps have known flaws that attackers can easily use.
- Weak APIs:Most cloud systems make use of APIs which require strong authentication.
These problems can be identified through a mere audit. Their repair at an early stage can help avoid severe losses in the future. In 2025, experts predict that the cloud security failures will occur 99 percent on the user end, rather than on the provider. Regular checks are important, therefore.
Future Cloud Security Trends in 2025 and Beyond
There is constant evolution of technology and threats. Some of the trends that will define cloud security in 2025 are listed here:
AI-Driven Security:
Attacks can now be detected and blocked by AI quicker than by humans. It does learning based on data patterns to prevent threats.
Zero-Trust Architecture:
Increasing numbers of businesses are becoming zero-trust frameworks where default trust is not given to anyone. All users and devices are required to identify.
Multi-Cloud Management:
There are different cloud platforms that companies are utilizing. Poorly integrated and secured tools are sought after.
DevSecOps Integration:
There is a new working relationship between developers and security teams that aim to identify and address any issues at an early stage in the software lifecycle.
These trends indicate that the cloud security is currently changing rapidly and those businesses that adapt quickly will remain secure.
Conclusion
Cloud computing makes businesses fast, scaled and flexible. However, in the absence of robust security, it poses some grave dangers. The key to the safety of data, maintaining trust, and addressing global compliance standards is the safety of clouds.
In 2025, it is not only intelligent to invest in improving cloud security equipment and training. It is necessary. Companies that take action will not experience expensive data breaches and will secure their future. So, review your current setup. Strengthen your defenses. And may cloud security be the online armor that your business requires to be safe.
FAQs
What is the largest security threat of cloud security in 2025?
The greatest risk is AI-driven cyberattacks that will be able to attack weak points much quicker than ever. Companies require AI-based security systems to retaliate.
Is sensitive business data safe with cloud storage?
Yes, provided that you can rely on trusted cloud providers with encryption, MFA and ISO 27001 or SOC 2 compliance certifications.
How many times should a business update healthcare cloud system?
Security systems are supposed to be revised on a regular basis at least once every quarter or upon the discovery of new threats.
Why are cloud security in the industries the most beneficial?
All industries are benefited but particularly finance, healthcare and e-commerce wherein sensitive data is stored on daily basis.
Are small businesses able to afford cloud security?
Yes. Enterprise-level protection is affordable and available to small businesses due to most cloud platforms having affordable and scaling plans.
Share this content:














Post Comment